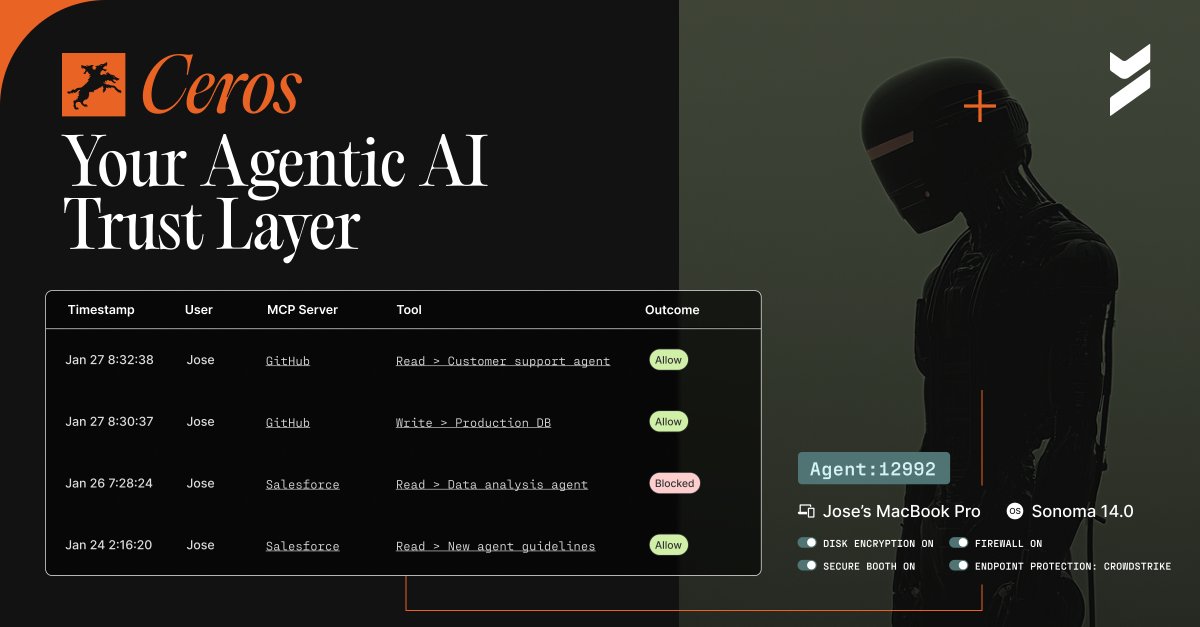
Every new AI agent your team ships = another API key living somewhere you don't fully control.
Nobody's doing anything wrong. That's just how credential checkout works at scale.
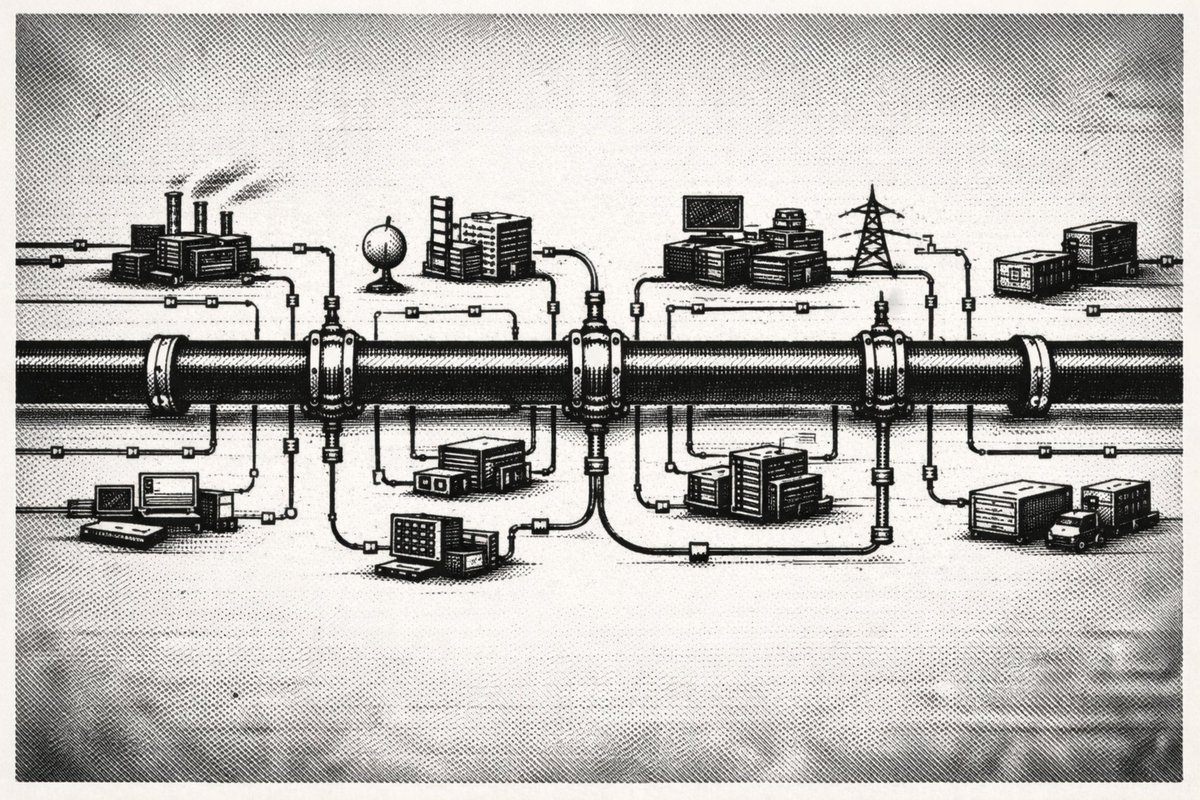
The problem compounds quietly until it doesn't. We wrote about what the architecture looks like when you stop distributing secrets to endpoints entirely, check it out:
beyondidentity.ai/blog/credentia…
English