Blockaid
1.5K posts


Blockaid
@blockaid_
Trusted by Coinbase, MetaMask, Stellar, and more to detect, understand, and protect against fraud, scams, and exploits in real time.
New York & Tel Aviv Katılım Şubat 2023
382 Takip Edilen21.6K Takipçiler

Join @blockaid_ for an exclusive VIP cocktail reception on Miami Beach, bringing together the builders and founders shaping the future of onchain security during @consensus2026.
📅 May 5, 2026
🕖 7:30 PM - 10:30 PM
⬇️ RSVP link below

English

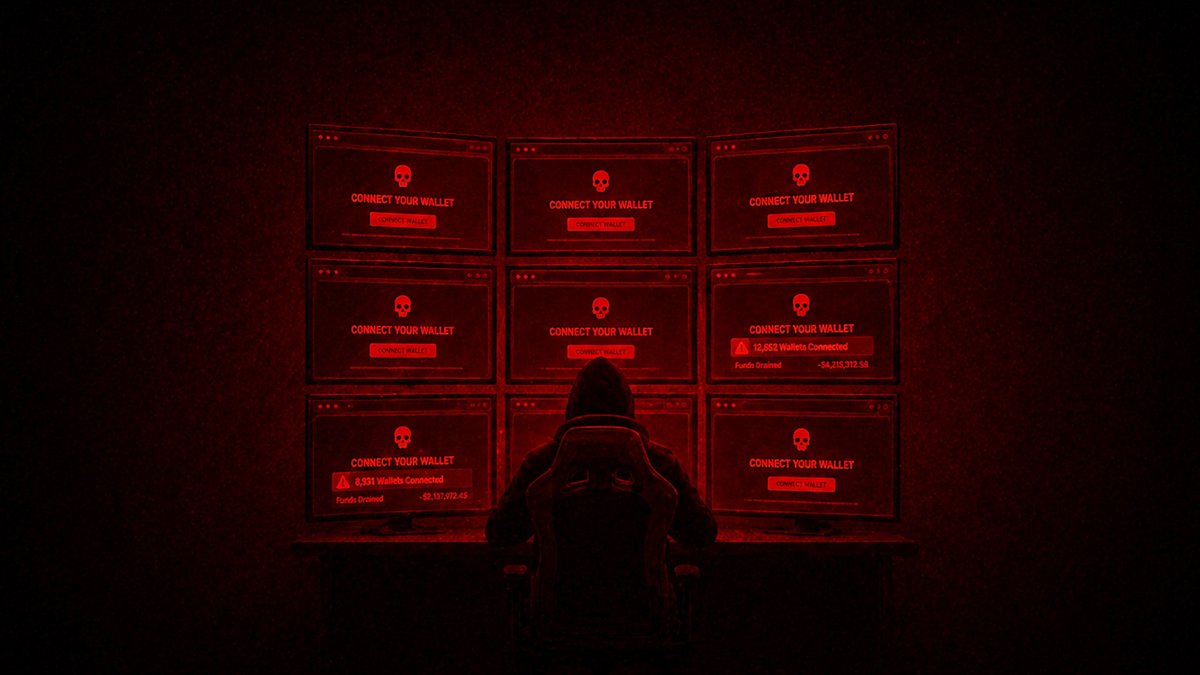
Crypto hacks have surged over the past month.
When a protocol gets hit, wallet drainers register fake 'revoke' and 'migrate' phishing sites within minutes and flood Twitter with posts targeting users who are trying to protect themselves.
Read more: blockaid.io/blog/how-walle…
English
Blockaid retweetledi

