
AstraSec
142 posts


AstraSec
@AstraSecAI
Blockchain security auditing, trusted by Magpie, 1inch, Paraswap, Kodiak, ... (https://t.co/74XaWrdj3c)





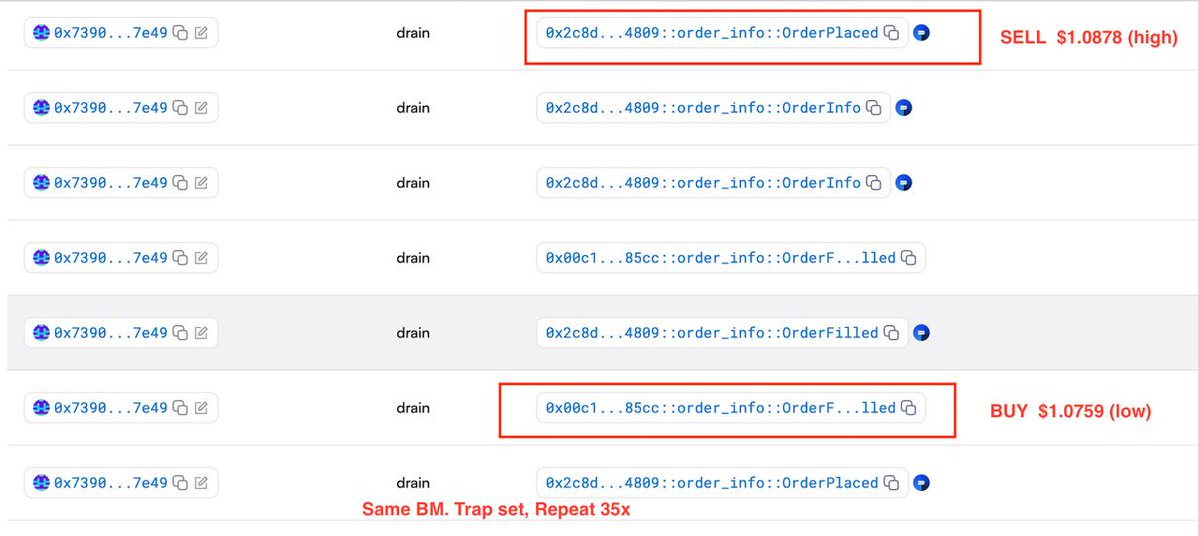
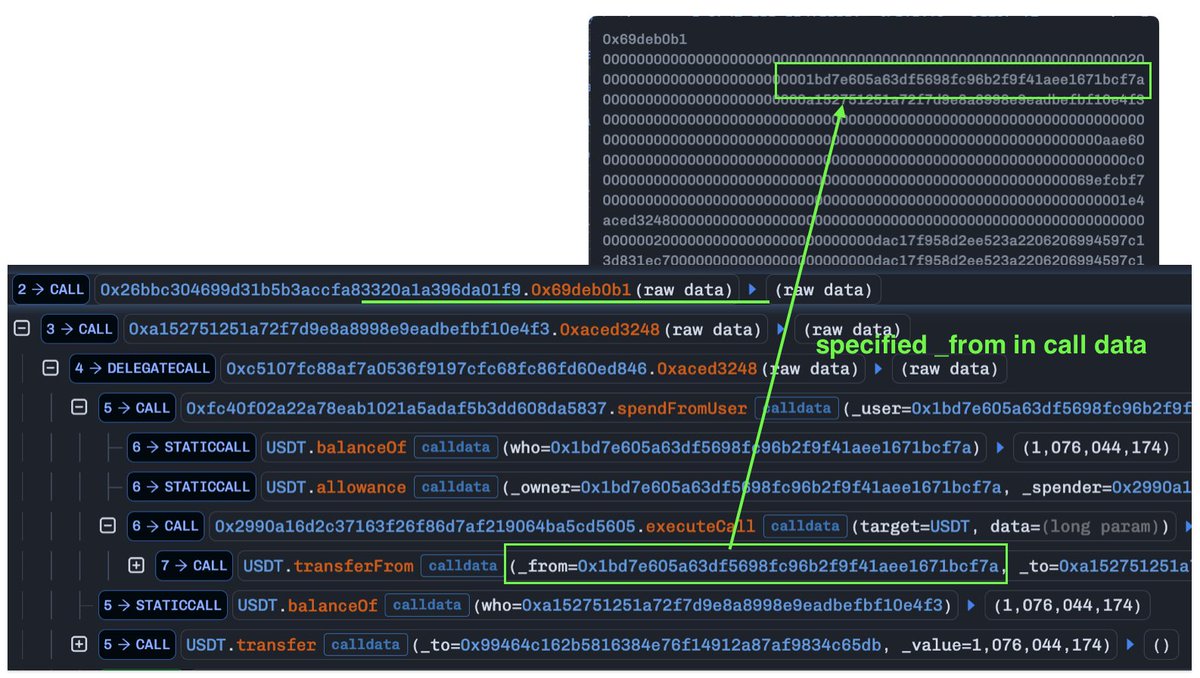
At ~3:18 AM UTC today, an undercollateralization vulnerability accrued $239,700 in bad debt in the USDC margin pool. Margin Trading has been temporarily paused. The Deepbook Insurance Fund has injected the amount of lost funds back into the affected pools. Deposits and withdrawals have now resumed.



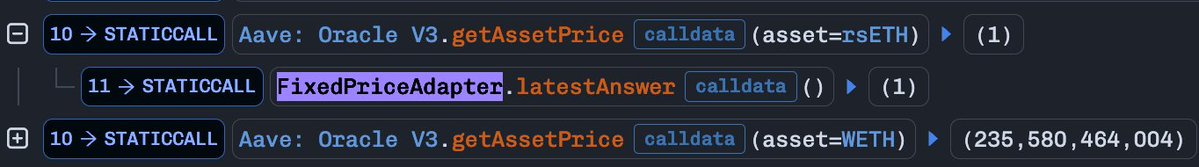






Earlier today we identified suspicious cross-chain activity involving rsETH. We have paused rsETH contracts across mainnet and several L2s while we investigate. We are working with @LayerZero_Core, @unichain, our auditors and top security experts on RCA. We will keep you posted as we learn more about this situation. Please follow only the official @KelpDAO handle for the updates.





