Sabitlenmiş Tweet
Danielle Aminov
123 posts

Danielle Aminov
@AminovDanielle
Threat researcher @wiz_io
Katılım Şubat 2019
180 Takip Edilen1.6K Takipçiler
Danielle Aminov retweetledi

Jenkins.. still building code, leaking secrets, and keeping security teams busy 😈
Merav@merav_br
My new research on the Jenkins threat landscape 🔍☁️ Exposed instances, deprecated plugins, CI/CD attack paths… and based on TeamPCP’s recent activity, I think they read it too 👀 wiz.io/blog/jenkins-t…
English
Danielle Aminov retweetledi

🚨 Meet "Dirty Frag": a new Linux kernel privilege escalation, fresh off the heels of Copy Fail.
Wiz Research is tracking CVE-2026-43284 and CVE-2026-43500 (also known as Copy Fail 2), discovered by Hyunwoo Kim (@v4bel). No official patches are out yet, and a public PoC already exists.
🔑 The technical bit:
A vulnerability chain in the ESP (IPsec) and RxRPC kernel subsystems, with two deterministic page-cache write primitives in the same spirit as Dirty Pipe. Ubuntu, RHEL 8/9/10, AlmaLinux, Fedora, openSUSE, and more are all affected.
🛡️ Slightly less risky for containers:
Exploitation usually requires CAP_NET_ADMIN, so hardened Kubernetes setups with default seccomp profiles are at lower risk. VMs and less restricted environments should still take this seriously.
🔧 What to do now:
Until patches drop, you can temporarily disable the vulnerable kernel modules (esp4, esp6, rxrpc). Full mitigation and detection guidance in the blog.
Wiz customers: pre-built queries and a live advisory are already in the Threat Intel Center. We'll keep updating both as more info comes to light.
Full research from Merav Bar and @ramimacisabird: wiz.io/blog/dirty-fra…

English
Danielle Aminov retweetledi
Danielle Aminov retweetledi

🎉 IT'S OFFICIAL: @wiz_io joins @Google to secure the AI era.
This is a massive moment for our customers and our team.
Thank you to every customer, partner, and Wizard who made this moment possible 💙
We can't wait to share what's next.
wiz.io/blog/google-cl…
English
Danielle Aminov retweetledi

@shahardorf & I found a phishing campaign abusing oauth applications in Entra in more than 50 organizations! And i promise you that in this blog we explain how you can do it too! And provide all the IOCs 🤭 It's one of these blogs i would enjoy reading!
#tldr-0" target="_blank" rel="nofollow noopener">wiz.io/blog/detecting…
English

I had the pleasure of speaking at @DistrictCon 🪩 in Washington, DC last weekend. It was my second time speaking at the conference - this time about another common misconfiguration in the cloud that should make you think twice. Power outage last year, snowstorm this year ❄️ once again, the hacker community showed up strong. What a community! great energy and brilliant people 🙌




English
Danielle Aminov retweetledi

Introducing my Bug Bounty Masterclass. 100% free.
I've made $2,000,000+ finding security bugs. I spent the last year turning my methodology into a complete blueprint.
4 hours of video - foundations, reconnaissance, web proxies, hands-on challenges, and certification.
Finish it in a weekend and start hacking real-world applications 🐞
English
Danielle Aminov retweetledi

We hacked the AWS JavaScript SDK, a core library powering the entire @AWScloud ecosystem - including the AWS Console itself 🤯
How did we do it? Just two missing characters was all it took.
This is the story of #CodeBreach 🧵👇

English

Excited to be returning to @DistrictCon for round two this month!
Back on stage again, presenting: Auths Gone Wild – When authenticated means anyone 🪩
Looking forward to another epic DistrictCon and great conversations around auth gone wrong 🔓

English
Danielle Aminov retweetledi
Danielle Aminov retweetledi

Here's our new blogpost with a technical deepdive into exploitation we're observing in the wild of CVE-2025-55182 (aka react2shell):
wiz.io/blog/nextjs-cv…

English
Danielle Aminov retweetledi

🚨 React2Shell (CVE‑2025‑55182) in‑the‑wild exploitation & deep‑dive analysis. Critical RCE across React 19, Next.js & all RSC frameworks. Patch now.
wiz.io/blog/nextjs-cv…

