Balthasar
65 posts

Balthasar
@BalthasarMartin
Red team lead @ https://t.co/fkrENrHmF5 @[email protected] (he/him)

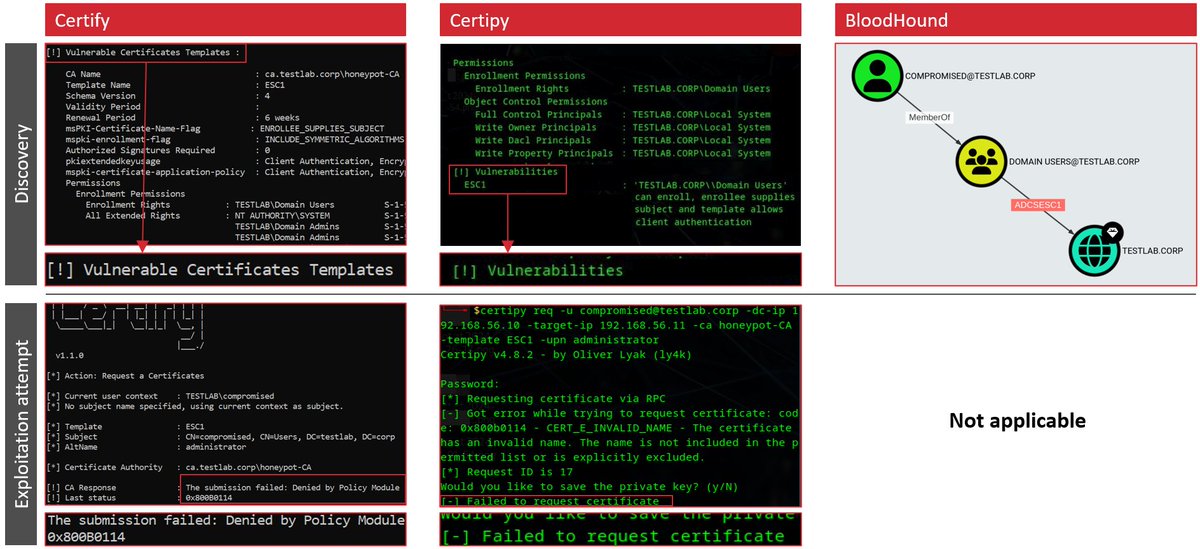
Today at #Troopers24 we released Certiception – the ADCS honeypot we always wanted to have. Blog: srlabs.de/blog-post/cert… Source code: github.com/srlabs/Certice… Slide deck, including our guide to deception strategy: github.com/srlabs/Certice…

Morning starts with LDAP guide by @sapirxfed at @WEareTROOPERS










Crypto-oh-my-god! @paulmmueller is at it again! What's old is new with Telerik exploits! A new tool release! Check out our write up on a new exploitation tool! blog.blacklanternsecurity.com/p/yet-another-…




The slides and video for our #HITB2022SIN talk where @jrrgimenez and Karsten explained and tested different EDR evasion techniques are now available. conference.hitb.org/files/hitbsecc… Here's a summary 🧵