Sabitlenmiş Tweet

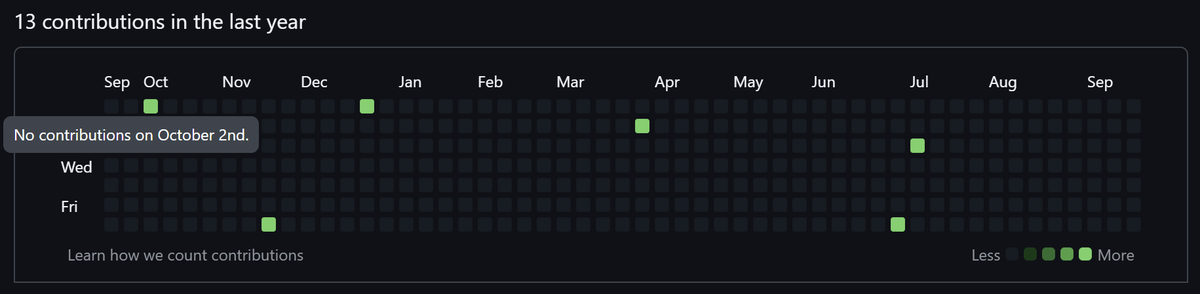
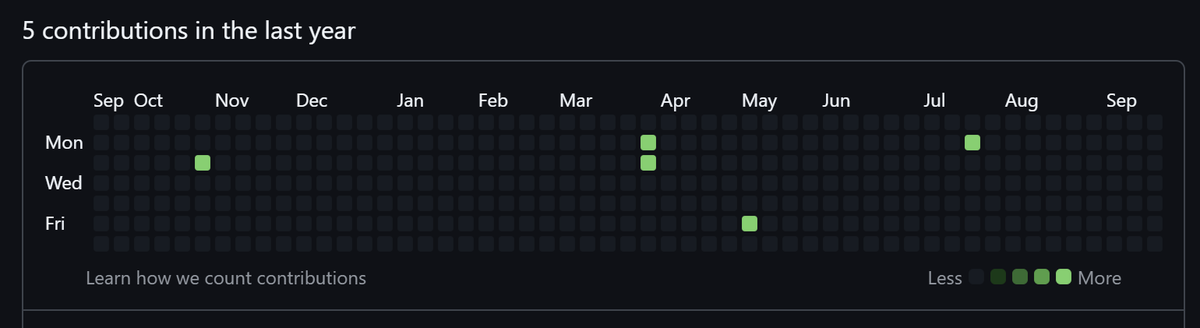
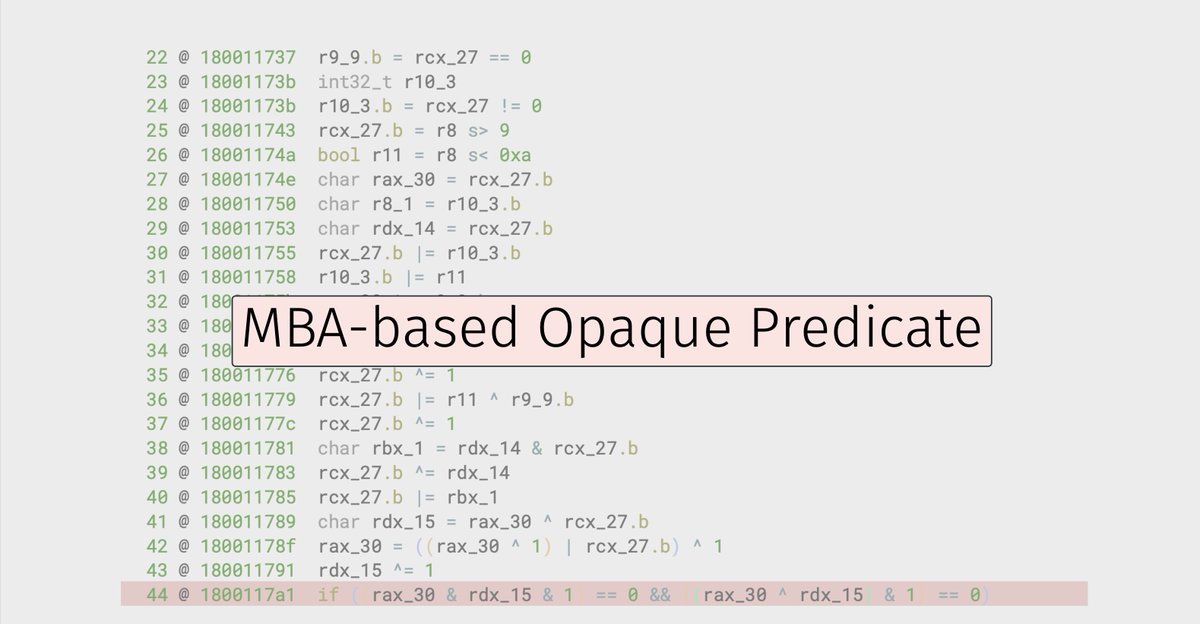
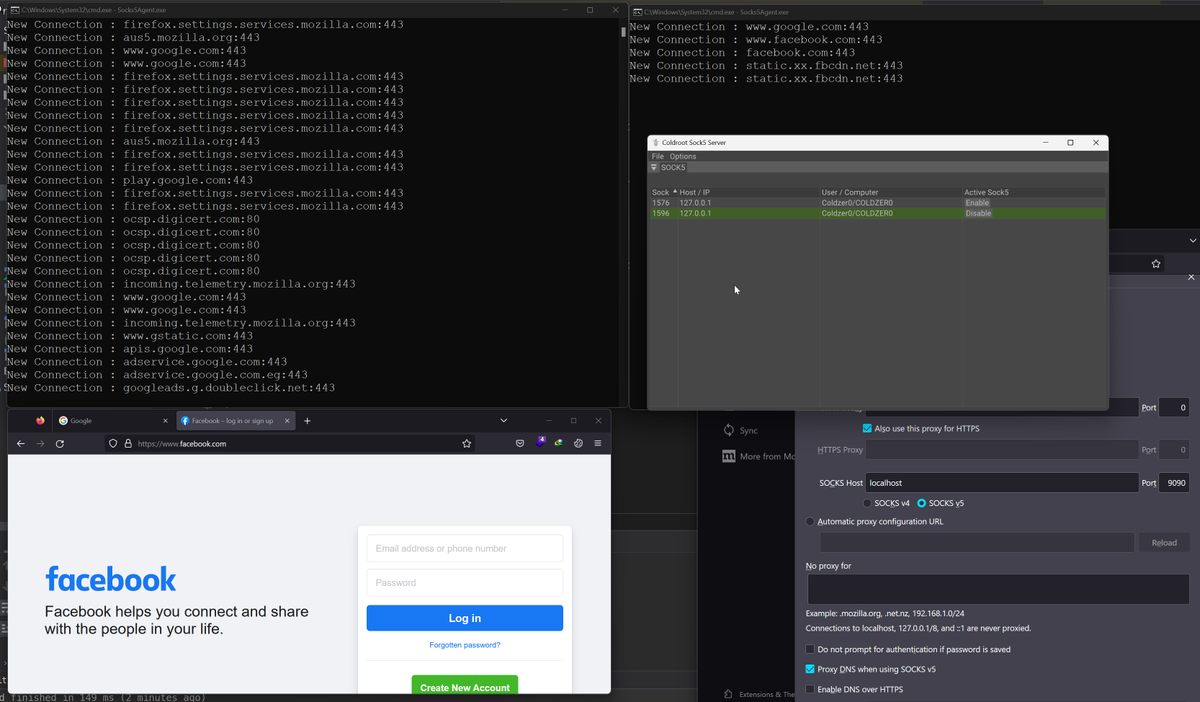
Just Finished the Sock5 Server GUI using ImGui 😎
Keep in mind that the code is a massive pile of spaghetti
So there will be BUGS 🐞 a lot of it 😂
github.com/Coldzer0/Rever…
#ImGUI #CPP #Sock5 #Coldzer0 #ReverseProxy #cybersecurity #redteam

English