

Sam Thomas
682 posts

@xorpse
Chief Scientist @binarly_io. Program analysis. Reverse engineering. Backdoor detection.



We @binarly_io just open-sourced our VulHunt framework at @REverseConf! GitHub: github.com/vulhunt-re/vul… Documentation: vulhunt.re/docs Slack: join.slack.com/t/vulhunt/shar… vulhunt.re

we will present our work on practical binary type recovery at ACM CODASPY '26! prior work rarely focused on applicability: too slow, no meaningful filtering mechanisms, unsound struct recovery we address these gaps and present a system for headless type recovery at scale


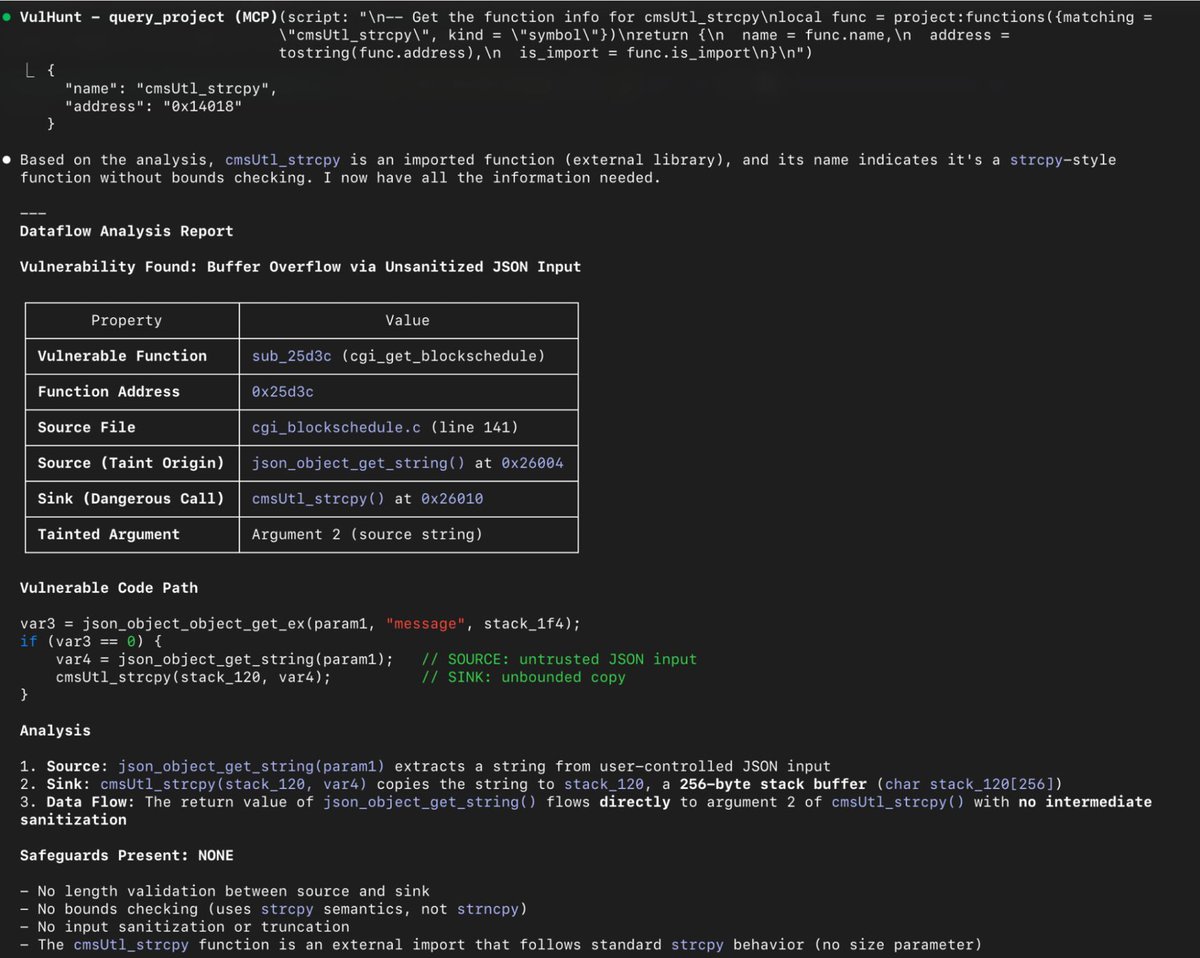
We @binarly_io just open-sourced our VulHunt framework at @REverseConf! GitHub: github.com/vulhunt-re/vul… Documentation: vulhunt.re/docs Slack: join.slack.com/t/vulhunt/shar… vulhunt.re




