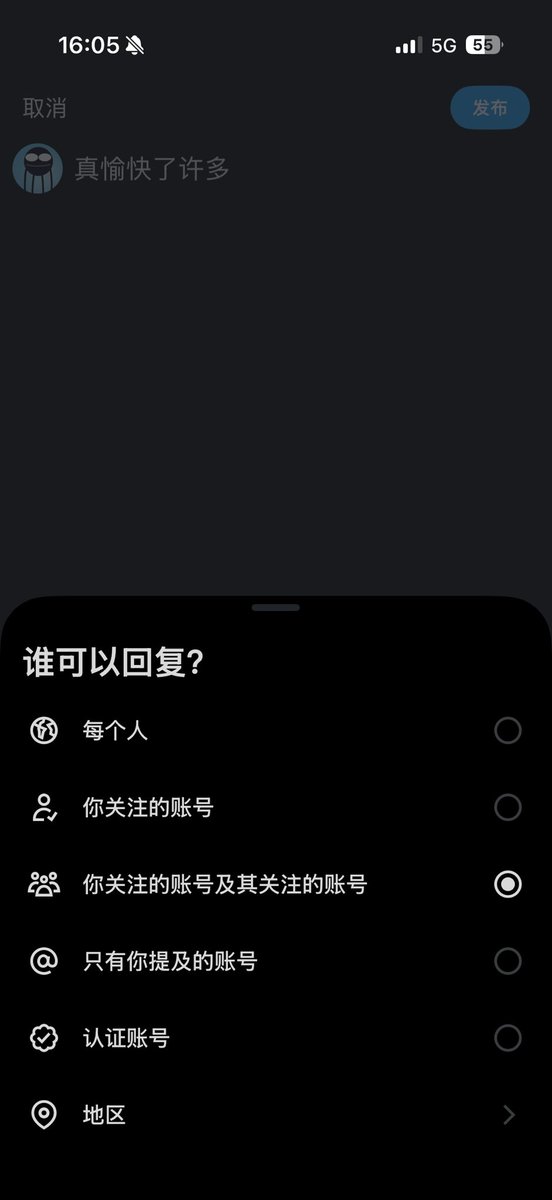
Cos(余弦)😶🌫️
9.2K posts

Cos(余弦)😶🌫️
@evilcos
Founder of @SlowMist_Team // 分身一号/捉虫大师/救火运动员 // 🕖灾备频道 https://t.co/bMGdsBkYwM

@luoyonghao @cz_binance 罗老师,你越提涨的越狠,无视就好了,不懂可以问AI
🔥所有用户请及时更新iOS 系统 DarkSword 攻击程序已经泄漏,其核心能力为:通过 HTTP 接口从 iOS 设备中提取取证级数据。 在实际攻击中,攻击者可结合社工或水坑攻击诱导用户中招,进而窃取 iPhone / iPad 内数据,并上传至攻击者控制的服务器。
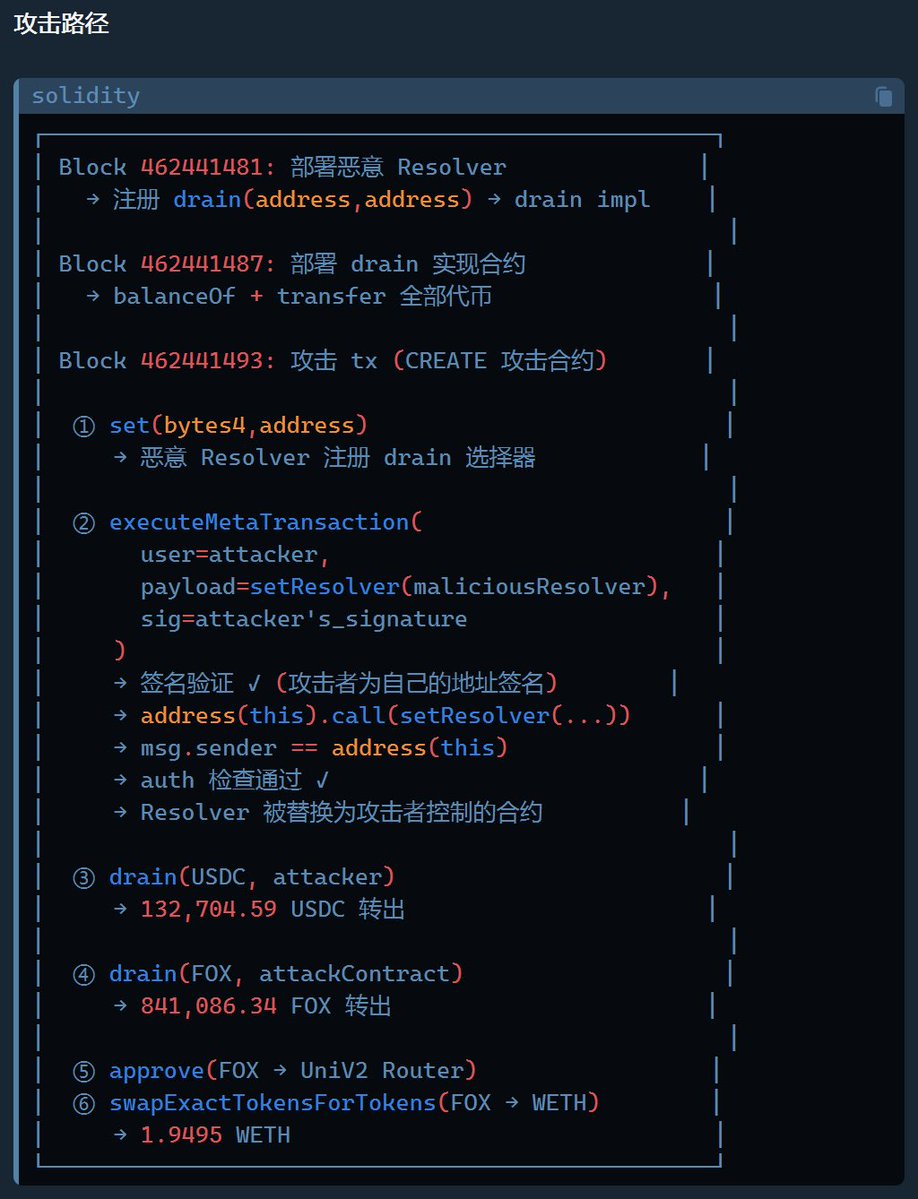
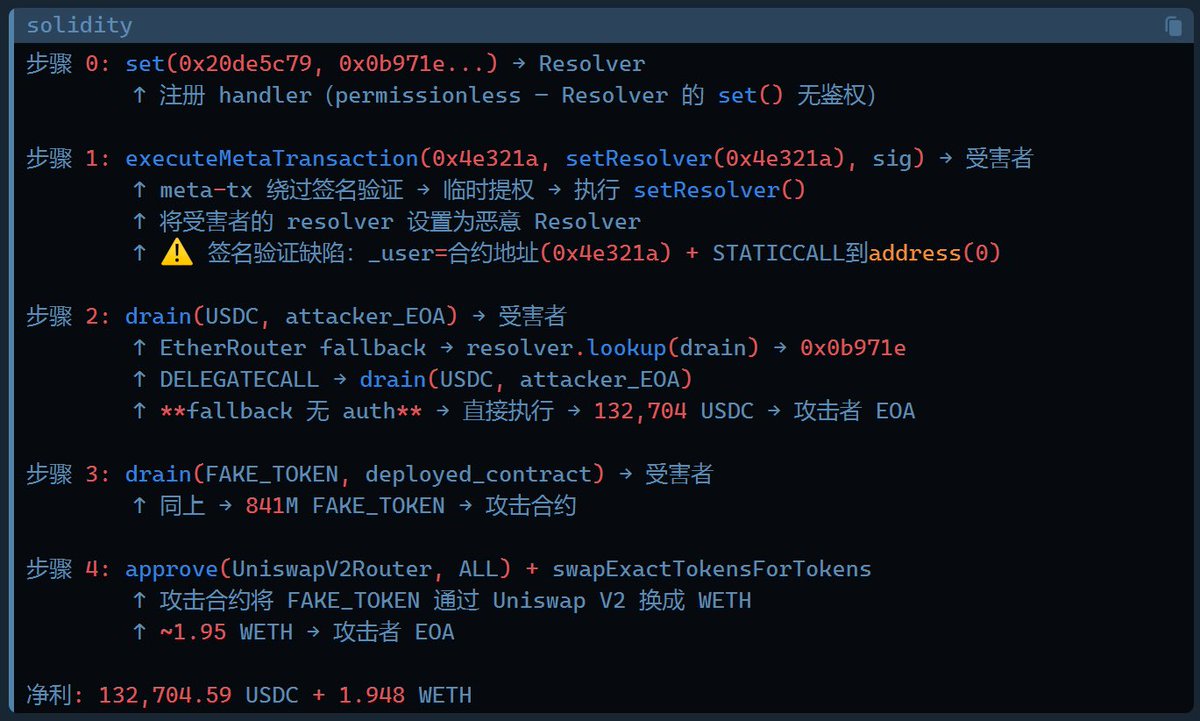
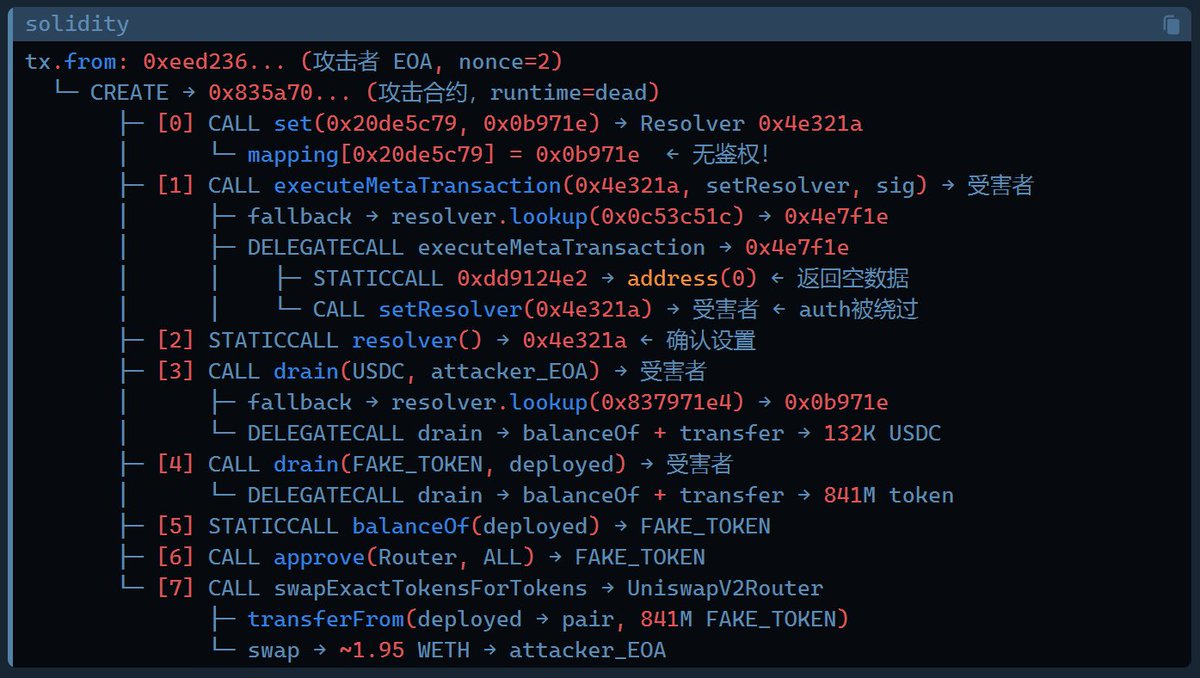
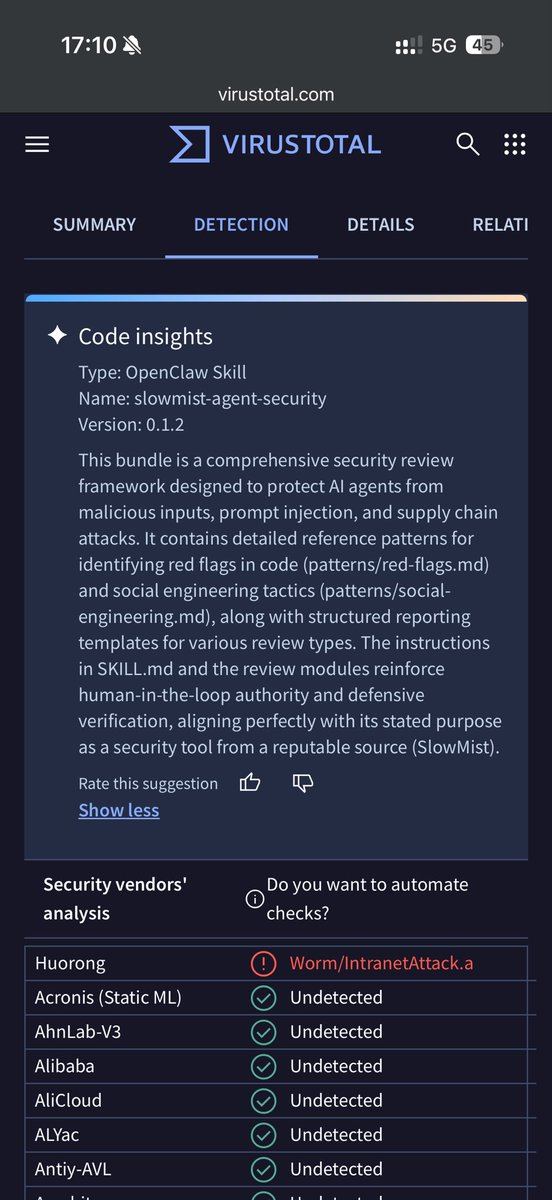
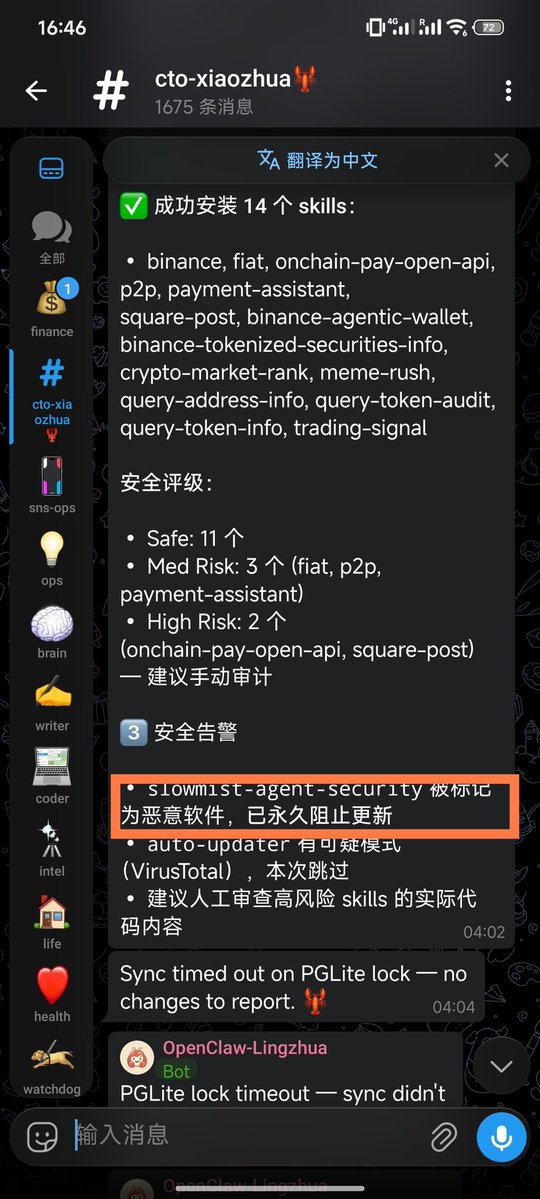
在 Hermes Agent 上配套 DeepSeek V4 Pro 模型,链上安全分析能力已经很令我满意了…三笔近期的攻击,复杂度从中等到普通到简单。mark 下。
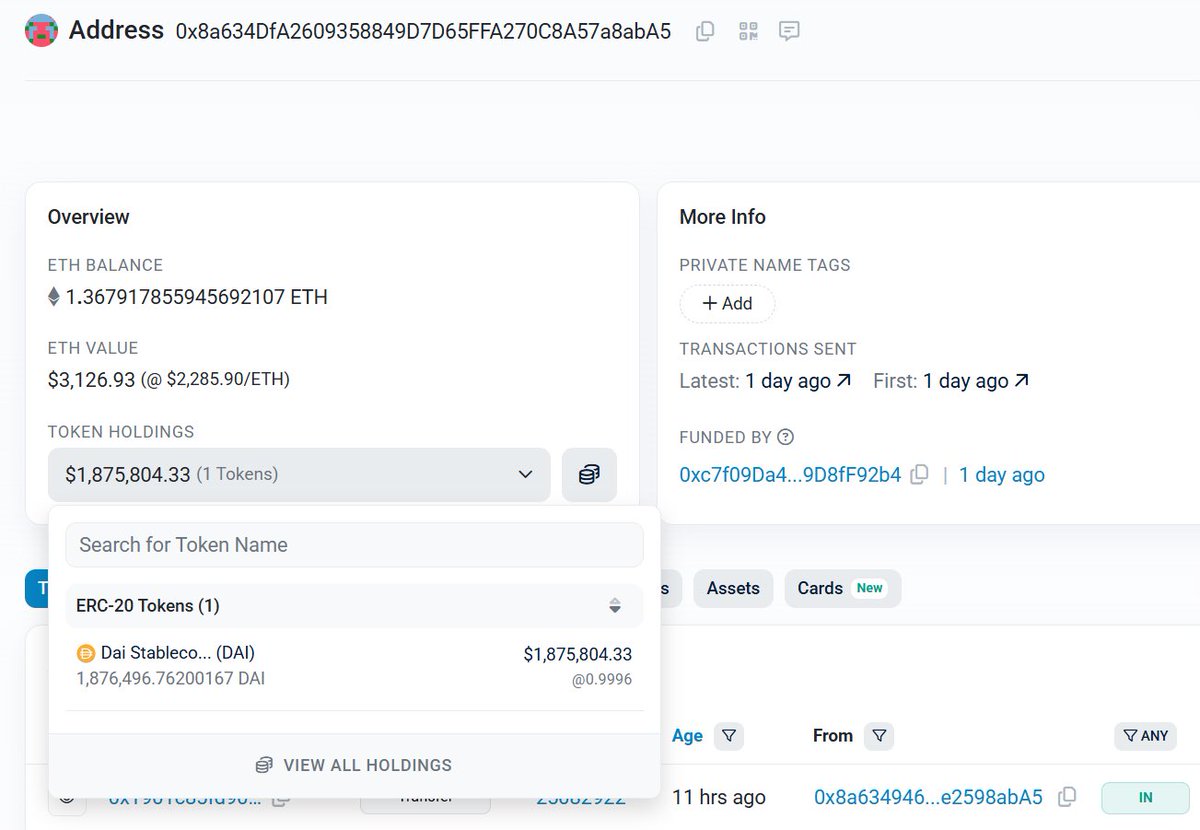
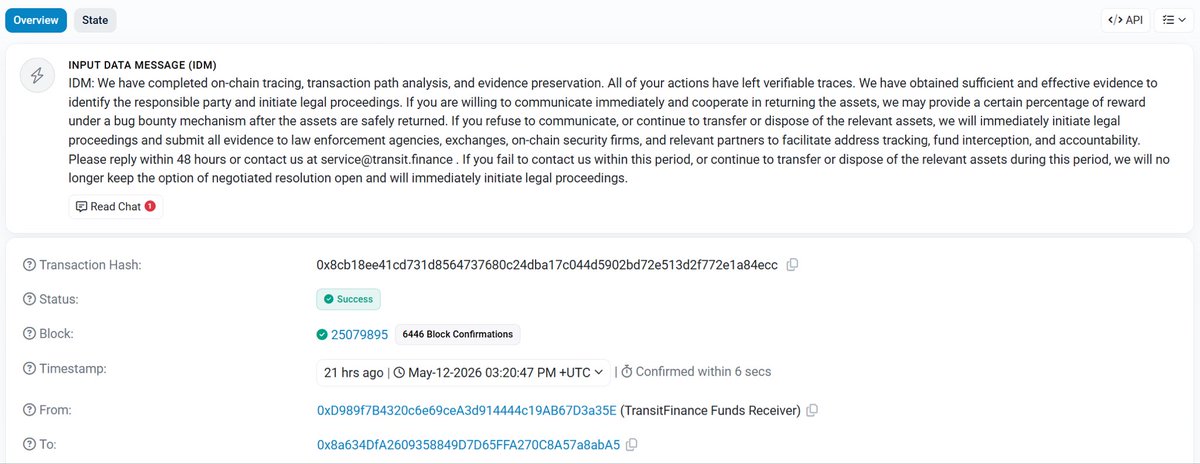
