CyberSec retweetledi
CyberSec
1.1K posts


CyberSec
@CyberSec84
Cybersecurity and hacking news for everyone.
Katılım Aralık 2020
31 Takip Edilen2.8K Takipçiler
CyberSec retweetledi
CyberSec retweetledi
CyberSec retweetledi

@ApizCrypto I was reading your ANN in altcoinstalks.com and I saw that you have a text error on the website, in the box "How many coins or tokens exist currently, how many will be in the future and when will they be created?"
English

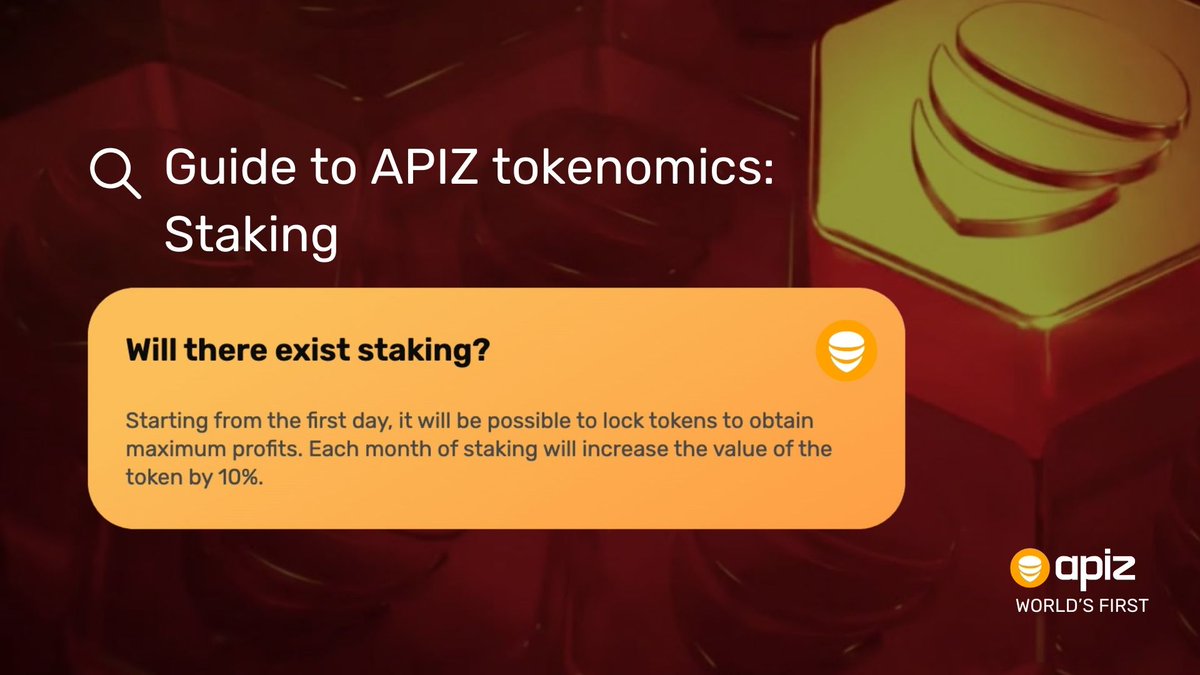
APIZ dedicates 50% of profits to buy back #tokens, boosting #tokenomics with offline business success. Stakers of APIZ tokens get these, earning more based on stake size and duration—up to 60 months with a 10% reward boost per month. #crypto #beewithapiz
English

This emphasis on combating fraud appears to be a strategic move to garner support from China, tired of being targeted in “pig slaughter” scams, where online fraud victims are coerced into becoming internet scammers.
#Scams #Government #Myanmar
cybersec84.wordpress.com/2024/01/10/pop…
English

The post-exploitation toolkit is then employed to download the AnyDesk remote desktop application from a network share, facilitating access to the machine.
#Cybersecurity #Hacking #MicrosoftSQL #TurkishHackers
cybersec84.wordpress.com/2024/01/10/tur…
English

By employing this method, threat actors can exploit compromised machines for information and cryptocurrency theft, as well as unauthorized mining.
#Cybersecurity #Youtube #Malware #LummaStealer
cybersec84.wordpress.com/2024/01/10/lum…
English

The affected websites, linked to the NoName ransomware group, experienced connectivity issues, displaying error messages like “403 Forbidden.”
#Cybersecurity #Ukraine #NoName #DDoS #Cyberattack
cybersec84.wordpress.com/2024/01/09/non…
English

Capital Health is currently investigating whether any data was compromised during the cyberattack.
#Cybersecurity #Cyberattack #Healthcare #Ransomware #LockBit
cybersec84.wordpress.com/2024/01/09/loc…
English

The company assured that efforts were underway to restore normal business operations swiftly and to understand the full extent of the incident.
#Cybersecurity #Cyberattack #loanDepot #US #Ransomware
cybersec84.wordpress.com/2024/01/09/maj…
English

According to 23andMe, this negligence allowed attackers to initiate a credential stuffing campaign by using usernames and passwords obtained from unrelated security breaches on other websites.
#23andMe #Cybersecurity #DataBreach
cybersec84.wordpress.com/2024/01/08/23a…
English

The rise of cyber criminal operations, facilitated by global digital infrastructure, has created challenges for law enforcement due to the involvement of victims and perpetrators in diverse locations.
#Cybersecurity #FBI
cybersec84.wordpress.com/2024/01/08/fbi…
English

While state-sponsored hacking groups from Iran and Israel have traditionally dominated the Middle East’s threat landscape, indigenous groups like Anonymous Arabic continue to thrive in the cybercrime markets
#Cybersecurity #Syria #RAT #SilverRAT #Trojan
cybersec84.wordpress.com/2024/01/08/syr…
English

This latest incident follows a trend of cyberattacks targeting small governments across the United States throughout 2023.
#Cybersecurity #Cyberattack #Government #US #Ransomware #Virginia
cybersec84.wordpress.com/2024/01/08/cyb…
English

Over the past few months, UAC-0050 has wielded the same Trojan in at least three distinct phishing campaigns. One of these attacks introduced an information-stealing program named Meduza Stealer.
#Cybersecurity #Malware #Stealer #RAT #UAC0050 #Ukraine
cybersec84.wordpress.com/2024/01/07/rem…
English

Following the security breach, the cybercriminal created a counterfeit webpage on Mandiant’s account, mimicking the appearance of the official Phantom website.
#Cybersecurity #Cyberattack #Google #X #Mandiant #Phantom #Hacking
cybersec84.wordpress.com/2024/01/07/hac…
English

In a recent update, the university disclosed that internet and WiFi services for resident students remain non-operational, and payment terminals for credit and debit card transactions are also affected
#Cybersecurity #Cyberattack #MUN #Canada #Ransomware
cybersec84.wordpress.com/2024/01/07/mem…
English

Organizations are advised to enforce strong password policies, implement two-factor authentication (2FA), limit login attempts and monitor SSH traffic.
#Cybersecurity #Cyberattack #Cyberespionage #Netherlands #SeaTurtle #HackerGroup
cybersec84.wordpress.com/2024/01/06/sea…
English

The attackers utilized a combination of tools during the campaign, including an executable (NACL.exe) requiring administrator privileges to erase data by removing the boot signature.
#Cybersecurity #Cyberattack #Albania #NoJustice #Malware #HackerGroup
cybersec84.wordpress.com/2024/01/06/no-…
English