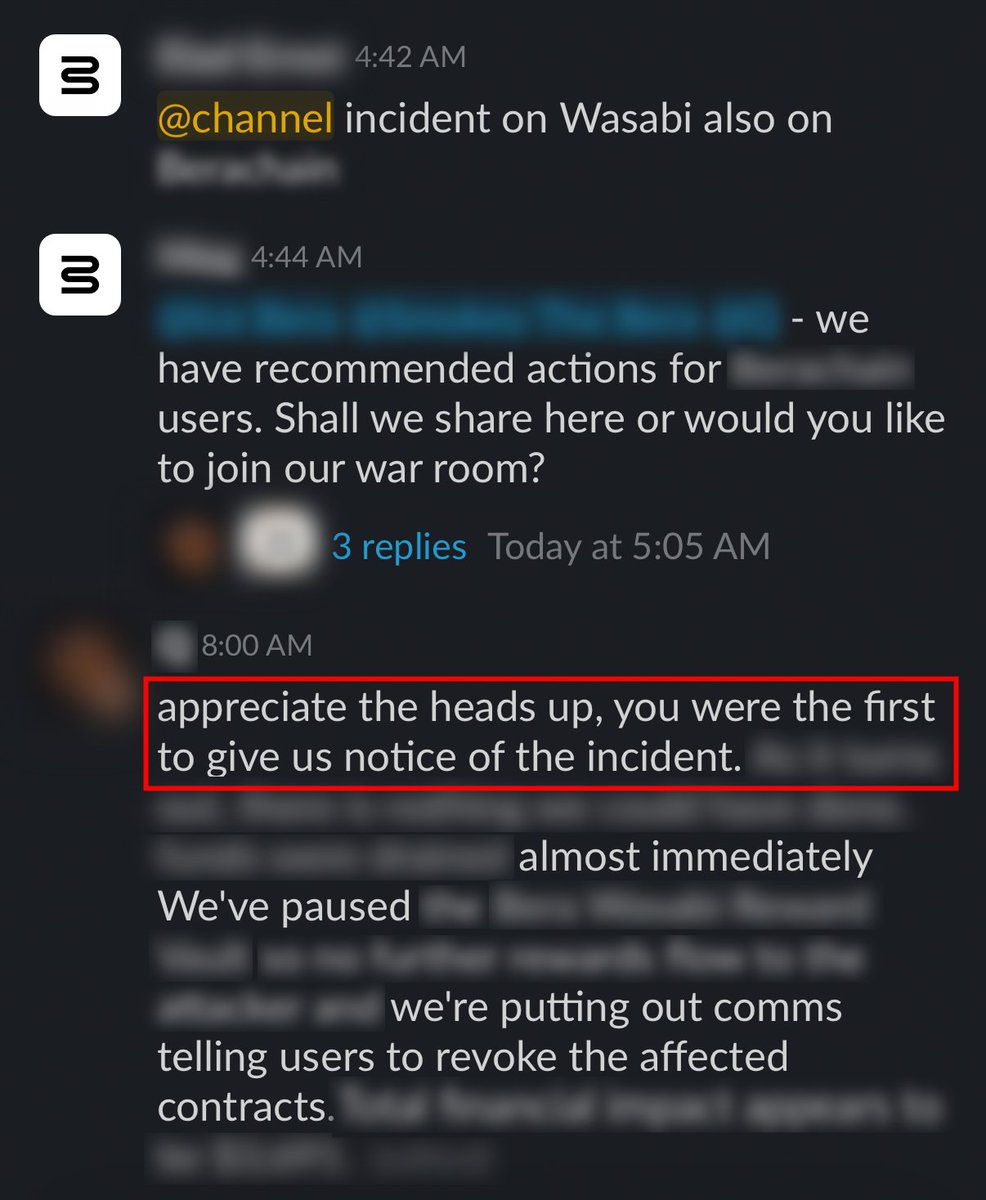
When working with onchain assets, you need to detect and respond to attacks in seconds and minutes, not hours.
The need for speed is real.
@Blockaid_ gives teams the speed and agility they need to act and contain the damage in real time.
Blockaid@blockaid_
🚨 Blockaid's exploit detection system identified an on-going admin-key compromise exploit on @wasabi_protocol across Ethereum and Base. The Wasabi: Deployer EOA was used to grant ADMIN_ROLE to an attacker helper contract, which then UUPS-upgraded the perp vaults and LongPool to a malicious implementation that drained balances.
English

Funds left my wallet to this address. Not sure what the vulnerability surface is. Others are getting zeroed out as well. Mainnet ETH only and strangely SAI:
etherscan.io/address/0xa707…
English

@wasabi_protocol @SEAL_911 @blockaid_ two of the best firms out there on this
didnt expect anything less
this is how you handle it properly
respect
English
Blockaid retweetledi

Update: We've been working with professional security teams including @SEAL_911 and @blockaid_.
Further updates will be shared as soon as they are available.
Do not interact with Wasabi contracts until further notice.
English