As part of our vulhunt.re release, we've also dropped few rules! First up is a rule to detect a #LogoFAIL variant (CVE-2023-40238) in a UEFI DXE driver for BMP decoding... Test case(s): github.com/vulhunt-re/tes… Rule: github.com/vulhunt-re/rul…

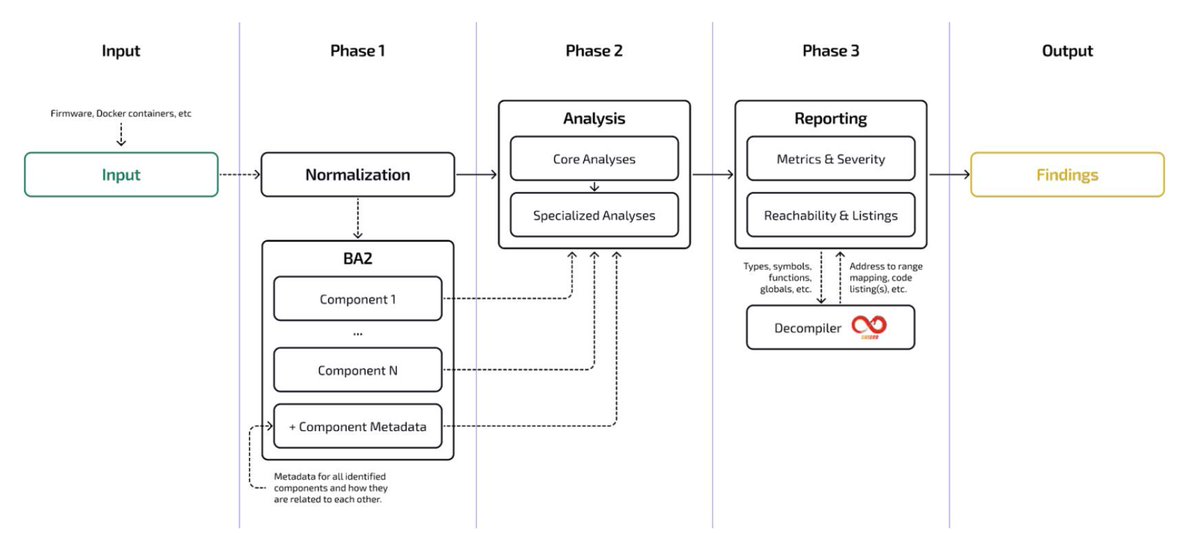
This year at @REverseConf, we’re dropping something special, a project we’ve been heads-down on for a while that boosts semantic-level binary detection with reachability + taint analysis. Like CodeQL/Semgrep, but for binaries. VulHunt use cases: Vuln REsearch: binarly.io/blog/vulnerabi… Detection Eng: binarly.io/blog/vulhunt-i… VH Intro: binarly.io/blog/vulhunt-i…

As part of our vulhunt.re release, we've also dropped few rules! First up is a rule to detect a #LogoFAIL variant (CVE-2023-40238) in a UEFI DXE driver for BMP decoding... Test case(s): github.com/vulhunt-re/tes… Rule: github.com/vulhunt-re/rul…