Dan Amodio retweetledi
Dan Amodio
301 posts

Dan Amodio
@DanAmodio
mostly I just hack stuff. 💻🔨
Annapolis, MD Katılım Aralık 2010
1.4K Takip Edilen414 Takipçiler
Dan Amodio retweetledi

New blog post outlining a fun phishing technique to look out for!
@cachemoney/exploiting-application-logic-to-phish-internal-mailing-lists-486b94fc2ef1" target="_blank" rel="nofollow noopener">medium.com/@cachemoney/ex…
English
Dan Amodio retweetledi

Want to be part of a great security team and do security research full-time? We've got just the role! Tinder is looking for an experienced researcher to go deep and find new bugs. Learn more about it here! jobs.lever.co/matchgroup/8a7…
English
Dan Amodio retweetledi

Calling all hackers! You can now find the bug of your dreams with @Tinder's #bugbounty program, which has just gone public! Check out their program page for more details: hackerone.com/tinder?type=te… #happyhacking
GIF
English

Forgot I pushed my AWS asset collection script a while ago. I know there are others.. no attempt to overshadow those. It can attempt to enumerate and assume role into all organization accounts to grab external facing stuff. github.com/Contrast-Labs/…
English
Dan Amodio retweetledi
Dan Amodio retweetledi
Dan Amodio retweetledi
Dan Amodio retweetledi
Dan Amodio retweetledi

Ever wondered what it takes to build your own CTF? @clevernyyyy @DanAmodio @SaraKathrynG chatted about this in Labs Weekly #5 - youtube.com/watch?v=HBDM11… #ctf #gamification #appsec #training #security

YouTube
English

Run every repo from a GitHub user through truffleHog to find leaked keys:
curl api.github.com/users/<username>/repos?per_page=1000 | jq '.[].html_url' | xargs -I{} sh -c 'echo {} && truffleHog --entropy false {}' | tee output.txt
English
Dan Amodio retweetledi

I think @ericsyuan response to @zoom_us security concerns is great so far. Let's not forget security is tough and evolves over time. blog.zoom.us/wordpress/2020…
English

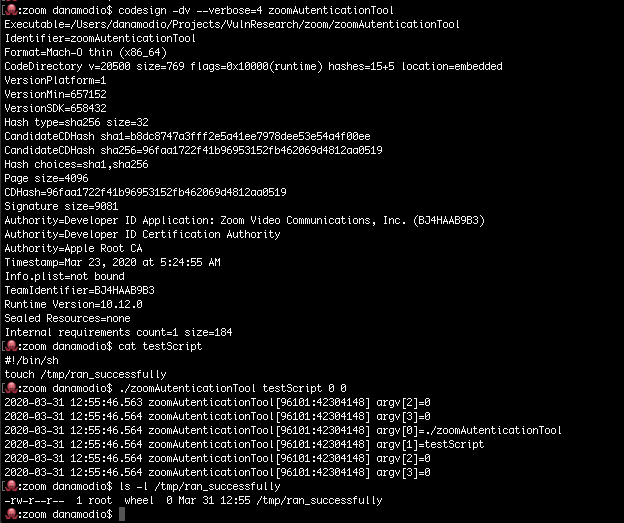
Reposting my reply bc I think it was misleading. zoomAutenticationTool will run whatever script you give it, and ask you to authenticate as System. It's like they wrote their own sudo tool.. Don't think you can weaponize but weird practice.
Felix@c1truz_
Ever wondered how the @zoom_us macOS installer does it’s job without you ever clicking install? Turns out they (ab)use preinstallation scripts, manually unpack the app using a bundled 7zip and install it to /Applications if the current user is in the admin group (no root needed).
English

@dchest Yes I agree. it just still seems really weird their own sudo tool basically. I didn’t prove this as actual gatekeeper bypass delivery for malware would be tricky. But some OSX malware uses similar patterns.
English