Adetola Samuel
628 posts


Adetola Samuel
@Cyber_Sam01
Cybersecurity 🌿 | Security Engineer (Aspr) | God's Masterpiece
Space Katılım Temmuz 2022
505 Takip Edilen127 Takipçiler

@FadilulahA999 @Ahmed___khaan @Amospikins @CompTIA @crownbefitsme07 @cyb3rshi3ld @cyber_rekk @cyberwithdani Scaling up, free resources aren't really organised. One just has to search for the concept one intends to learn and instead of one thorough path. For the paid, I would say TryHackMe
English

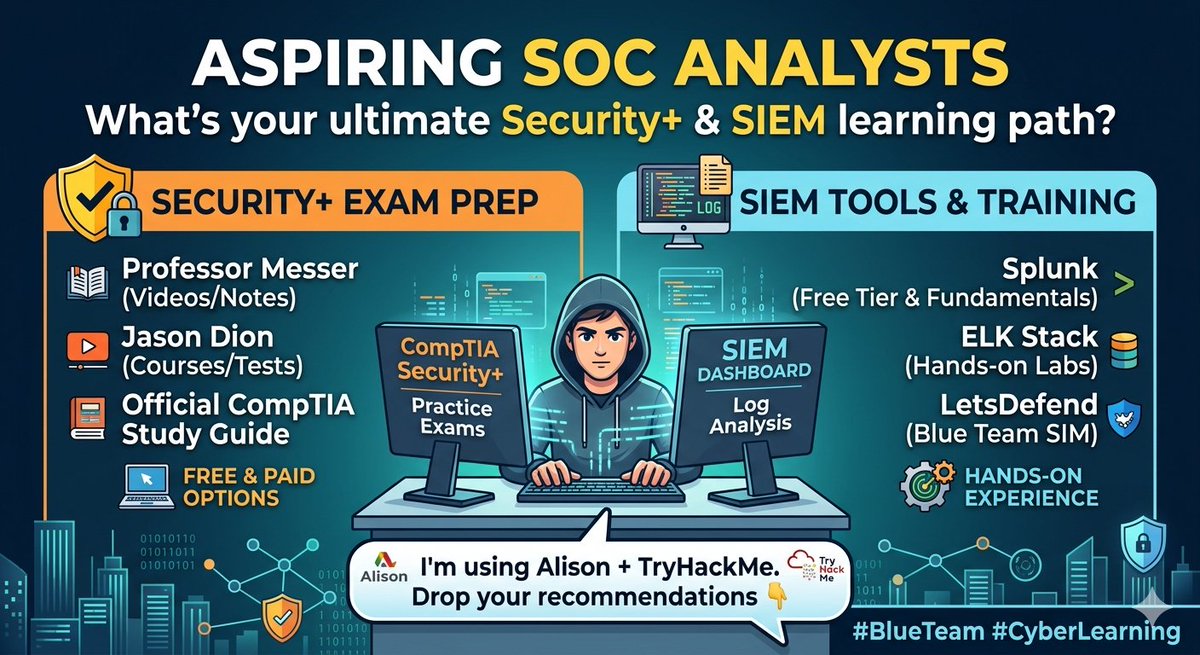
I am Aspiring SOC Analysts — what's the best free/paid resource that helped you with Security+ or SIEM tools? I'm using Alison + TryHackMe. Drop your recommendations 👇 #BlueTeam #CyberLearning #juniorsocanalyst
English

How it ended👇🏾:
@jay_hunts

Adetola Samuel@Cyber_Sam01
Day 1/100 #100Daysofcybersecurity I started with The Windows Command Line. In my learning I was able to cover Command prompt and its command, how to work on files and directories ( create, move copy and the likes), getting help and navigate through system via HTB. #blueteam
English

A wrap! X won't let me share my full reflection, so catch up on the complete journey and what I learned on LinkedIn: linkedin.com/posts/adetola-…: linkedin.com/posts/adetola-…
Adetola Samuel@Cyber_Sam01
Day 1/100 #100Daysofcybersecurity I started with The Windows Command Line. In my learning I was able to cover Command prompt and its command, how to work on files and directories ( create, move copy and the likes), getting help and navigate through system via HTB. #blueteam
English

Day 1/100 #100Daysofcybersecurity
I started with The Windows Command Line. In my learning I was able to cover Command prompt and its command, how to work on files and directories ( create, move copy and the likes), getting help and navigate through system via HTB.
#blueteam

English

Day 100 #100Daysofcybersecurity 🎉
I solved a challenge room, Tempest. It was a full kill-chain analysis on a Windows OS. I used Sysmon View, EvtxECmd, Brim, and PowerShell ISE to aid my analysis.

