ChainBounty
697 posts

ChainBounty
@ChainBountyX
ChainBounty is a decentralized platform that helps solve security challenges in the crypto space.



Most crypto hacks don't start with a cracked wallet.🤔 They start with trust — in a UI that looks exactly right, but isn't. Bybit lost $1.5B this way. Signers approved what they saw. What they saw had been replaced. The fix isn't more complicated software. It's moving verification off the screen that can be tampered with.




LATEST: 🚨 Hacked crypto token prices drop a median 61% within six months of a breach, with 84% ultimately failing to recover, according to Immunefi.





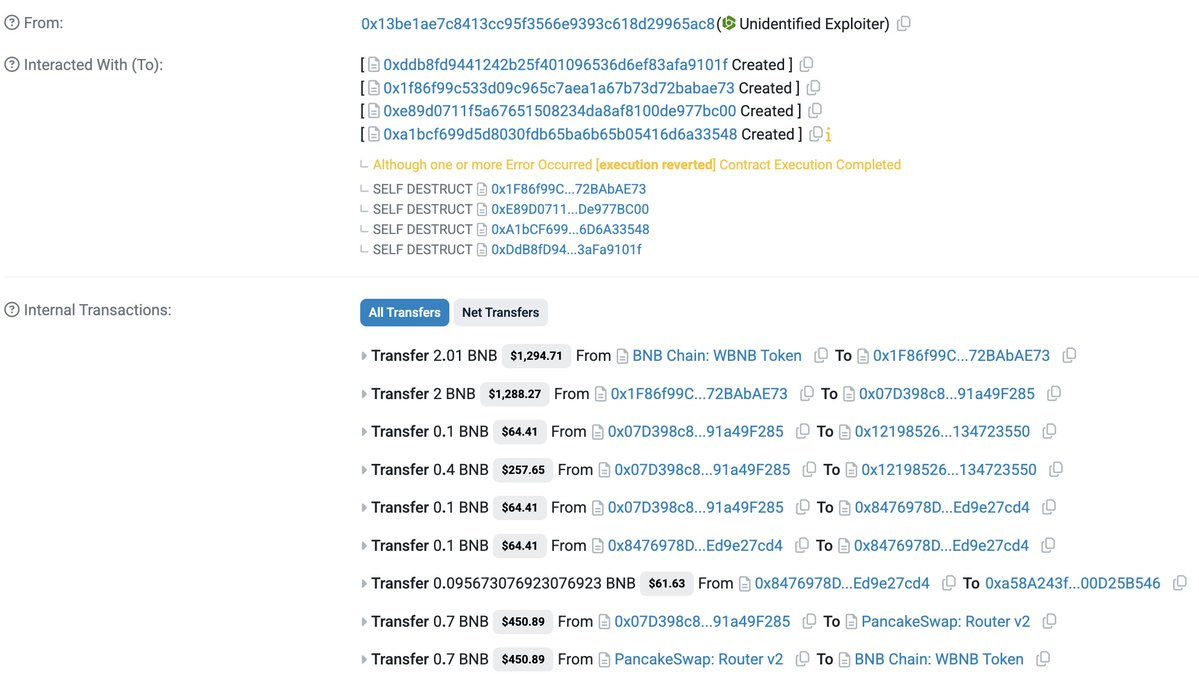
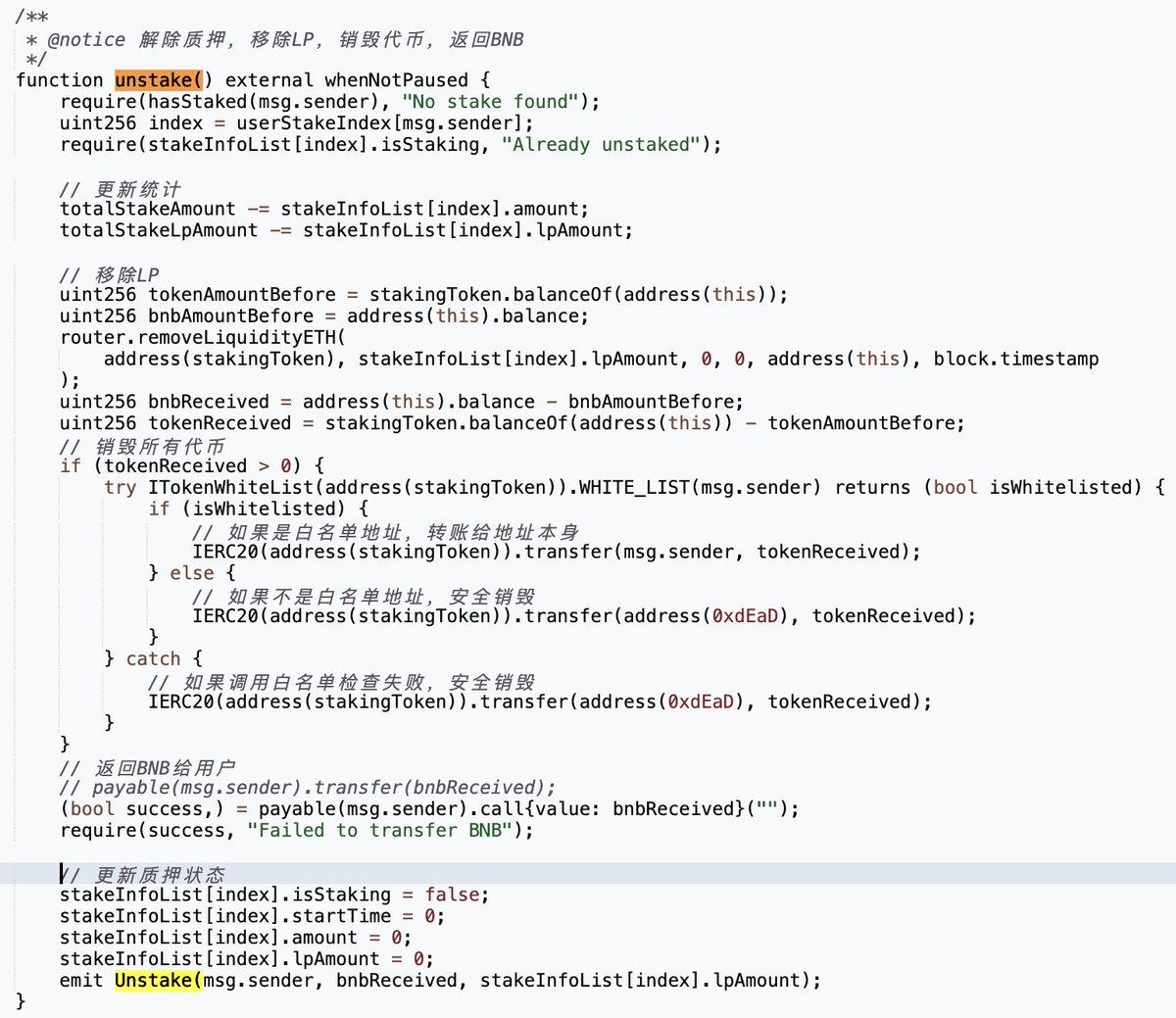
🚨 @VenusProtocol on BSC was exploited for ~$3.7M on March 15. Root cause: supply cap bypass via direct ERC-20 transfers to a vToken contract, a known Compound V2 design flaw previously flagged in Venus’s own Code4rena audit. Example tx: bscscan.com/tx/0x5aede60c7… ~50 exploit transactions in total. 🧵






🚨 URGENT: 7,000+ users just got hacked through a once "harmless" browser extension The QuickLens Chrome extension (formerly Google Lens) was SOLD to hackers who injected malware in v5.8 and auto-pushed it to victims. What they stole: - Login credentials - Session tokens - Crypto wallet seed phrases - Deployed fake Google updates to install backdoors This is a supply chain attack. Hackers bought a legitimate extension and weaponized the auto-update system. No phishing needed when malware delivers itself. 🛡️ PROTECT YOURSELF NOW: ✅ Audit your extensions TODAY (Chrome → More Tools → Extensions) ✅ Remove anything you installed >6 months ago and don't actively use ✅ NEVER paste commands into the terminal without understanding them ✅ Move serious funds to hardware wallets, like Keystone. ✅ Use separate browsers for crypto vs. casual browsing The extension marketplace is the new attack vector. Your browser is a weapon pointed at your wallet. RT to save someone's crypto 🔁