Qinrun Dai
23 posts
Qinrun Dai
@2st___
CTF Player @ L3H_Sec / OIer / System Security / Exploitation / CS PhD Student
Katılım Haziran 2020
128 Takip Edilen215 Takipçiler
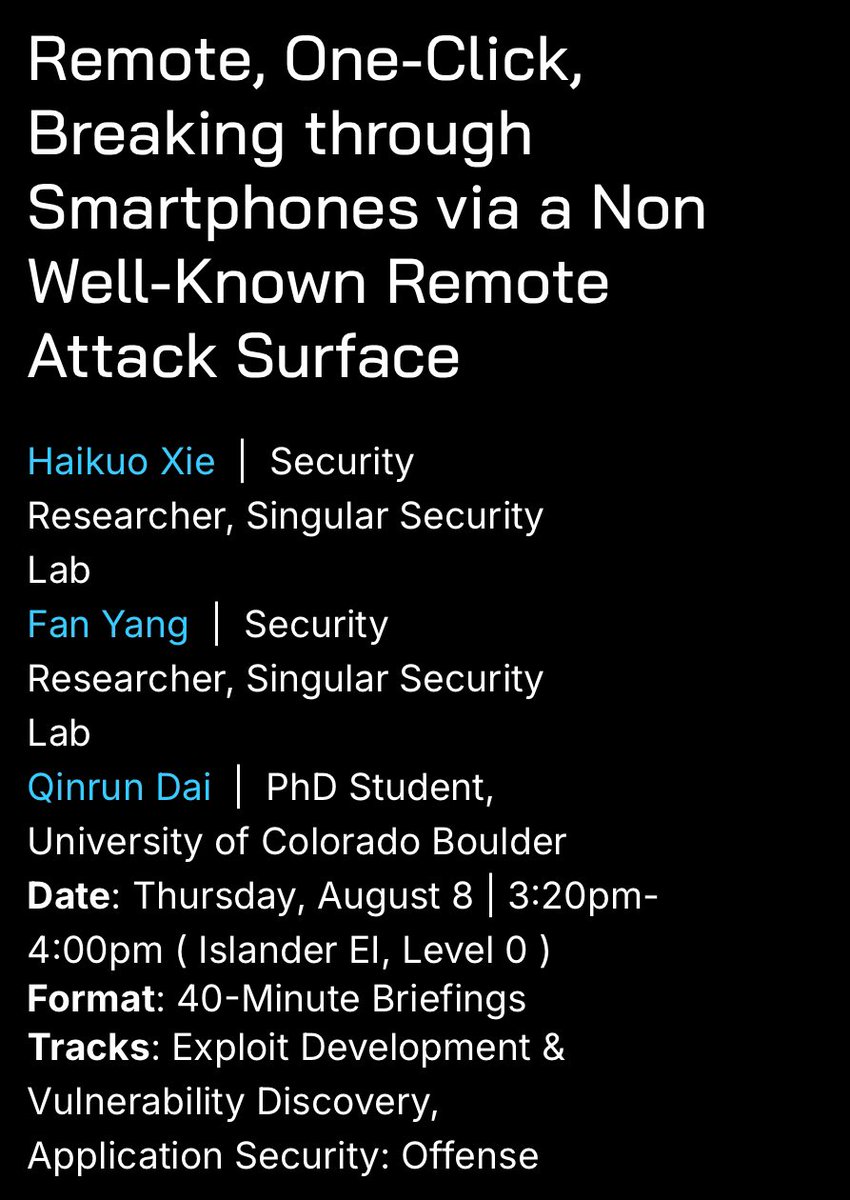
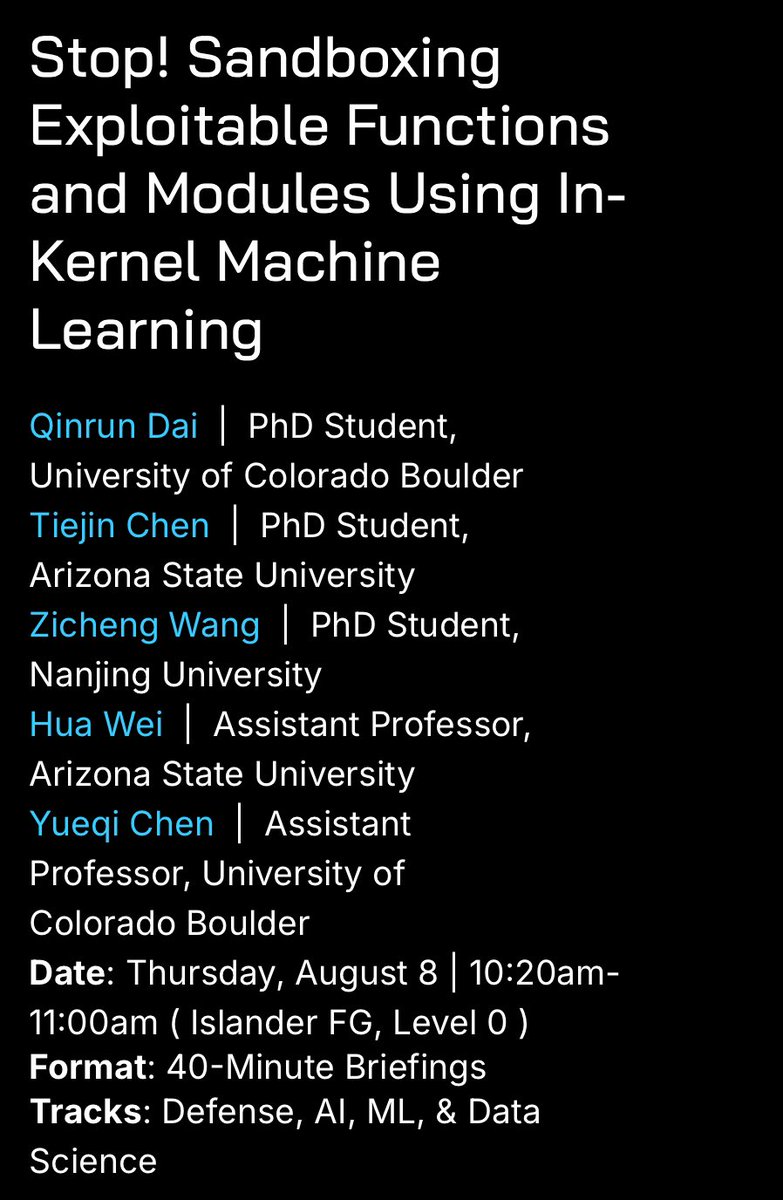
I’m honored to be here at #BHUSA 2024 to deliver my talks about 1 click RCE on smart phones and machine learning into kernel on-the-fly quarantine!