English

Day 100 - #100DaysOfCybersecurity 🎉 (Final Day)
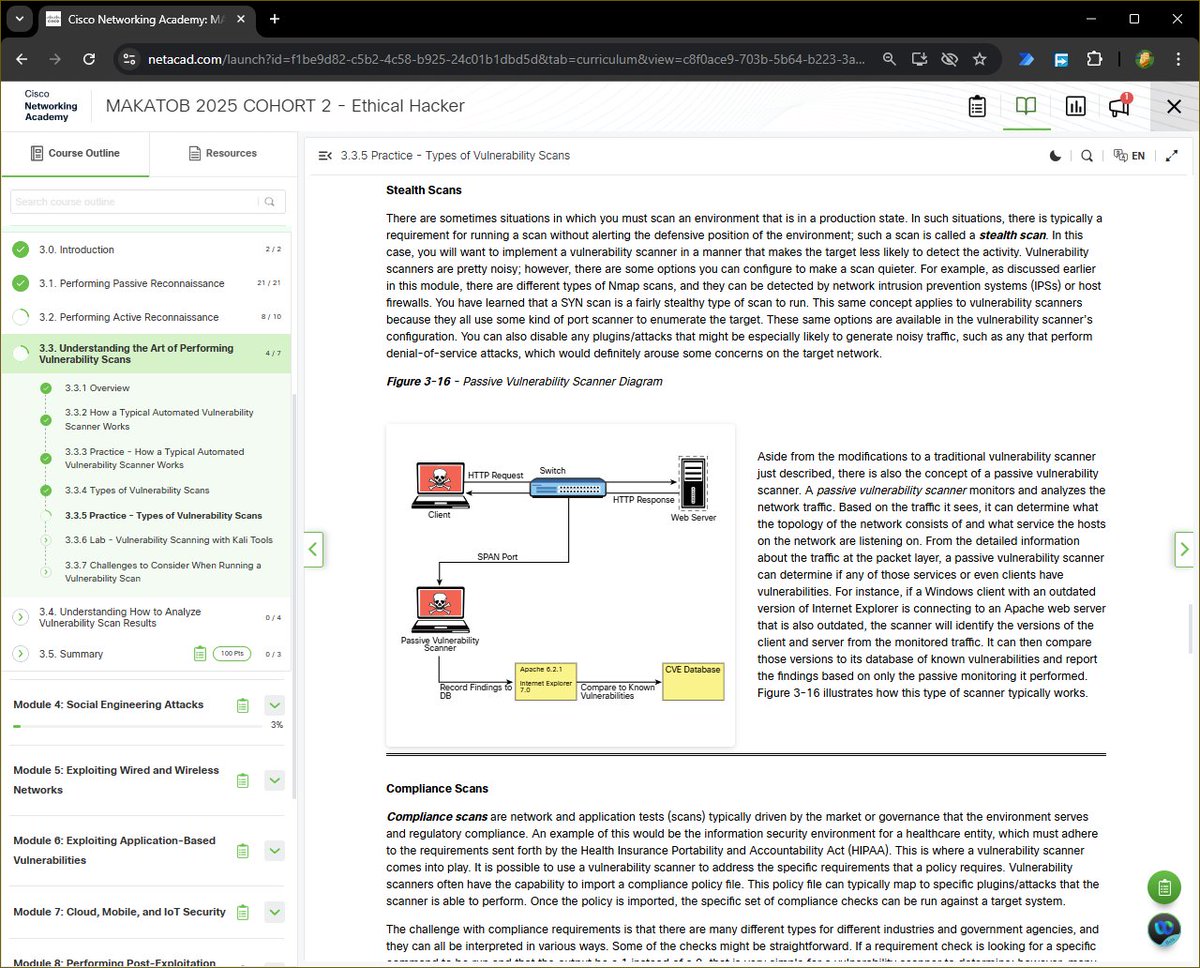
Today marks the completion of my 100 Days of Cybersecurity Challenge, and I wrapped it up by diving into a critical concept in vulnerability management: Types of Vulnerability Scans.
After building a strong foundation in reconnaissance, and packet crafting, today I tied everything together by exploring how vulnerabilities are systematically discovered in real-world environments.
What I Learned Today:
Vulnerability scanning is about strategy, context, and accuracy.
Here are the key scan types I explored today:
Unauthenticated Scans
Simulate an external attacker’s view.
-Useful for identifying exposed services, but limited visibility.
Authenticated Scans
Provide deeper insight by logging into the system (with credentials).
-More accurate results, fewer false positives.
Discovery Scans
Focus on identifying the attack surface (hosts, ports, services).
- This builds directly on tools like Nmap.
Full Scans
Run all available checks and plugins.
- Powerful but can be noisy and resource-intensive.
Stealth Scans
Designed to reduce detection (e.g., SYN scans, reduced noise).
- Important in production or monitored environments.
Compliance Scans
Validate systems against regulatory standards (e.g., security policies).
- Critical for enterprise and regulated industries.
⚙️ Key Insight
Vulnerability scanners follow a structured workflow:
- Discover hosts & services (often using tools like Nmap)
- Identify software versions
- Match against known vulnerabilities (CVE databases)
- Generate findings (which must be validated)
⚠️ One major lesson:
False positives are real, and validation is just as important as detection.
🧠 Why This Matters
This ties directly into everything I’ve been learning:
Recon - identifies targets, builds profile
Enumeration - reveals services
Scanning - uncovers weaknesses
It’s the bridge between finding systems and actually assessing their security posture.
🚀 Reflection - 100 Days Later
What started as curiosity has evolved into structured, hands-on cybersecurity practice.
Cybersecurity goes beyond tools, it’s about understanding systems, thinking critically, and validating everything.
This is just the beginning.
@jay_hunts @ireteeh @segoslavia
#RedTeamer #Cybersecurity #EthicalHacking #VulnerabilityAssessment #Nmap #RedTeam #LearningInPublic