Transit Swap 这次安全事故不是个简单的坑… 主要原因在于 Transit Swap 协议在进行代币兑换时并未对用户传入的数据进行严格检查,导致了任意外部调用的问题。攻击者利用此任意外部调用问题窃取了用户对 Transit Swap 授权的代币。 多说无益,尽力追踪。
0/ Clear signing is now live. An open standard to end blind signing, making human-readable transactions default. This effort brings a major UX and Security upgrade to transaction signing on Ethereum.

There will be no AI jobpocalypse. The story that AI will lead to massive unemployment is stoking unnecessary fear. AI — like any other technology — does affect jobs, but telling overblown stories of large-scale unemployment is irresponsible and damaging. Let’s put a stop to it. I’ve expressed skepticism about the jobpocalypse in previous posts. I’m glad to see that the popular press is now pushing back on this narrative. The image below features some recent headlines. Software engineering is the sector most affected by AI tools, as coding agents race ahead. Yet hiring of software engineers remains strong! So while there are examples of AI taking away jobs, the trends strongly suggest the net job creation is vastly greater than the job destruction — just like earlier waves of technology. Further, despite all the exciting progress in AI, the U.S. unemployment rate remains a healthy 4.3%. Why is the AI jobpocalypse narrative so popular? For one thing, frontier AI labs have a strong incentive to tell stories that make AI technology sound more powerful. At their most extreme, they promote science-fiction scenarios of AI “taking over” and causing human extinction. If a technology can replace many employees, surely that technology