Luis Vacas de Santos retweetledi

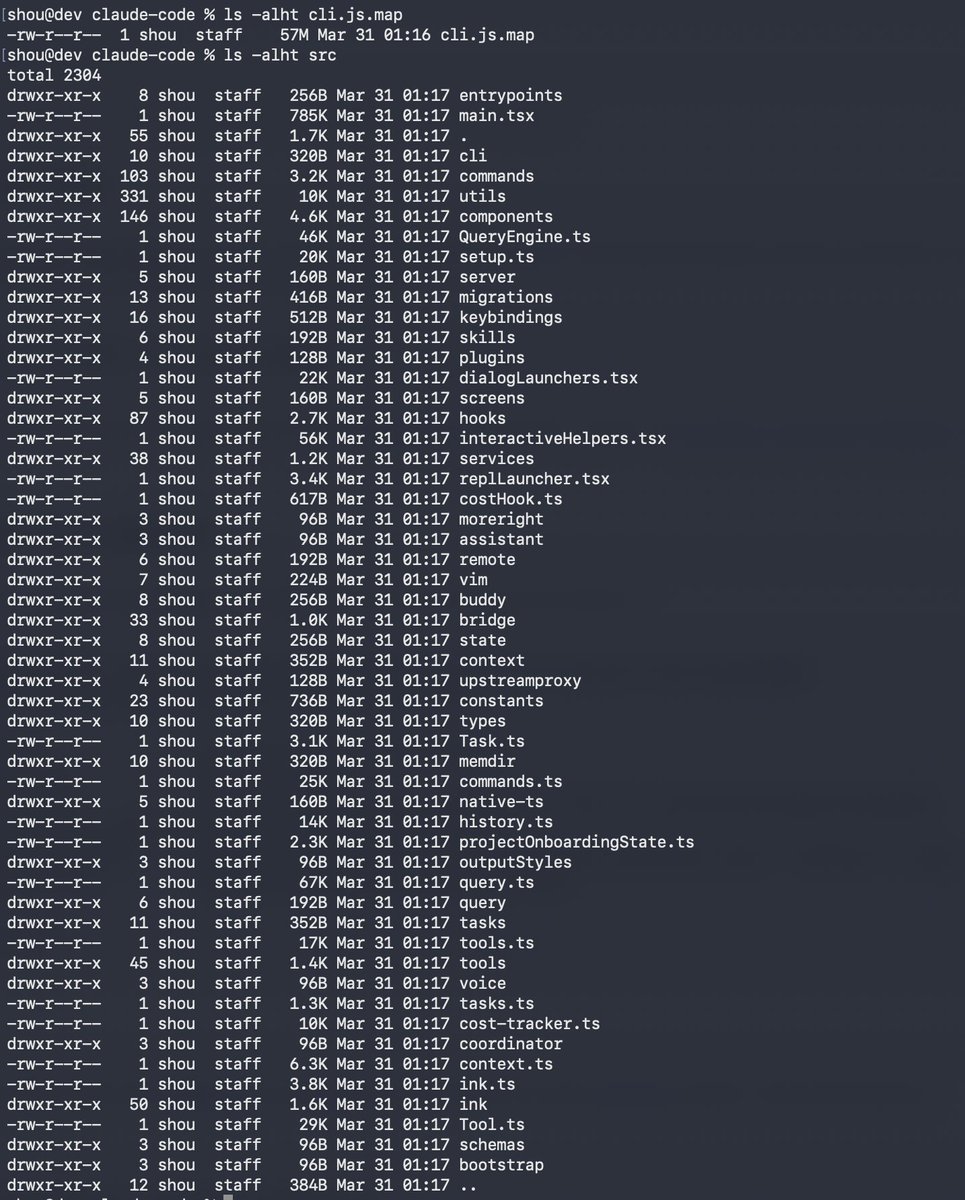
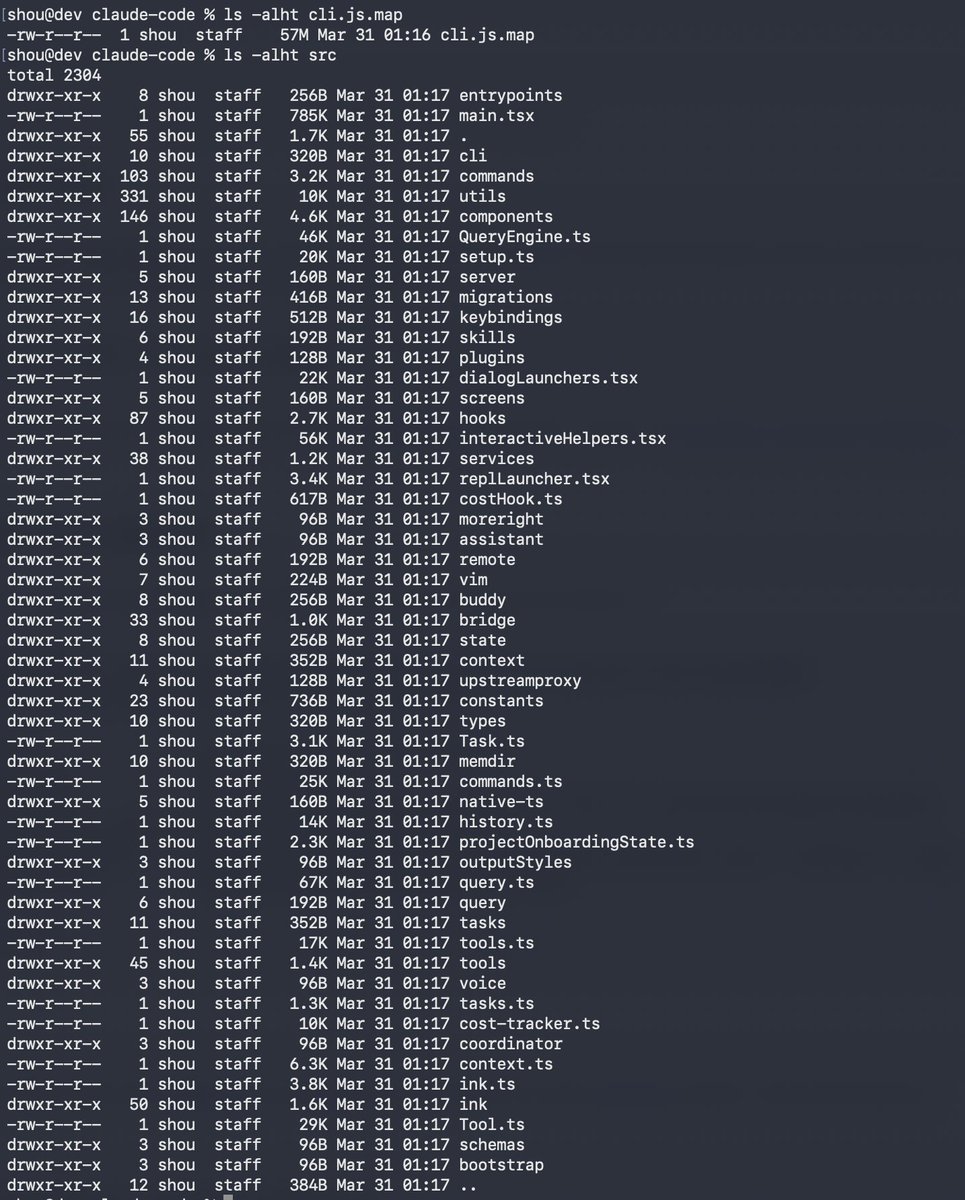
Claude code source code has been leaked via a map file in their npm registry!
Code: …a8527898604c1bbb12468b1581d95e.r2.dev/src.zip
English
Luis Vacas de Santos
1.8K posts


@CyberVaca_
Cybersecurity Analyst, Evil-WinRM Creator