English

Day 99 #100Daysofcybersecurity
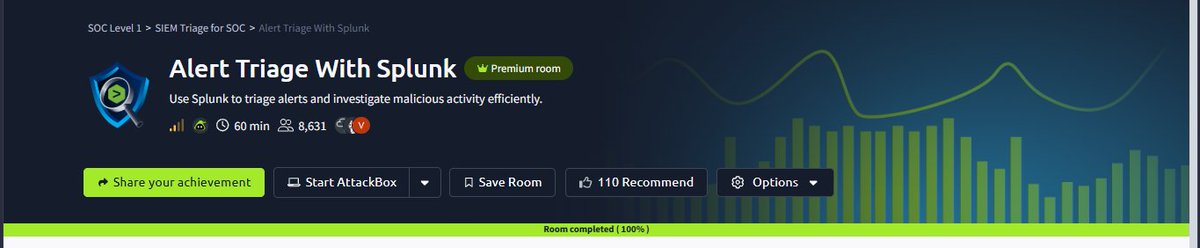
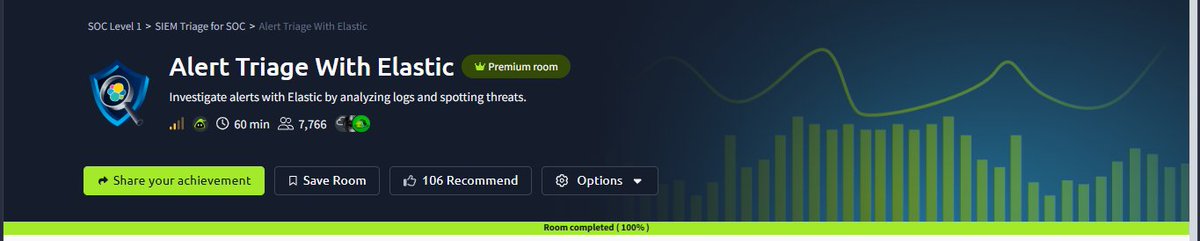
I worked with siem tool, splunk and elastic elk for log analysis.


English

I intended to share this yesterday, but the exhaustion caught up with me and I slept off. I share a post on linkedin yesterday bytheway, kindly view it here: linkedin.com/posts/adetola-…
English

Day 97-98: #100DaysOfCybersecurity
Back in Ipajs, where the electricity isn't as constant as it is at Unilag. Over the last few days, I took on a challenge room for malware analysis called Shadow Trace.
Technical Highlights:
...
English

Days 93-96 #100Daysofcybersecurity
The last 4 days had been very taxing for me. First, I had to lock in for my last exam that was yesterday, then a robot design project which I had to defend also. I almost crashed out.

English

