3DOↃ Security
94 posts


3DOↃ Security
@3DOCsec
Cyber entomologist | warden, judge, Zenith @code4rena | FV ambassador @Certora













164,000 employees and this “this update introduces 8 new emojis”

Opsek is growing: we are looking for the best talent obsessed with Cybersecurity and blockchain technology. If you are, drop me a dm. btw, we don't work with anons, camera always on.

Last year, @neumoXX and I (hunting as Pai Mei & Gandalf) discovered and disclosed a very plausible phishing attack on the most common NFT contract in the @Stacks ecosystem. At its heart, it's due to the way authentication is commonly implemented in Clarity contracts. But it turns out the authentication method is known and accepted by the Stacks ecosystem, even though it's been debated for many years. We aren't convinced that it's safe enough. So we've written a blog post about it with the sincere hope that it sparks wider discussion. It's time the debate moved beyond GitHub Issues and gets much more exposure. 100proof.org/a-questionable…


In November, I submitted a critical bug to Cronos (@cronosapp) which they downplayed and have since been kicked off Immunefi. Here's some info about the bug and an example of how projects can simply not pay a fair amount. Report: gist.github.com/fatherGoose1/6… tl;dr: - It's a simple staking contract where you stake your TONIC and receive xTonic at the current exchange rate. - The vulnerability lies in a function called performConversionForERC20() which allows anyone to convert other tokens held by the contract into TONIC. - This function is vulnerable to reentrancy because the caller sets an arbitrary swap path and can inject a malicious token in the middle to gain control of execution. - The contract determines the estimated amount of TONIC that should be received by the swap, and any extra goes to the caller as a reward. - But since there is reentrancy, the caller can also STAKE their TONIC prior to the above function completion. - The caller's stake is honored AND they are transferred back their TONIC, essentially receiving free staked tokens. Caveat: There is a 10 day unstaking delay. So the exploiter would not be able to actually convert the staked tokens back into TONIC until the cooldown period had passed. What Cronos said: Thank you for reporting this issue. The team has verified that the exploit described can indeed work. From our side, we have safeguards in place to mitigate these risks; such as a 10 days delay period for the xTonic minted. As such, there is a low possibility of the exploit realising; as the issue will be rectified before the exploiter can launder the gotten funds. However, we do appreciate your effort in identifying this issue and plan to update the contract to eliminate the risk entirely. In addition, we are happy to reward you with USD1,600 as a token of appreciation. Actions: Cronos fixed the vulnerability immediately, before even responding to the report. My thoughts: Obvious lowball. Cronos's max bounty was $250,000 and they offered $1,600. I understand the technicality with this attack, and would have agreed to a payout less than the max, but the payout would have to accurately represent the value of this report. Mediation: Immunefi mediated twice and confirmed that this report deserved the max bounty. Immunefi told Cronos that a simple unstaking delay is not an adequate means of protection. Cronos claimed: "We have implemented a robust monitoring framework, consisting of internal systems, protocols, and strategic third-party partnerships, which promptly respond to any anomalies within our smart contracts. This is the standard of any big organization, and we refrain from disclosing further specifics to maintain the integrity of our security protocols." When Immunefi asked them to provide any information regarding their automated detection and mitigation processes, Cronos would not comply. Result: Cronos was kicked off Immunefi. Final thoughts from Django: 'Tis the life of a bug hunter.



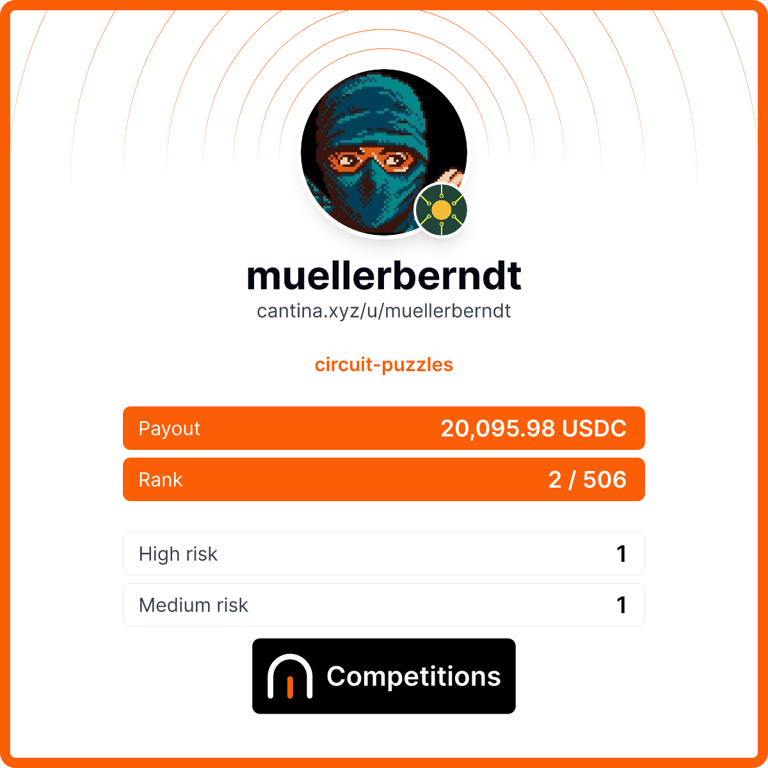
The results of the $80,000 Initia Cosmos competitive audit are in! Congratulations to everyone who submitted valid findings, especially to @bernd_eth for securing over half of the total prize pool along with 7 solo high-risk findings submitted! Much respect to @initia for their unwavering commitment to the highest security outcomes. Full list of winners in thread 👇