English

For the latest developments on React2Shell 👉wiz.io/blog/critical-…
English

With all the talk about the Next.js PoC, many people missed that the React2Shell vulnerability (CVE-2025-55182) affects the underlying RSC implementation itself. This means other popular frameworks that rely on RSC are also vulnerable. We are still analyzing the impact and ease of exploitation across additional platforms. For example, the commonly used Vite RSC plugin, when running with its default configuration, is also vulnerable with only minor modifications to the existing PoC. Patch your environments as soon as possible 🏃♀️

English

We were analyzing the new RSC vulnerability and its impact. RSC is a React feature, but most apps use it through Next.js, which bundles RSC widely. So it will likely surface most often as Next.js CVE-2025-66478. Patch snippet below 🧐 Initial analysis: wiz.io/blog/critical-…

English
Danielle Aminov retweetledi

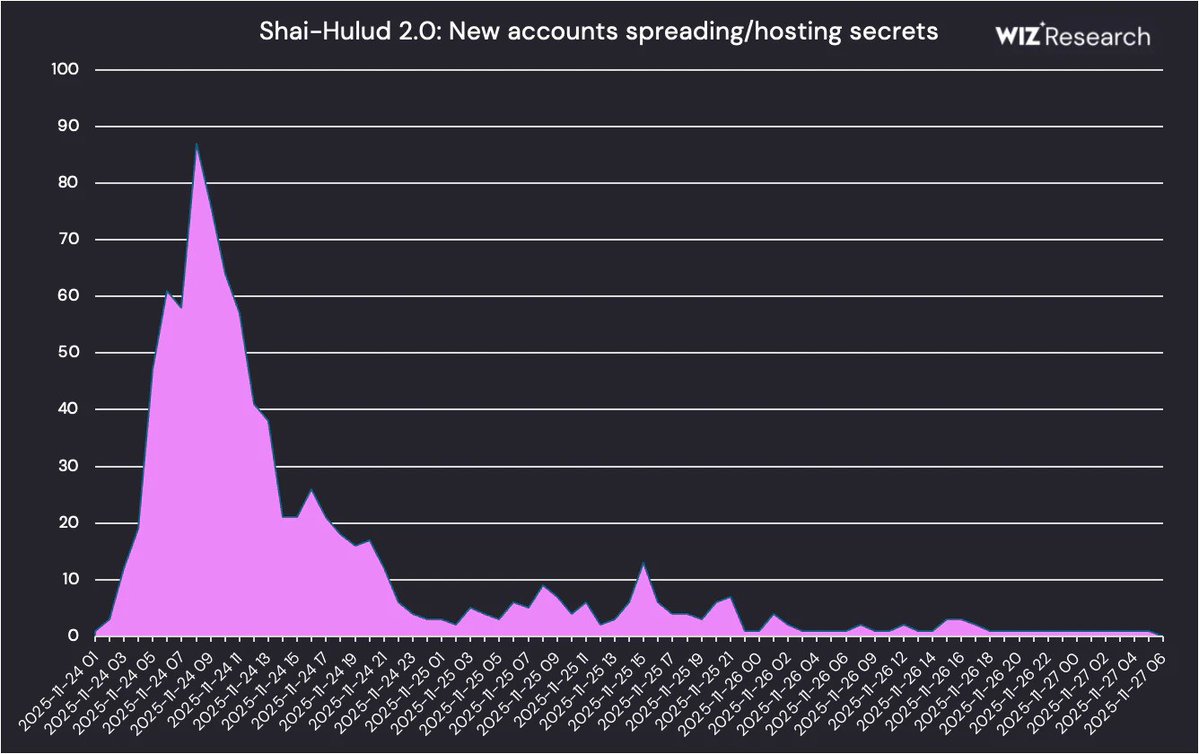
🪱sharing more on sha1-hulud w/@sshaybbc
* 2 packages == ~60% of infections
* 400k unique secrets in truffleSecrets.jsons, only 2.5% verified, & the majority of those short lived JWTs for GitHub Actions!
* 3/4 of impacted workloads were CI/CD, 1/4 were users
🔗below
English
Danielle Aminov retweetledi

WIZ ASM IS HERE!💥
Discover, validate & prioritize all your exposures cloud, AI, SaaS & on-prem. Context-driven ASM powered by Wiz Security Graph. Eliminate exploitable risk everywhere!
Ready to see Wiz ASM in action? 🥳 wiz.io/blog/introduci…
English
Danielle Aminov retweetledi
Danielle Aminov retweetledi