📷 COMPROMISED LP TOKENS 📷
All Wasabi/Spicy LP-share tokens minted by these vaults should be treated as COMPROMISED — the underlying assets backing them have been drained or are at risk while the Wasabi: Deployer key (0x5c629f8c…fb0c8) remains live. End-users holding these tokens are showing book-value, but the redemption value is 0 (or rapidly approaching 0). We strongly recommend customers (a) flag these tokens as compromised in their UIs, and (b) prompt users with active approvals to the Wasabi vault contracts to revoke immediately.
Ethereum Compromised Vault Contracts:
• 0x630ed8220f9cbc98358a2e2ecb0727d7b9d61397 (wWETH)
• 0x7d7bb40f523266b63319bc3e3f6f351b9e389e8f (sUSDC)
• 0xb533c682553f518a3961eeec2bfdc645c60289f0 (sREKT)
• 0xb86510bfdcd229a66f0617162ef1c45db1ceaba8 (wPEPE)
• 0x8d48b8d948726d4636aa15a9d6124422f461e153 (wMog)
• 0x127d3615a8865812f76ff8f214f9955c3a74820a (wBITCOIN)
• 0x10432bc30396e70f792b538d7e810c83dd7bfe71 (sZYN)
• 0xd2502e8e253a48d229df0e642a404c5bbff1c1b4
• 0x8e0edfd6d15f858adbb41677b82ab64797d5afc0 (Long Pool)
Base Compromised Vault Contracts:
• 0x1c4a802fd6b591bb71daa01d8335e43719048b24 (sUSDC)
• 0x197d5c29072c1444acb4f0935c219738a47e4a18 (wWETH)
• 0xb152e957ab1210153ba0ef07c52f5b559f1ad8c9 (sBTC/cbBTC)
• 0x833fd94958e35d55f2921f45bee4ae8ac82766b6 (sVIRTUAL)
• 0xb8da93ded809ac035c72b543ab728a55017239a0 (sAERO)
• 0x95c81f13d78449b3a02b39e41f26b18a5597fe95 (sBRETT)
• 0xe6c109b1f8052f1977c572a952f66677f49962a2 (sWELL)
• 0x078b931f7759ec09d74dd31316c610e09aac94fc (sSKI)
Root cause: Compromise of the Wasabi deployer key (wasabideployer.eth 0x5c629f8c0b5368f523c85bfe79d2a8efb64fb0c8, sole ADMIN_ROLE holder in the PerpManager OZ AccessManager).
The function called was grantRole(roleId=0 ADMIN, account=orchestrator, delay=0), which made the attacker's orchestrator an admin and bypassed WasabiVault.strategyDeposit's onlyAdmin modifier. Single-EOA admin, no timelock / multisig. Same attacker / same orchestrator + strategy bytecode that hit Wasabi.
Grant role transactions
Ethereum
etherscan.io/tx/0x985b4cde1…
etherscan.io/tx/0x11ff84ffb…
Base
basescan.org/tx/0x0b5dcdf99…
basescan.org/tx/0x185512ab1…
basescan.org/tx/0xa2ec466f2…
Bera
berascan.com/tx/0x23c5d8065…
Blast
blastscan.io/tx/0xbcb10b3d7…
English

Exploiter: 0x02228b0afcdbEdf8180D96Fc181Da3AF5DD1d1ab ETH drain tx (vaults): 0xcd77423f1bfa362c43f98356360c1f6c6e5fe989f18036e874884e9ad4a70116 Base drain tx (vaults): 0x10b371603d42a672b0bffda526af8400885c65fa7b541678f2bd8dad6fcb7e40 ETH drain tx (LongPool): 0xbabbfd5dc3a448244b1797928c69001726106c241f29e22b979a8bc01807c317 Extracted so far: ~$4.55M. Investigation is ongoing.
English

🚨 Blockaid's exploit detection system identified an on-going admin-key compromise exploit on @wasabi_protocol across Ethereum and Base. The Wasabi: Deployer EOA was used to grant ADMIN_ROLE to an attacker helper contract, which then UUPS-upgraded the perp vaults and LongPool to a malicious implementation that drained balances.
English

Multiple Sweat Foundation accounts were drained to zero in a single ~30-second window starting 2026-04-29 13:36 UTC.
Total extracted: ~13.71B SWEAT (~65% of supply).
Funds are being routed via Ref Finance and Wormhole/Portal Bridge.
The exploiter address is running a custom drainer contract (Rust crate name: exploit-resolve).
The attacker controls ~17.71 B SWEAT (≈ $3.46 M) - split between $2.68 M on the hub, $761 K on staging hop #2, and ~$20K already swapped to NEAR/USDC via Ref.
English

🚨Community Alert: Ongoing exploit on @SweatEconomy on @NEARProtocol.
Exploiter:
3be304b2151870b2be88b9de0b80acab921337ad152584138bd852fc6e9ae018
Largest exploit tx:
DvrSMfY85Anc6AuLUmoEDkDdab7qX5NUZLu76HN8NoPn
English
Update: Great news. Thanks to support from @Mysten_Labs and @SuiFoundation all users will be made whole
ZERO losses for anyone.
Aftermath will be up and running again soon. Thank you to both teams and to @blockaid_ for the rapid response.
For clarity: this was not a Move contract-language security issue.
English
Blockaid retweetledi

