Sabitlenmiş Tweet
cyint_dude @[email protected]
3.8K posts

cyint_dude @[email protected]
@CYINT_dude
Technical Director of #threatintel @thomsonreuters | rock climber & boulderer | tweets and views are my own | Mastodon:@[email protected]
Katılım Mayıs 2014
2.4K Takip Edilen5.3K Takipçiler

@_John_Doyle You have a bouldering area in your office?!?! Who sets the problems? My climbing gym is very close but an office gym is another level!
English

Getting a few sends in before work at our office climbing gym. #WorkforGoogle #BoulderingInBoulder

English

Woo hoo! Ticket for #cyberwarcon purchased! Looking forward to seeing folks there! #threatintel
CYBERWARCON@CYBERWARCON
CYBERWARCON is coming!!! Registration and CFP are now open for this year’s #CYBERWARCON! This year’s keynote will be given by the NSA’s @adamski_morgan. The in-person event is in Arlington, VA on Nov. 22nd and virtual tickets are available. 1/x cyberwarcon.com
English

@T1l2L3n Sadly, we are not able to offer FT remote for this role.
English

@CYINT_dude Just curious, i noticed it is marked as hybrid. Is there an FT remote potential with this one or does it require the hybrid part?
English

Hello! We are looking for a new cyber #threatintel analyst to join our team! Don't have any experience in the intel space? That's OKAY! We are looking for folks eager to learn and grow! thomsonreuters.wd5.myworkdayjobs.com/External_Caree…
English

@4n6ir Or maybe even more simply: how have you (#threatintel) made security better at the organization (and/or what else could be done assuming right resources)?
English

@KyleTDavis1 Keep a list of topics/issues customers care about and review if/how your team can address them. Collect sources and change processes where needed to fulfill requirements. And don't mention "PIRs" to stakeholders (because they don't care and that's okay). #threatintel
English

@KyleTDavis1 PIR's in the #threatintel space IMO have been mostly over-engineering and intellectualized, drawing too much from .mil in the overly prescriptive development and management, leading to overhead that most teams can't handle...
English

Microsoft's direct observations of AI abuse are consistent with NCSC's report from earlier this year in which they forecasted the ways in which AI would boost different stages of cyber operations #threatintel
microsoft.com/en-us/security…
ncsc.gov.uk/report/impact-…

English

I coin the collection and analysis of internal data and incidents: INTINT #threatintel
English

@HostileSpectrum Are you telling me that I can no long rely on TWITINT exclusively for my intel that I copy/paste directly to my most senior leadership?
English
For anyone still unclear on the point, X Twitter is not a medium for delivery of finished intelligence. It may be useful in exhortations for attention to tradecraft, or to highlight lines of analysis that may be further developed in product. A shop may also use it to highlight contract / case BLUF or specific KJ, this is however dependent on underlying analysis & production outside of this platform. Do not confuse the two
English

If your company is using AI internally, or developing customer-facing AI products, then #threatintel teams will be expected to start answering questions about the related risks (like, right now). This is going to be a very challenging requirement IMO.
English

NIST Taxonomy of Attacks > csrc.nist.gov/pubs/ai/100/2/…
MITRE ATLAS > atlas.mitre.org
English

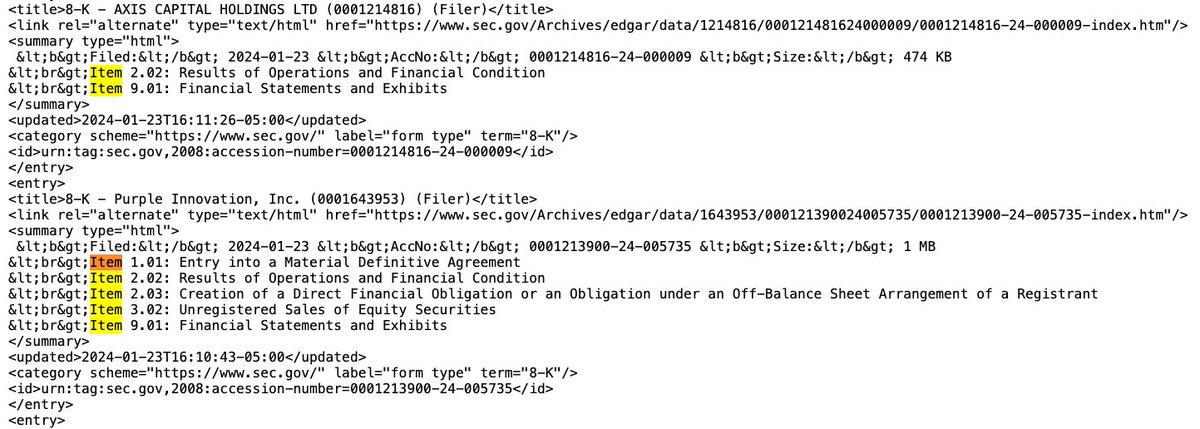
Microsoft and VF Corporation are the first two companies I'm aware of that have made Item 1.05 filings. sec.gov/ix?doc=/Archiv…, sec.gov/ix?doc=/Archiv…
English

Re: #1 - Executives will be closely watching how other companies are responding to the SEC's new "4 day disclosure" rule. The SEC Edgar search allows you to create an RSS feed of 8-K filings and it includes the "Items" filed. Pay attention to the "Item 1.05" filings.
English

Two collection requirements I anticipate #threatintel teams needing to prioritize this year: 1) SEC 8-K filings with the new "Item 1.05" for disclosures of possible material breaches and 2) adversarial machine learning TTP
English