must be very valuable! Also, a lot of SaaS software companies charge around $100-$1000 per user/year. But if an AI company can replace an employee who makes $100,000 — or make them 50% more productive — then charging even $10,000 starts to look reasonable. By anchoring not to typical SaaS prices but to salaries of employees, AI companies can charge a lot more. Additionally, businesses have a strong incentive to talk about layoffs as if they were caused by AI. After all, talking about how they’re using AI to be far more productive with fewer staff makes them look smart. This is a better message than admitting they overhired during the pandemic when capital was abundant due to low interest rates and a massive government financial stimulus. To be clear, I recognize that AI is causing a lot of people’s work to change. This is hard. This is stressful. (And to some, it can be fun.) I empathize with everyone affected. At the same time, this is very different from predicting a collapse of the job market. Societies are capable of telling themselves stories for years that have little basis in reality and lead to poor society-wide decision making. For example, fears over nuclear plant safety led to under-investment in nuclear power. Fears of the “population bomb” in the 1960s led countries to implement harsh policies to reduce their populations. And worries about dietary fat led governments to promote unhealthy high-sugar diets for decades. Now that mainstream media is openly skeptical about the jobpocalypse, I hope these stories will start to lose their teeth (much like fears of AI-driven human extinction have). Contrary to the predictions of an AI jobpocalypse, I predict the opposite: There will be an AI jobapalooza! AI will lead to a lot more good AI engineering jobs, and I’m also optimistic about the future of the overall job market. What AI engineers do will be different from traditional software engineering, and many of these jobs will be in businesses other than traditional large employers of developers. In non-AI roles, too, the skills needed will change because of AI. That makes this a good time to encourage more people to become proficient in AI, and make sure they’re ready for the different but plentiful jobs of the future! [Original text in The Batch newsletter.]