Blockscope retweetledi

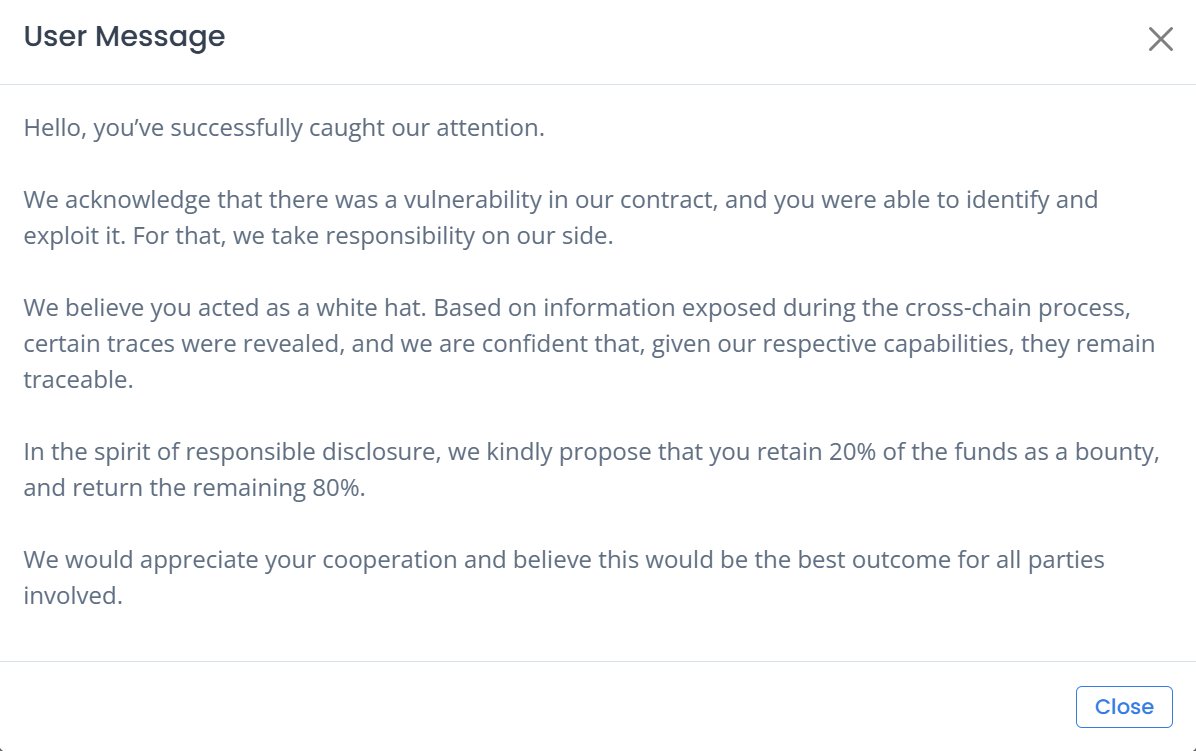
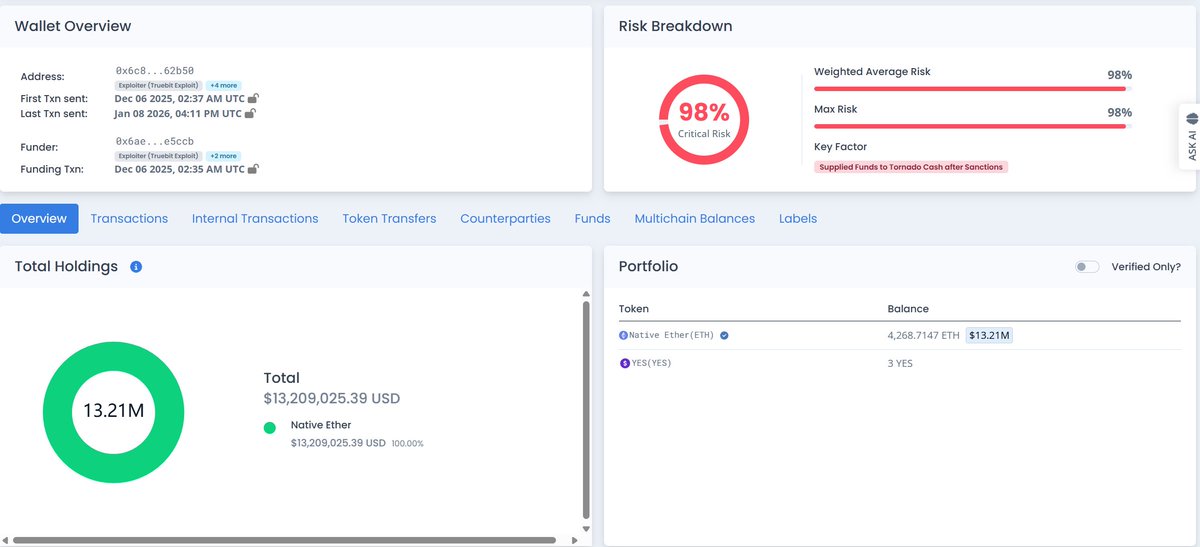
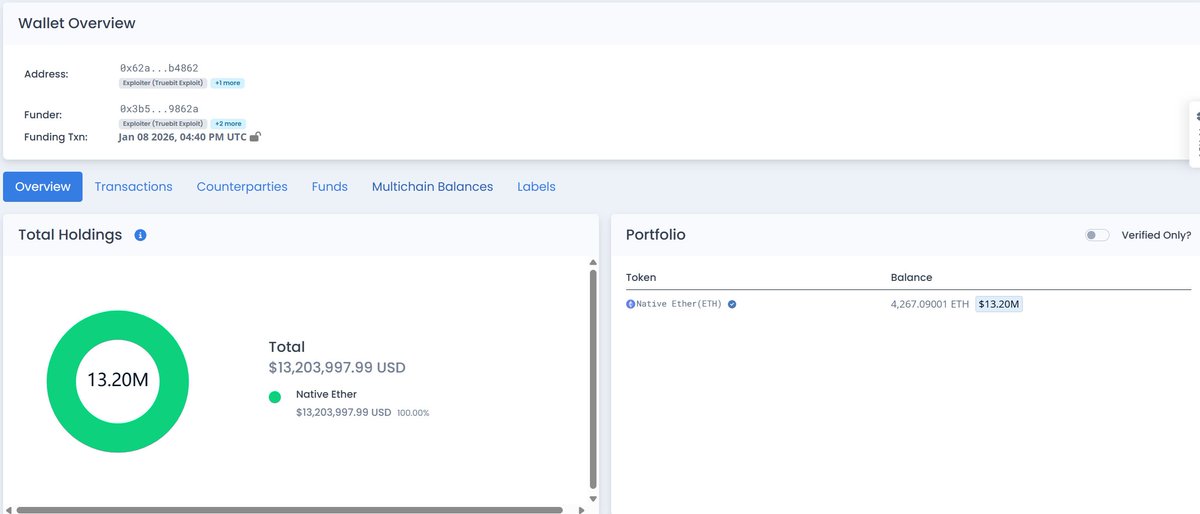
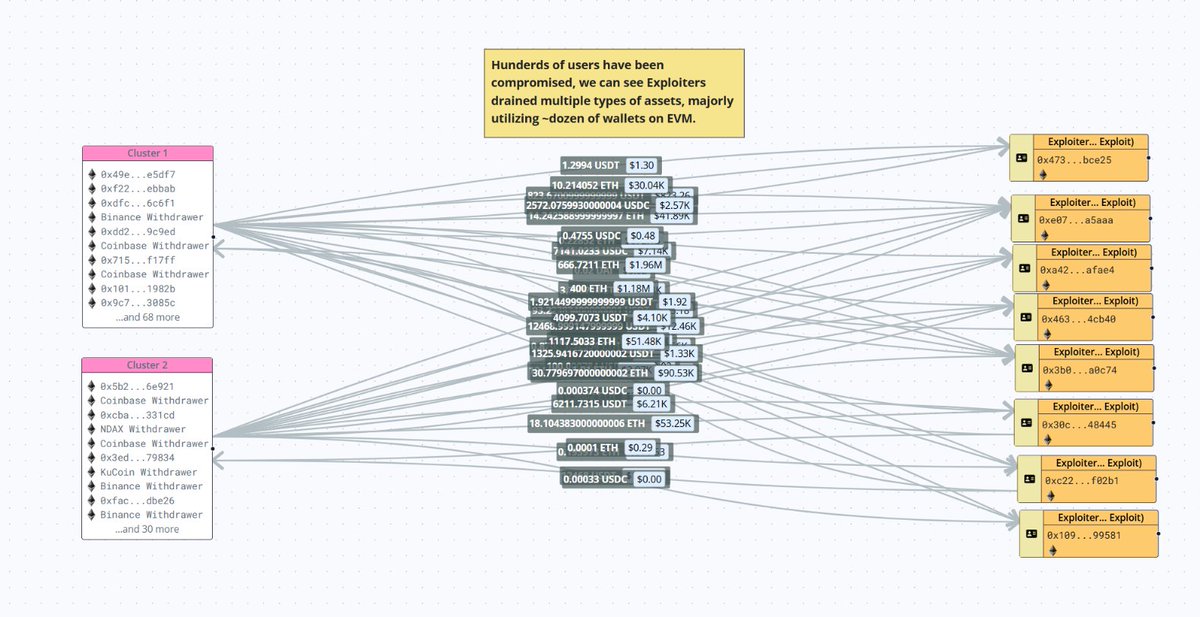
