Brokenarrow
1.6K posts

Brokenarrow
@Brokenarrow42
Private Investigator - OSINT practitioner and student

just found out iLovePDF is a million-dollar company. How is it even making money? 😭

top 10 movies 1. Gladiator 2. Braveheart 3. Lord of the Rings 4. Captain Fantastic 5. Legends of the Fall 6. Last Samurai 7. The Matrix 8. Batman Begins 9. Rocky 10. Borat you?



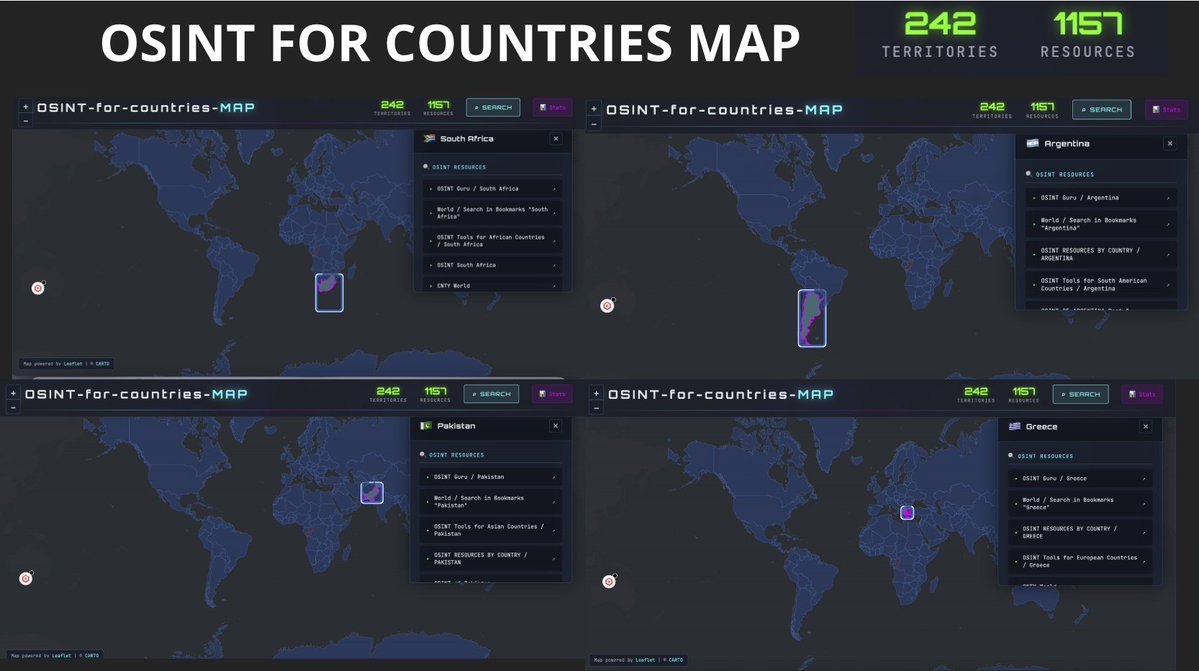




TGSpyder: Your Telegram OSINT Assistant 📲🔍 Telegram hides a lot of data behind groups and channels, but OSINT doesn’t have to wait. TGSpyder is a command-line tool built for investigators, analysts, journalists, and researchers. It helps you: ✅ Scrape member lists from public & private groups ✅ Collect chat messages ✅ Extract invite links ✅ Lookup users by username or ID ✅ Identify sticker pack creators 🧩 All outputs are exported to clean CSVs, ready for analysis and reporting. It even supports proxies (Tor/VPN) for secure and private operations ⚡ Website link: github.com/Darksight-Anal… --------- If you want to learn more about email OSINT and more, check out the OSINT Mastery course at cybersudo.org/osint-mastery you’ll learn OSINT from scratch with a real-life investigation. P.S. ♻️ Repost if you found this helpful.



OSINT Tip : Stop Installing Extensions Blindly If you’re doing #OSINT and you’re installing browser extensions without checking what’s inside them, you’re basically handing your investigation over to strangers. This week’s GhostPoster incident is a perfect reminder: even “trustworthy” extensions like Adblock clones, YouTube enhancers, Instagram viewers, and RSS readers were quietly hijacking user traffic, injecting code, opening backdoors, and tracking everything you clicked. bleepingcomputer.com/news/security/… For an OSINT investigator, that isn’t just annoying, it’s an OPSEC failure. Extensions see: •The sites you visit •The queries you run •The platforms you log into •The targets you research •The timelines of your investigations If an extension turns malicious (or gets sold to someone who is), your entire workflow becomes telemetry for an unknown third party. Due diligence isn’t optional. Check every extension, verify the developer, audit permissions, and assume that anything touching your browser can compromise your case work. Because in OSINT, it’s not the exploit you didn’t notice that ruins your investigation. It’s the extension you assumed was harmless.