English
Qinrun Dai retweetledi

Boulder faculty and students are pround of being part of the 42-b3yond-6ug team. Now, take a shot at the meaning of the team name.
DARPA@DARPA
Congrats to the 7 companies that will receive $1 million each to develop AI-enabled cyber reasoning systems that automatically find and fix software vulnerabilities as part of the #AIxCC Small Business Track! Full announcement: darpa.mil/news-events/20….
English
Qinrun Dai retweetledi

Do you use a virtual machine to browse dangerous links safely? If you use the Chrome browser inside that virtual machine, is it secure enough?
As you might have guessed, the answer is not so much.
We chained six unique CVEs from 2023 listed below.
• Chrome Renderer RCE : CVE-2023-3079
• Chrome Sandbox Escape : CVE-2023-21674
• LPE in guest OS : CVE-2023-29360
• VMware Info Leak : CVE-2023-34044
• VMware Escape : CVE-2023-20869
• LPE in host OS : CVE-2023-36802
English
Qinrun Dai retweetledi

Uploaded all my Offensive Security & Reverse Engineering (OSRE) course labs (docx) to my repo found below. Most of them have very detailed instructions and should be great to get you started in Software Exploitation. 1/n
#Offsec #SoftwareExploitation #RE
exploitation.ashemery.com

