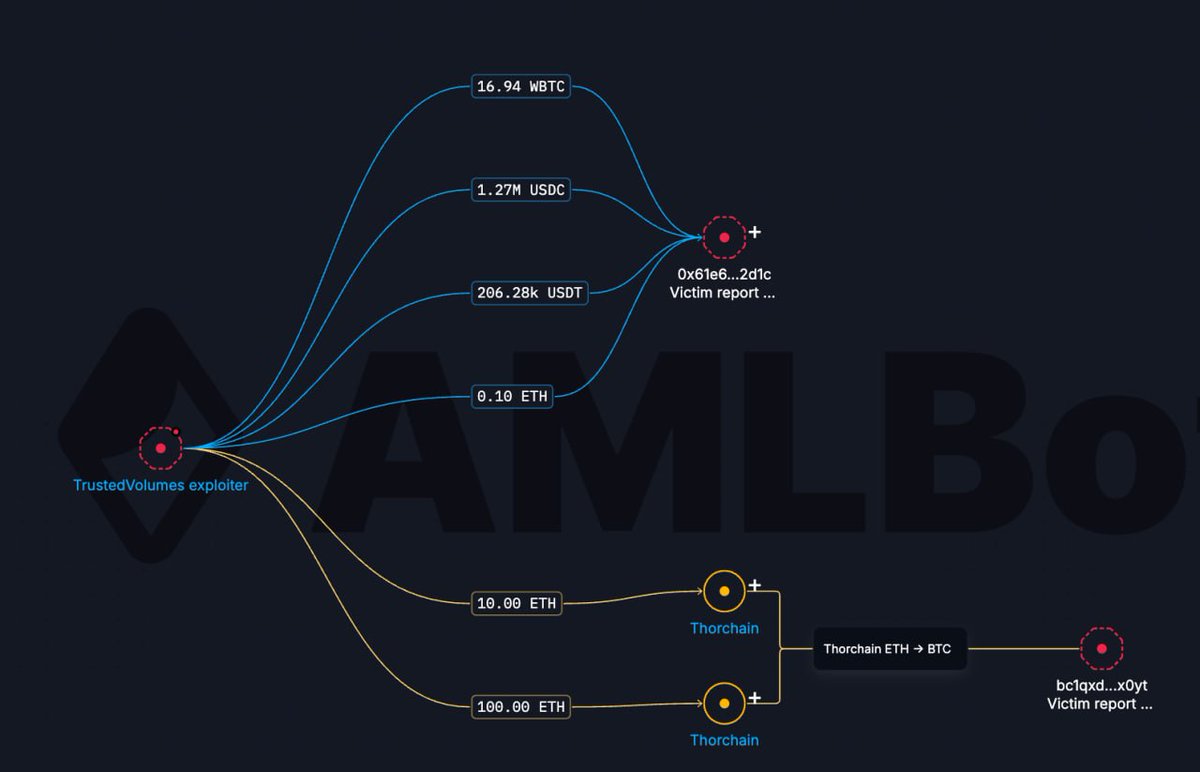
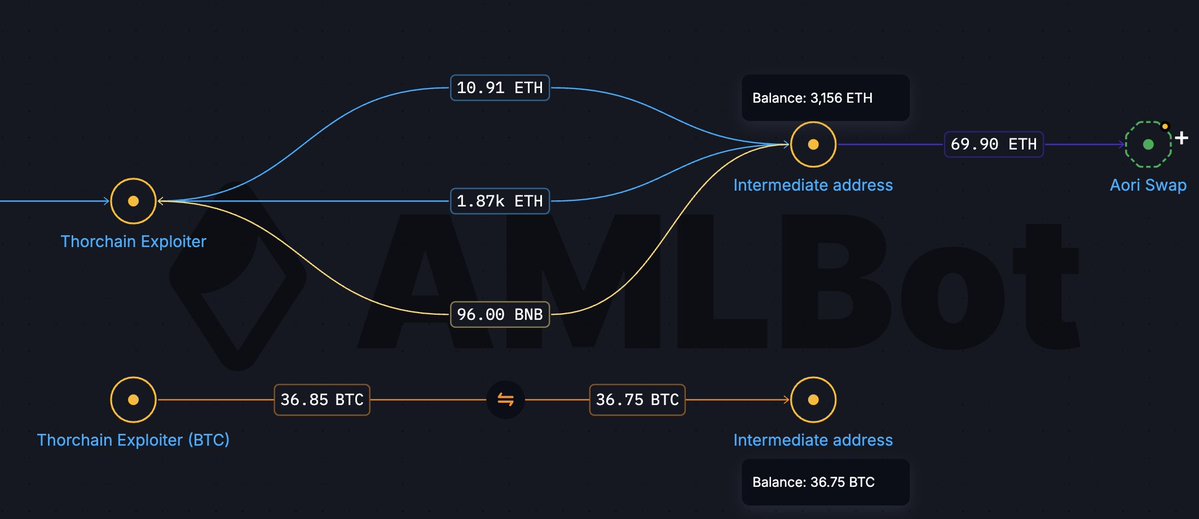
@zachxbt @solidintel_x Will attackers launder the stolen money via... THORChain? 😆
English
AMLBot
1.8K posts


@AMLBotHQ
Blockchain Intelligence at your fingertips. Report malicious crypto addresses here: https://t.co/VdIaZEqRBN





Another notable counterparty is Huione Crypto, a similar project that operated as a platform for money launderers and other illicit actors. This platform has received more than 70 billion USDT.