Ariel Jungheit
304 posts

Ariel Jungheit
@ArielJT
Life under the sea was so much easier | Threat Research @harfanglab | Maker | Tweets are my own
G28 X0 Y0 Z0 Katılım Mart 2009
205 Takip Edilen1.4K Takipçiler
Heartbroken to hear about the passing of @Skvern0. He was one of the best threat hunters in the industry - even APTs were afraid of him. I’m grateful for the time we worked together and for everything I learned from him. Rest in peace.

English

Full report with IoCs and Yara:
harfanglab.io/insidethelab/r…
English

We promise, AI mentions kept to a minimum🤞🏻
Full report: harfanglab.io/insidethelab/2…
English
Ariel Jungheit retweetledi
Anyway, we wanted to tell a bit later, but we had to rush it now, as fellows did publish about the same toolset today (as "TOLLBOOTH"). We're fewer guys but we may still have found a bit more. IOCs & Yaras: harfanglab.io/insidethelab/r…
English
Ariel Jungheit retweetledi
Documents 📃 about alleged IRGC 🇮🇷cyber ops are being disclosed since last week (#KittenBusters). 2nd batch of data includes a reference to our work @HarfangLab: "see reports on publicly available tools (such as BellaCiao and CYCLOPS) – these are malware tools used"
English

New tunneling services timeline:
🗓️ 2025-04-24: lhr[.]life
🗓️ 2025-05-06: serveo[.]net, workers[.]dev
🗓️ 2025-06-11: euw.devtunnels[.]ms
Updated Yara rule alongside IoCs: github.com/HarfangLab/ioc…
For more information about PteroLNK, please refer to: harfanglab.io/insidethelab/g…
English

Following our recent #Gamaredon publication, the actor upgraded their PteroLNK malware and expanded infrastructure. Key changes:
- NTFS Alternative Data Streams (ADS) storage
- Randomized HTTP headers breaking network sigs
- Expanded tunneling services
- More robust DDR approach
English

@mgreen27 We did report the issue to Yara-X and they quickly fixed it, version >v1.2.1 should be good :)
English
This was an interesting read. I will need to update my parser it seems! 😳
I also guess fancy yarax rules targeting specific arguments will fail too :)
Ariel Jungheit@ArielJT
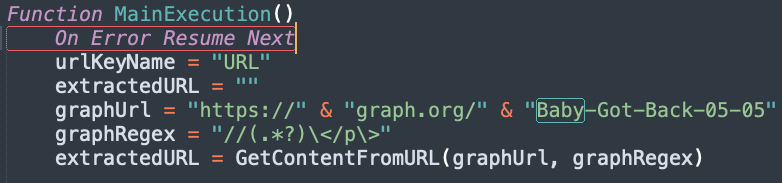
Dropping new research - this time on recent #XDSpy operations. Out of hundreds of LNK files leveraging ZDI-CAN-25373, we isolated a tiny cluster using an additional LNK parsing trick, leading us to uncover a multi-stage infection chain actively targeting government entities
English

Full technical report with IoCs and Yara rules below:
harfanglab.io/insidethelab/s…
English

Dropping new research - this time on recent #XDSpy operations. Out of hundreds of LNK files leveraging ZDI-CAN-25373, we isolated a tiny cluster using an additional LNK parsing trick, leading us to uncover a multi-stage infection chain actively targeting government entities

English