English
Qinrun Dai retweetledi

How to Reverse and Exploit iOS for BEGINNERS😈
👇My 3 part series👇
Part 1: How to Reverse & Patch iOS Apps
bit.ly/3inJgop
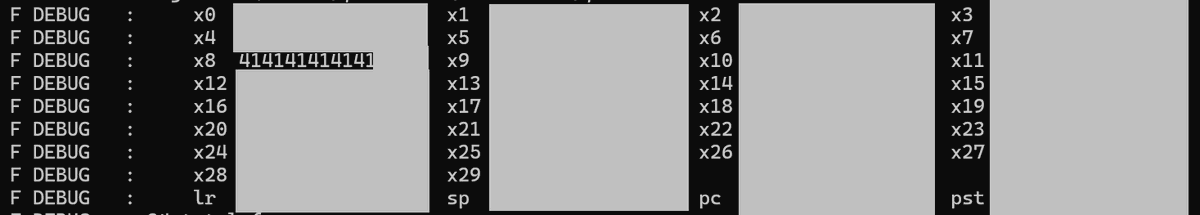
Part 2: Exploiting iOS binaries: ARM64 ROP Chains
bit.ly/3BgvLxt
Part 3: Heap Overflows on ARM64: Spraying, UAF
bit.ly/3gGI7rx
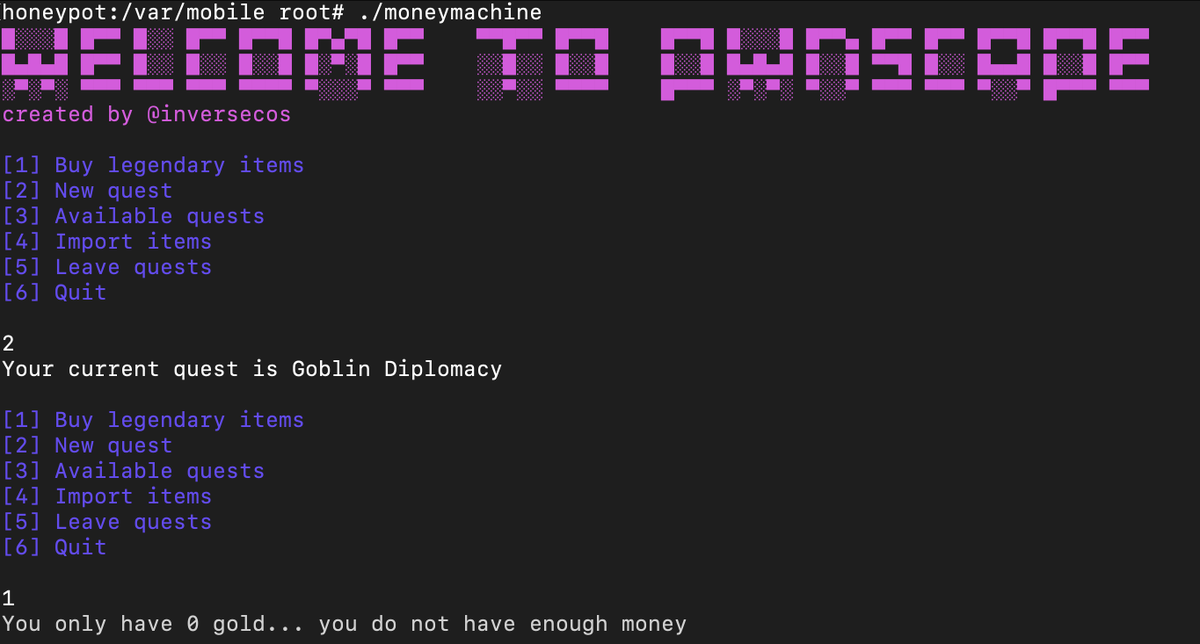
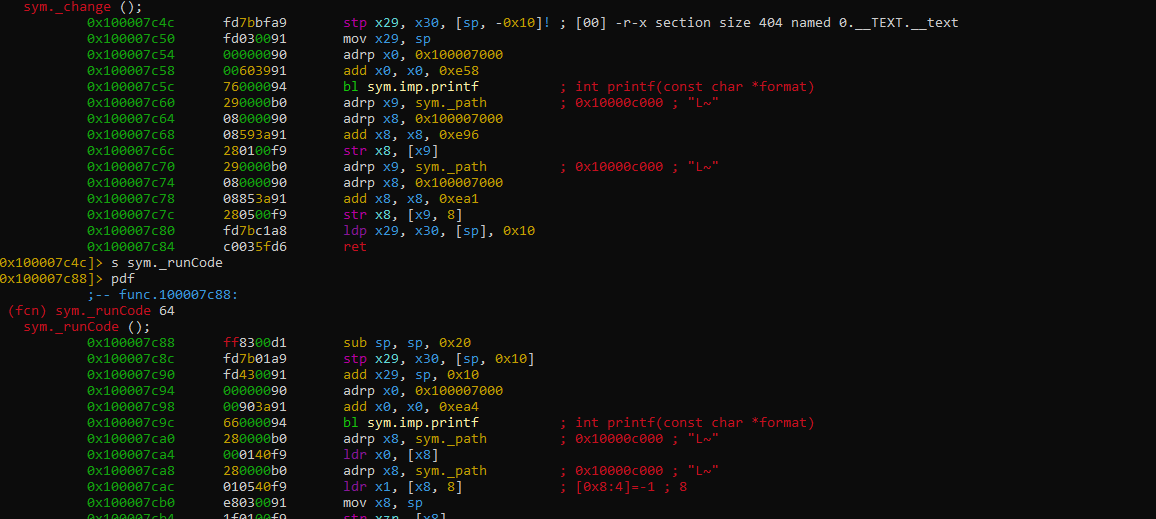
English
Qinrun Dai retweetledi