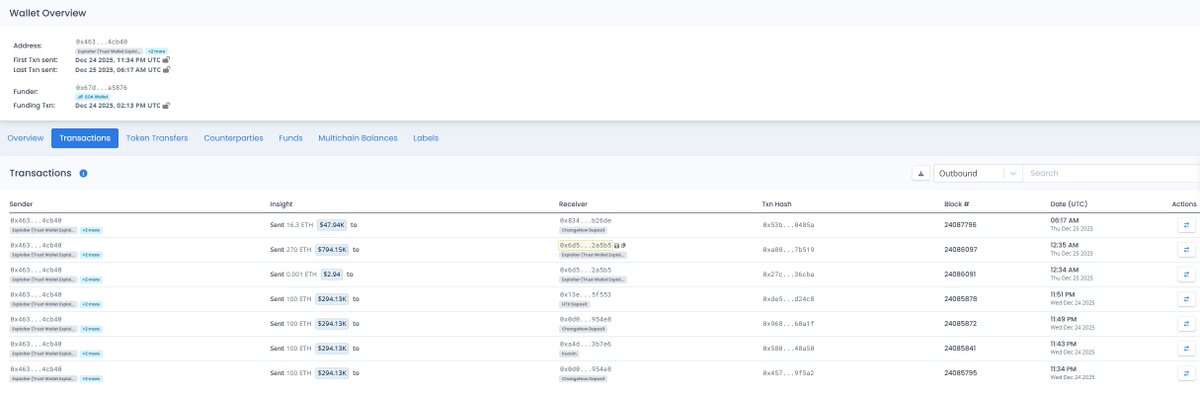
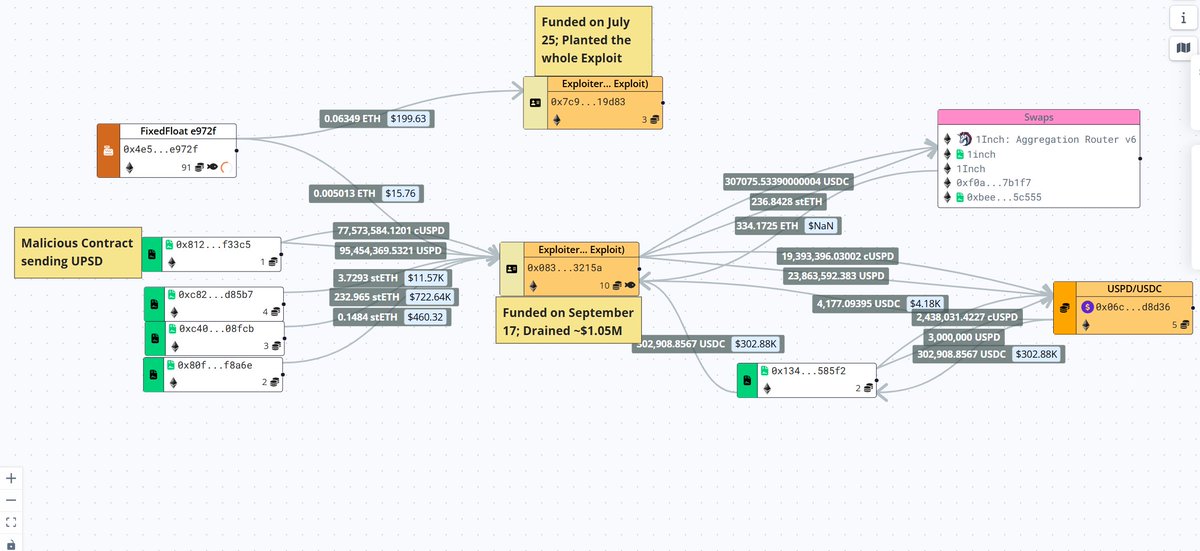
First major hack of 2026, as @Truebitprotocol was drained for $26.2 million through an overflow in unverified bytecode.
The same attacker hit Sparkle weeks prior. Old code keeps bleeding - the archives have clearly become a shopping list.
rekt.news/truebit-rekt
English