Andrew Chiles retweetledi
Andrew Chiles
1.1K posts


Andrew Chiles
@AndrewChiles
Works @ SpecterOps, Red Teamer, Amateur Photographer, Health Nut, Husband, Father, #wreckingball
Huntsville, AL Katılım Mart 2009
693 Takip Edilen2.3K Takipçiler
Andrew Chiles retweetledi

Want to write your own Nemesis enrichment modules? ✍️
@harmj0y and @tifkin_'s latest post covers module dev, Yara/Titus rule updates, and C2 connector design, including the new Claude Code/OpenAI Codex "easy mode."
Read more ⤵️ ghst.ly/4uapNIe
English
Andrew Chiles retweetledi

We fine-tuned an 8B model to pop a GOAD domain…using only synthetic training data. No real networks. No frontier model distillation. Just a world model that simulates AD environments and generates realistic pentesting trajectories.
See how @shncldwll and @0xdab0 did it: dreadnode.io/blog/worlds-a-…

English
Andrew Chiles retweetledi

Introducing BloodHound Scentry: BloodHound Enterprise + SpecterOps experts working alongside your team to eliminate attack paths and accelerate APM.
Level 0 → Level 3 maturity in ~6 months. Not theory. Tradecraft. 🎯
Learn more ➡️ ghst.ly/bhscentry-tw

English
Andrew Chiles retweetledi

My first blog post in a while. This was a fun one. The endpoint management agent belonging to Quest Desktop Authority had native support for DLL injection, thread token manipulation and elevated admin execution... all remotely from a low privilege user.
netspi.com/blog/technical…
English
Andrew Chiles retweetledi

Identity security in restricted environments shouldn’t be limited to periodic reviews.
BloodHound Enterprise on-premises enables continuous Identity Attack Path Management without cloud connectivity.
Learn more ➡️ ghst.ly/4bXPNQe

English
Andrew Chiles retweetledi

Hope to see you in Denver! V2 of SCCMHunter has some nice features including Kerberos support for the admin module now that Microsoft killed NTLM auth in the 2509 release
SpecterOps@SpecterOps
SCCM is everywhere, and still ripe for abuse. At #WWHF next month, @unsigned_sh0rt will walk through how to find, enumerate, and compromise SCCM environments using SCCMHunter — including a major upcoming update to the tool 👀 Don’t sleep on SCCM. 👉 ghst.ly/4qMWVDM
English
Andrew Chiles retweetledi

Just released a new @SpecterOps blog! I discovered that during client push in SCCM env's it's possible to remotely start WebClient and coerce HTTP from site servers for a relay to LDAP resulting in hierarchy takeover when WebClient is installed! 🫠
specterops.io/blog/2026/01/1…
English
Andrew Chiles retweetledi

My SCCM BloodHound OpenGraph collector, ConfigManBearPig, is finally ready to share! It can enumerate all of the relay TAKEOVERs and a few CRED and ELEVATE techniques from Misconfiguration Manager with just a domain account. Let me know what you find! specterops.io/blog/2026/01/1…
English
Andrew Chiles retweetledi
Andrew Chiles retweetledi

Generic AD labs don’t cut it.
Stop by @bagelByt3s' #BHEU Arsenal session and hear about LudusHound, a tool that rebuilds real-world AD environments using actual BloodHound data.
Learn more 👉 ghst.ly/48knutg

English
Andrew Chiles retweetledi

Beyviel David and BloodHound🤝 Ludus
If you're at BHEU, this will be a good one!
SpecterOps@SpecterOps
Generic AD labs don’t cut it. Stop by @bagelByt3s' #BHEU Arsenal session and hear about LudusHound, a tool that rebuilds real-world AD environments using actual BloodHound data. Learn more 👉 ghst.ly/48knutg
English
Andrew Chiles retweetledi

Just in time for the holidays, I wanted to share something that a lot of people have asked for: youtube.com/playlist?list=…
Short videos about Mythic development and customizations. This is just the start - I'll release a survey soon that'll get feedback for the next batch :)
GIF
English
Andrew Chiles retweetledi

Identity is the new battleground.
@jaredcatkinson talks with @thecyberwire about how attackers chain misconfigurations and identity relationships to reach critical assets, and how Attack Path Management stops them.
🎧: ghst.ly/4oXlfly