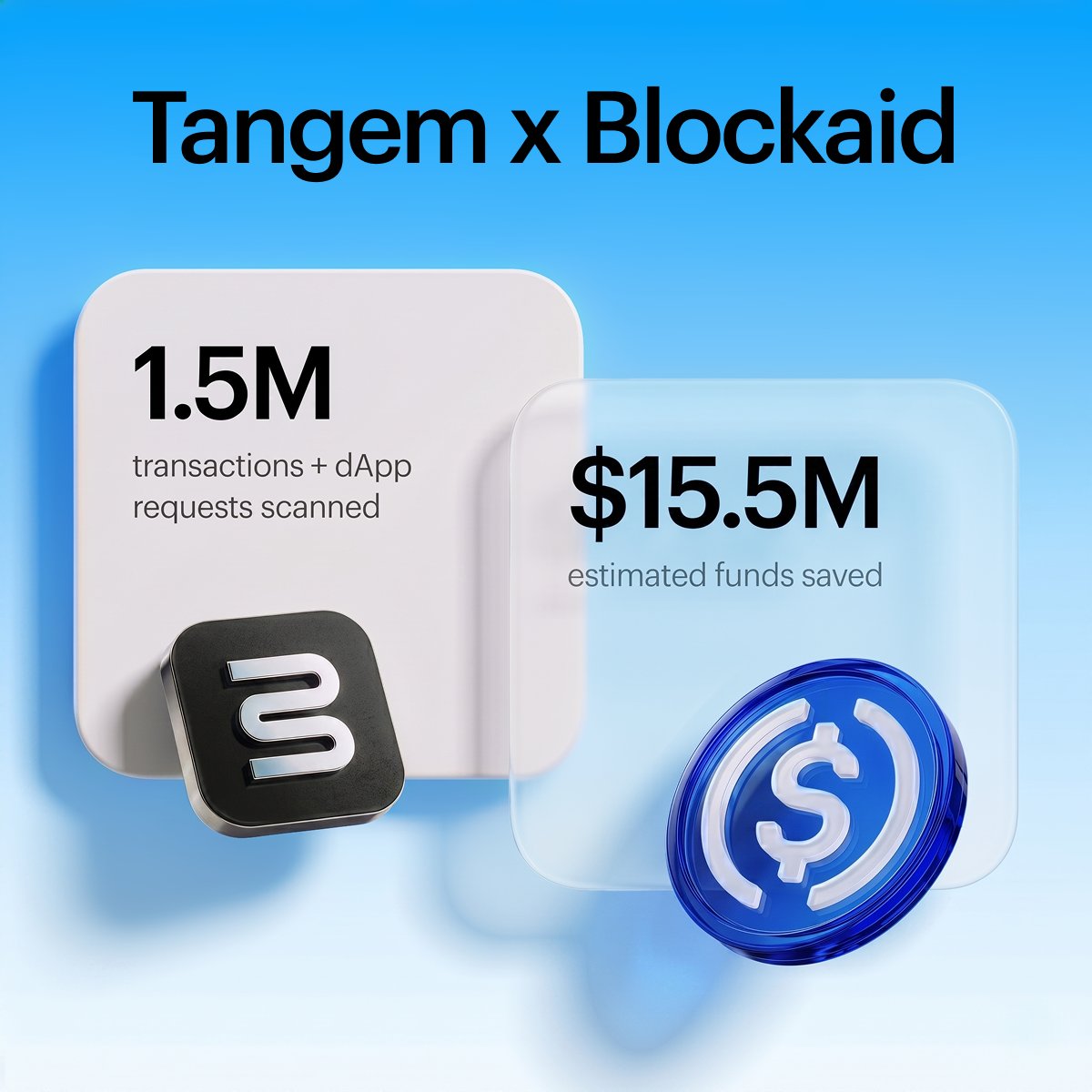
~$15.5M funds saved. 1.2K sketchy dApps blocked. 83K malicious txs caught.
One year ago, we integrated @blockaid_ into all @WalletConnect sessions on Tangem. Safer web3 isn’t the goal; it’s the baseline.
English

🚨 Blockaid detected and flagged an active exploit on @AftermathFi Perpetuals on @SuiNetwork.
~$1.1M USDC was drained across 11 transactions in ~36 minutes by attacker 0x1a65086c85114c1a3f8dc74140115c6e18438d48d33a21fd112311561112d41e. The exploit targeted a bug in the perp clearing house fee accounting, allowing synthetic collateral inflation and withdrawals from protocol vaults.
We are supporting the @AftermathFi and @Mysten_Labs teams and will share more findings shortly
English

🚨 Community Alert: Ongoing exploit on @ZetaChain cross-chain contracts!
Please revoke any approval for any ZetaChain GatewayEVM contract on all EVM chains.
English