Brian Vermeer retweetledi

Most developers install skills without reading what's inside them. But that's exactly what attackers are counting on.
@sjmaple sits down with Brian Vermeer (@BrianVerm) from Snyk (@snyksec) at DevNexus to get into the security risk hiding inside the skills and MCPs running on your local machine. They scanned over 4,000 skills and found that 1 in 7 had at least one critical security vulnerability.
Here’s what you need to know:
• Why prompting your agent to write secure code doesn't make it secure
• How a trusted skill can update silently and start offloading your credentials
• What prompt injection actually looks like inside a skill file
• Why vibe coding makes the attack surface bigger, not smaller
• How the Snyk agent scan catches what you'd never spot manually
Every skill on the Tessl registry now has a Snyk security scan attached. Check before you install.
(0:00) Trailer
(1:17) AI DevCon
(2:11) Introduction
(3:32) Snyk's evolution from SCA to AI security
(5:06) Can agents generate secure code?
(6:01) Skills and secure coding guidance
(7:24) Snyk agent scan and Tessl integration
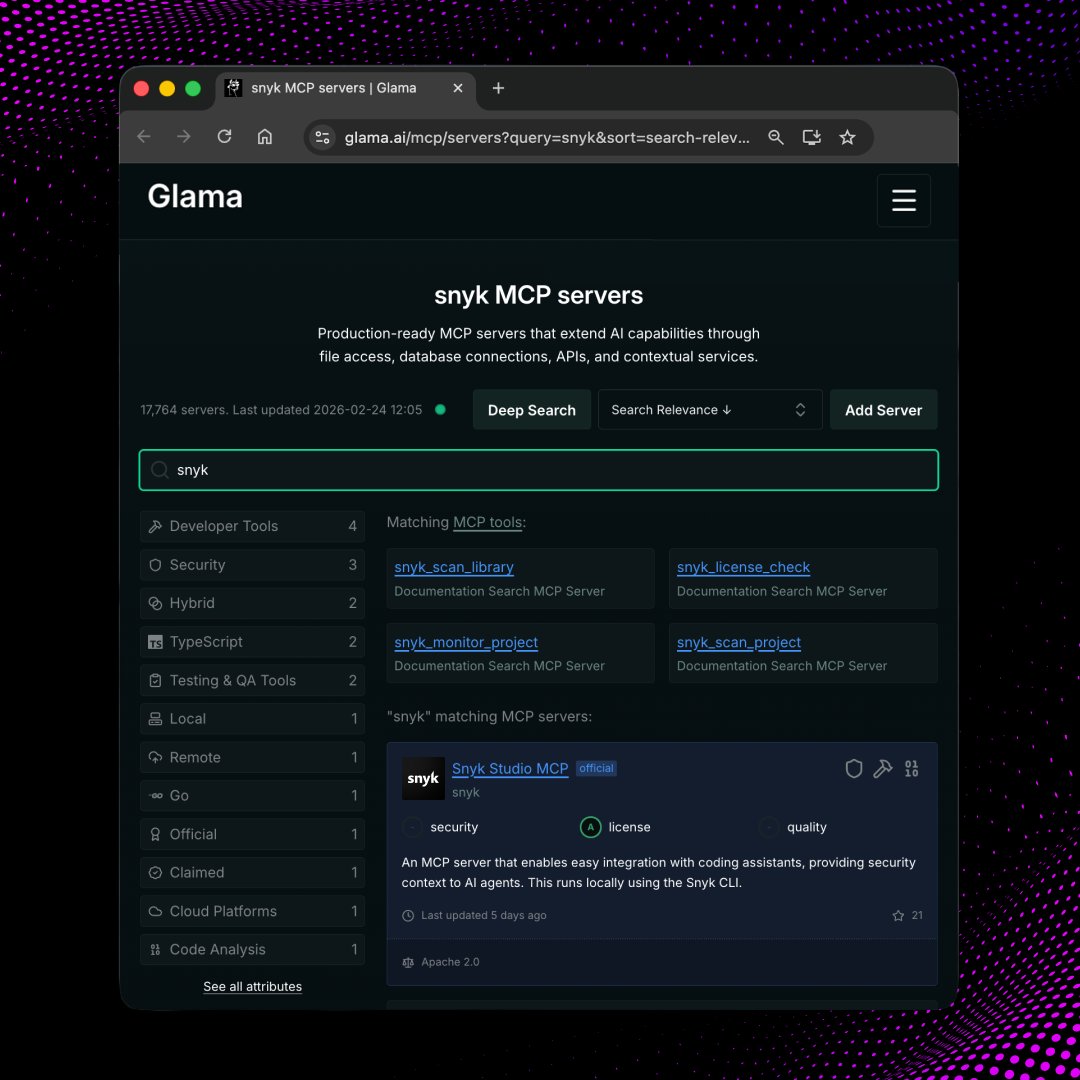
(7:56) MCP as the next supply chain problem
(9:04) ToxicSkills threat taxonomy
(10:27) How malicious skills exploit privileges
(12:39) MCP server attack surface
(13:51) The speed of AI adoption vs security
(15:51) Scan results and critical vulnerabilities
(17:06) False positives in natural language
(18:26) How attackers create malicious skills
(20:41) Trust and open source skill risks
(21:29) Using Snyk agent scan directly
(24:58) Snyk scans in the Tessl registry
(26:41) Advice for skill creators
(28:16) Protecting yourself as a skill user
(29:44) Snyk Evo Agent Guard for Cursor
(33:21) Runtime guardrails and policies
(34:10) Wrap-up and where to learn more
English