IRIS C2
1.2K posts


IRIS C2
@C2IRIS
The world's most advanced offensive cyber platform

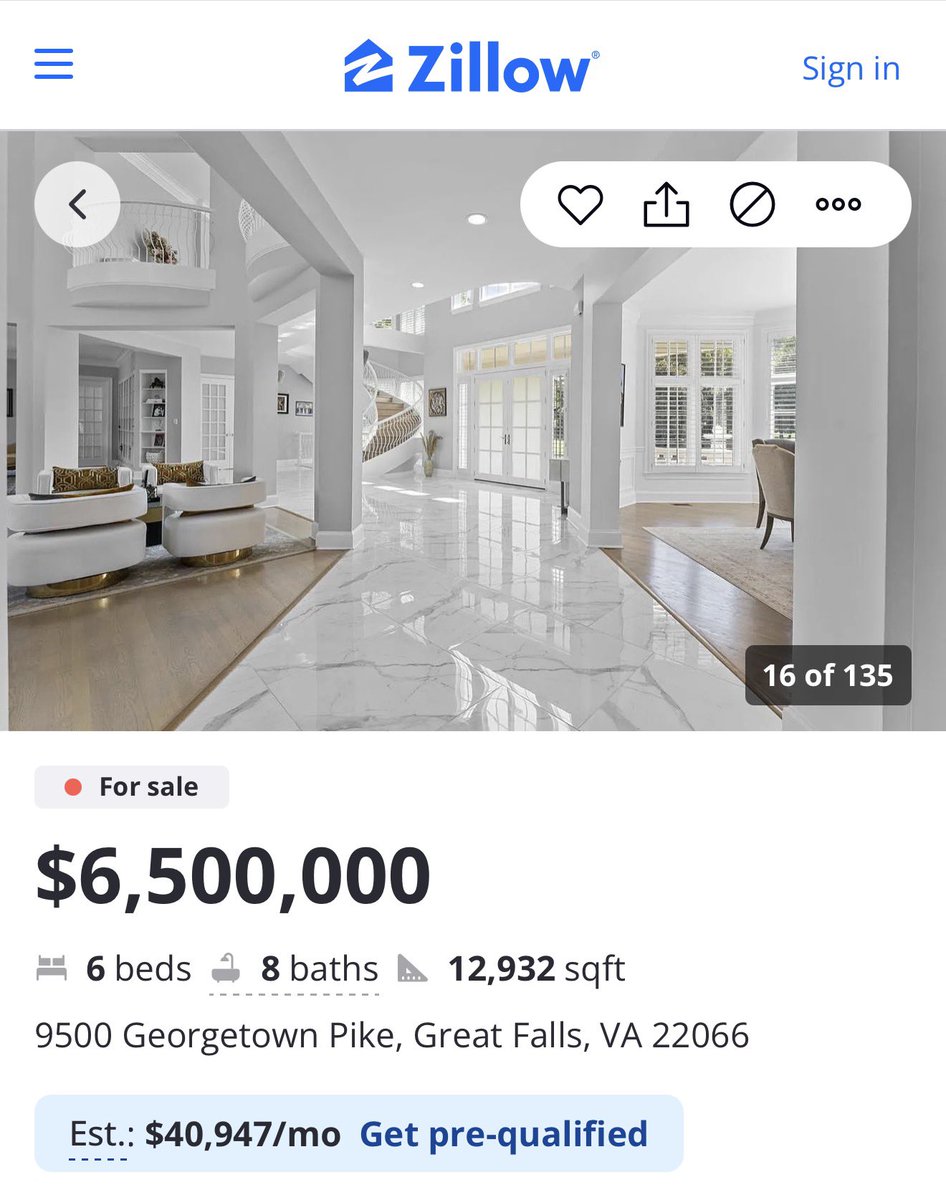
You could start with an undergraduate degree at an Ivy League school, ideally Yale or Princeton. Spend two formative years at Goldman Sachs in IB or ECM, learning the rhythms of the Street. Then earn your MBA at Harvard Business School or Stanford GSB, where the real networks solidify. From there, make the calculated jump to a respected boutique bank with a sharp niche offering — whether it’s distressed credit, SPACs, tech M&A, or complex structured products. Execute flawlessly, close the right deals, and secure a $25M+ penthouse with sweeping Central Park and Manhattan skyline views that most people only see in magazines. Become a member of both the Yale Club and the Metropolitan Club, where old-world discretion still matters. Cultivate taste that is quietly superior to anything you’ll find at a Soho House rooftop. But you will not.









met a guy who codes in assembly today

most delightful software ive used was entirely c++









