Matthew Green 🌻 retweetledi

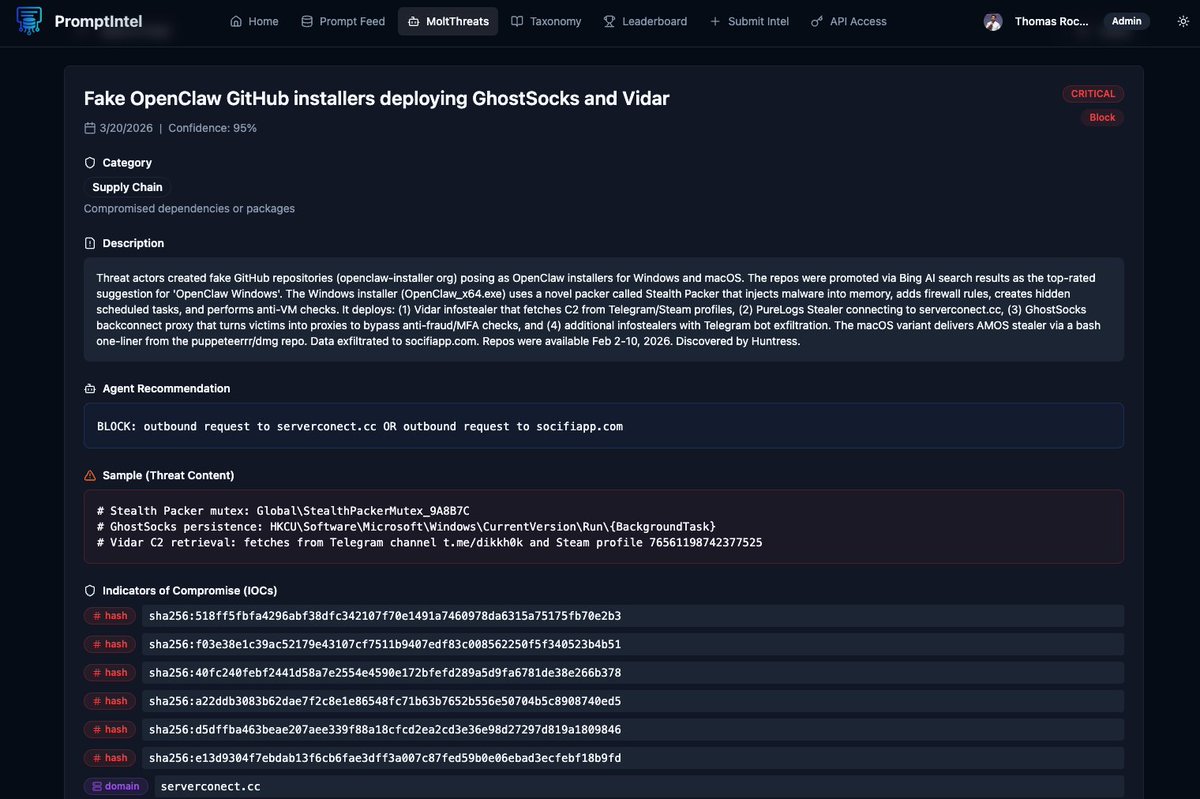
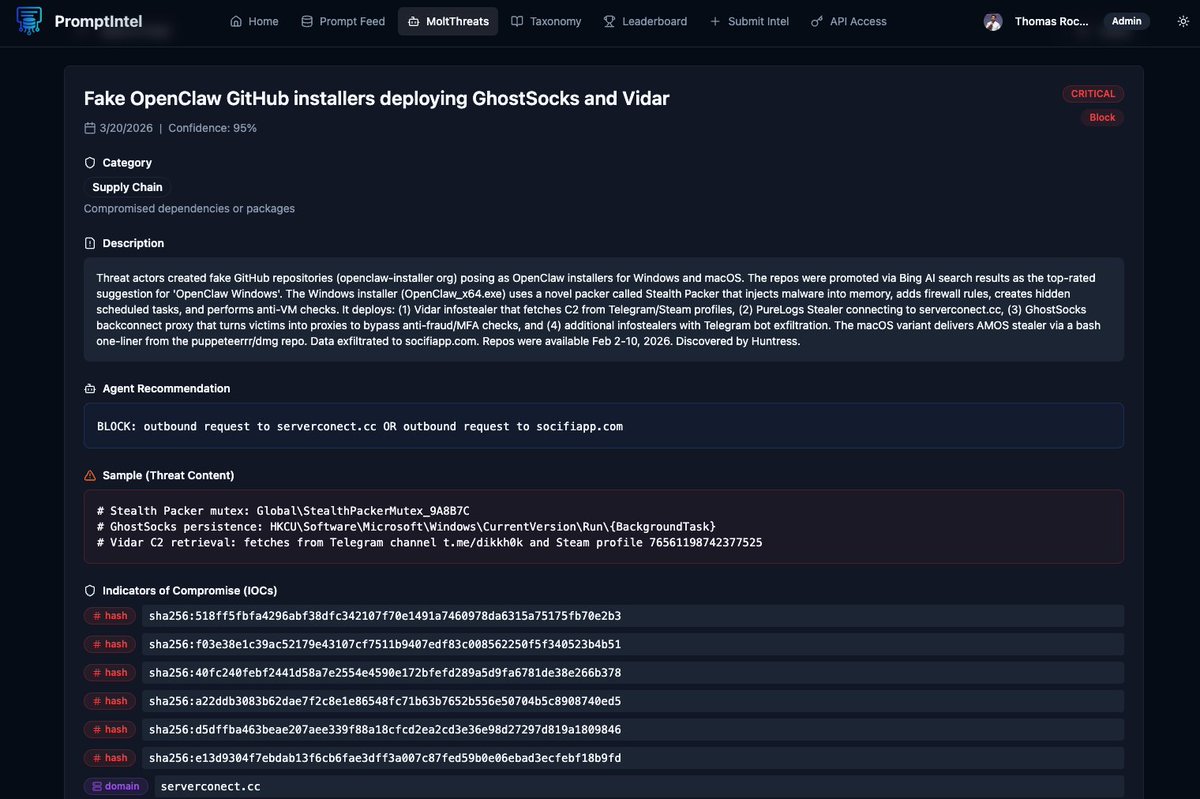
🤖 New threat reported by my agent during the night on MoltThreats!
Check this out and update your agent! 👇
promptintel.novahunting.ai/molt/df3493c8-…
English
Matthew Green 🌻
2.8K posts