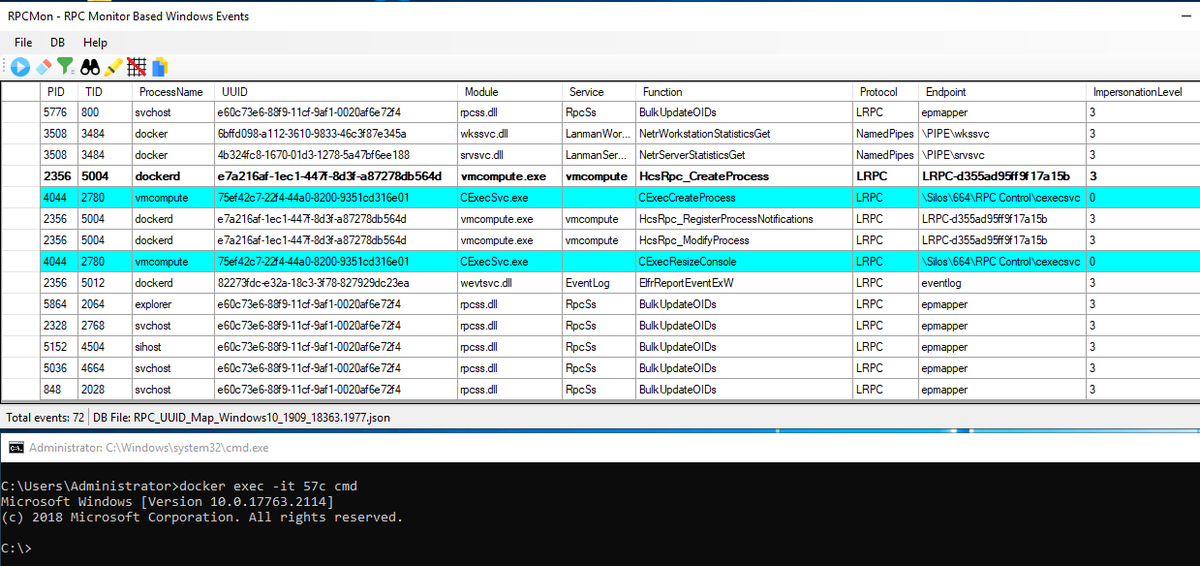
Check out our new blog post about analyzing the #RPC communication between #Windows #container to the host. 😃
cyberark.com/resources/thre…
We also released a new tool named #RPCMon to show RPC calls with functions names:
github.com/cyberark/RPCMon
(1/2)
#malware #redteam #Pentesting
English