English
Andrew Chiles retweetledi

Released my first blog post today:
specterops.io/blog/2025/11/1…
And released SecretHound, a BloodHound OpenGraph extension for secrets:
github.com/C0KERNEL/Secre…
English
Andrew Chiles retweetledi

This is (probably) the last time I‘ll nag you with TaskHound. Since my org doesn’t allow me to use memes in our official blogs I finally took the hint and stopped procrastinating. My personal Blog is now live :).
r0bit.io/posts/taskhoun…
(Disclaimer: may contain sarcasm and memes)
English
Andrew Chiles retweetledi

That feeling when your PowerShell syntax error almost deletes Global Admin. 🫠
@FKasler shares a cautionary tale on why you should always read the docs when you are about to issue a “DELETE” operation on any resource in your client’s infrastructure. ghst.ly/3X2bTZ4
English
Andrew Chiles retweetledi

I have released an OpenGraph collector for network shares and my first blogpost at @SpecterOps on the subject!
You can now visualize attack paths to network shares in BloodHound 👀
specterops.io/blog/2025/10/3…
English
Andrew Chiles retweetledi

Just like chocolate and peanut butter, runZero and BloodHound are an amazing combination. Today we are introducing runZeroHound - an open source toolkit for bringing runZero Asset Inventory data into BloodHound attack graphs: runzero.com/blog/introduci…


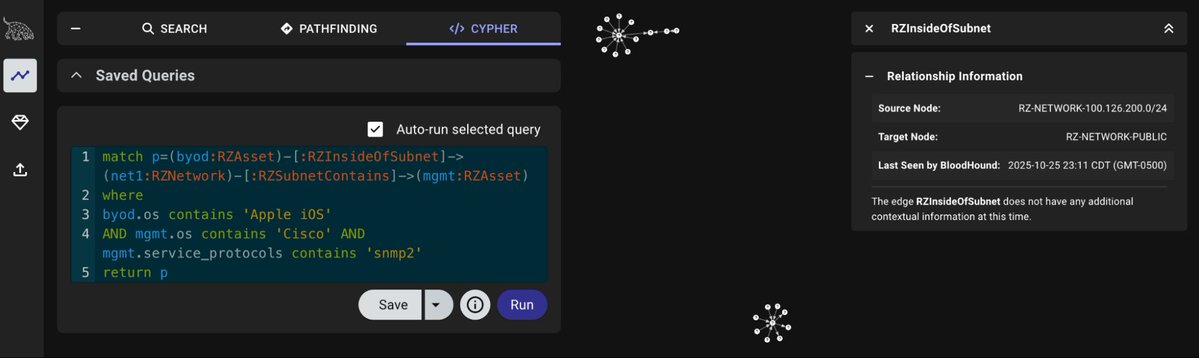
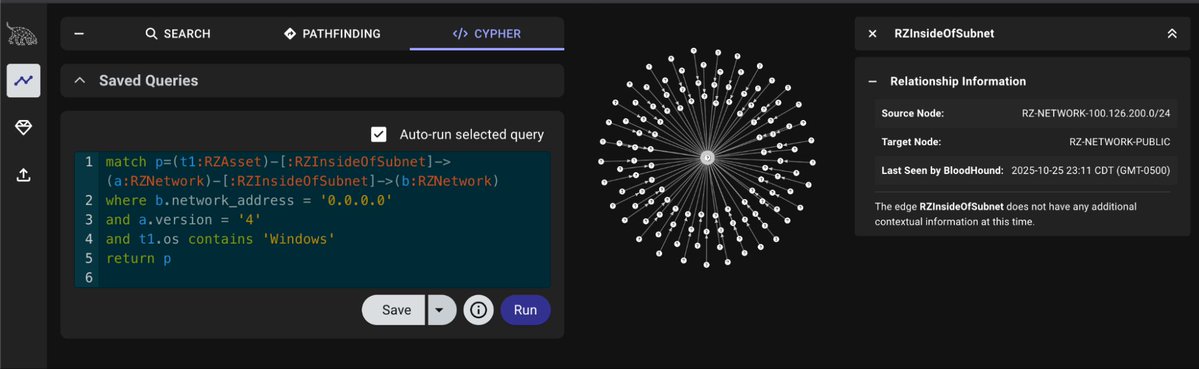
English