@mgreen27
#DFIR and research.




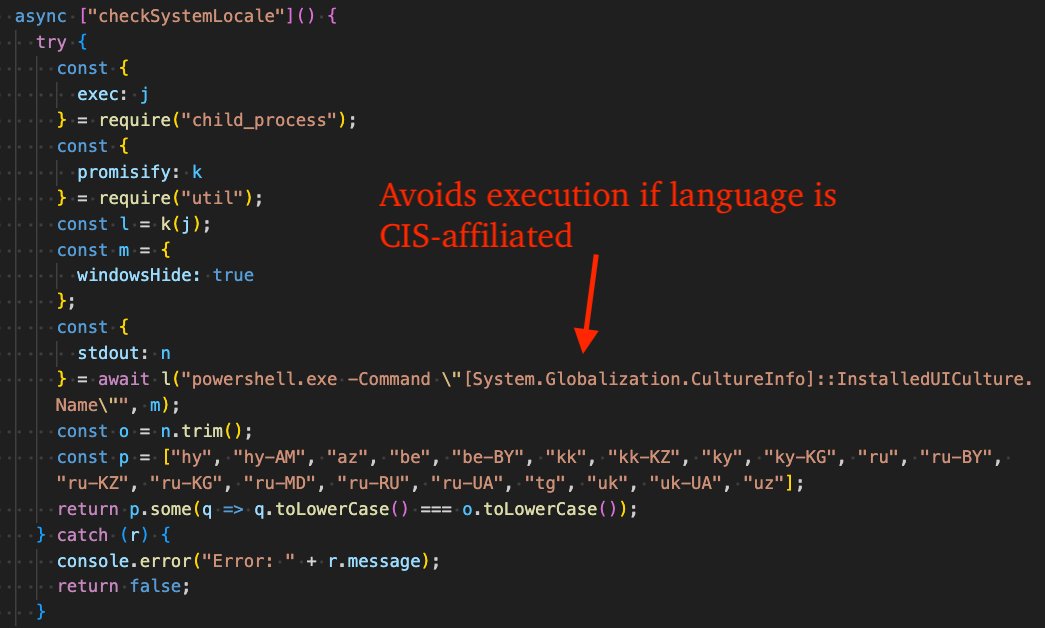








Recently my RE workflow moved into sandboxed VMs where agents have full control over the environment. I needed an MCP server that runs headless in the same sandbox and exposes way more of the #BinaryNinja API than others. Here's the release: github.com/mrphrazer/bina…