
0xBabsAudits
187 posts


@BABS96711
Smart Contract Auditor @sherlockdefi | I work on security reviews of DeFi protocols with focus on accounting risks, invariant breaks and trust assumptions.







There was an attack against the ZetaChain GatewayEVM contract today that impacted the internal ZetaChain team wallets only. We've already blocked the attack vector so no more funds can be compromised and will be releasing a detailed post mortem after we have completed our investigation. As a precaution cross-chain transactions are currently paused on ZetaChain. Investigation is still ongoing and at this time no user funds were impacted by this attack. The current status can be tracked at status.zetachain.com.


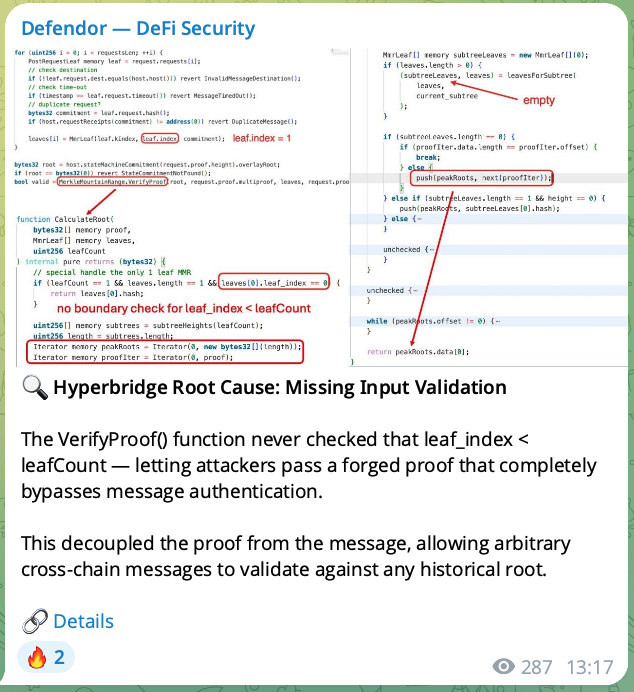




Web3 Security Contests 2024 vs 2026


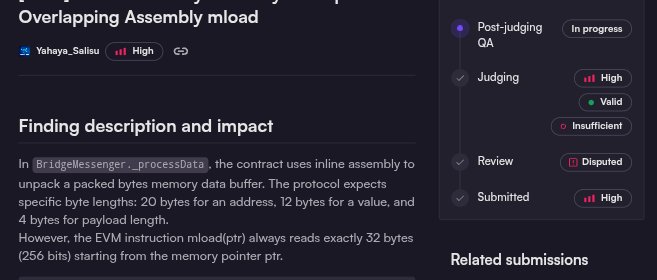
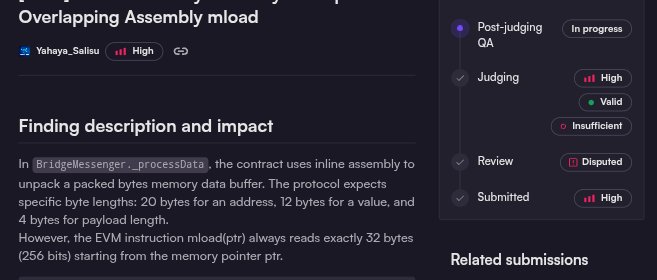
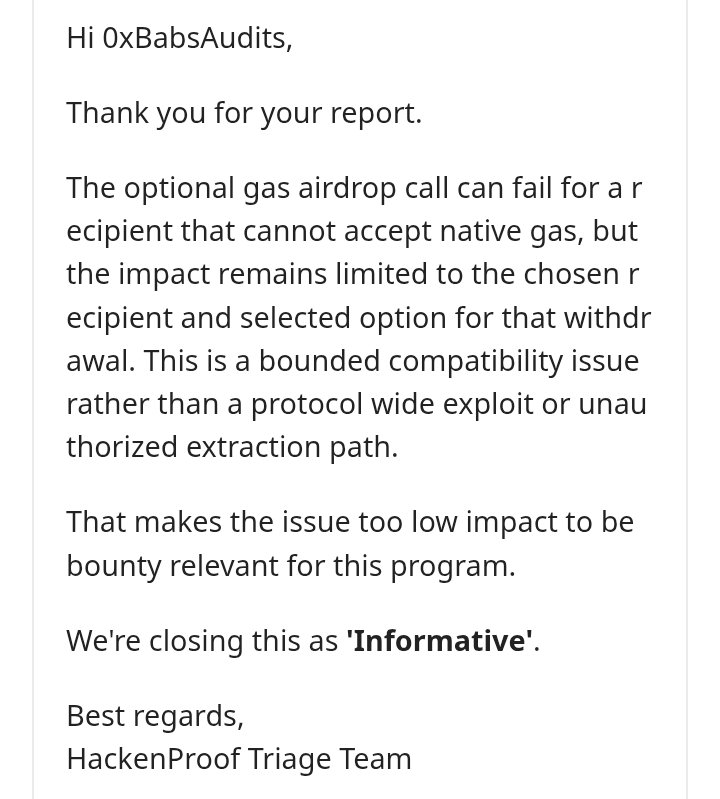
case in point

Due to the contest shortage, I'm considering starting bug bounty hunting again, for the second time since my journey began. I'll start by next week. What's your advice? #bugBounty #solidity #contest #smartcontracts #defi








What incentives do web3 researchers have to submit vulnerabilities ? @immunefi :KYC, banning, deposit to submit, ghosting @code4rena : KYC, submission limit Protocols: fix and lowball Protocols need researchers, real money is at stake, this industry is a joke. DeFi will die

I don't know what happened to @immunefi but they are partly responsible for the surge in hacks in 2026. People may want to submit a critical vulnerabilities and you are asking them to submit KYC information first ? to limit "spam". What happens if they don't want to ?