Matt Austin
923 posts






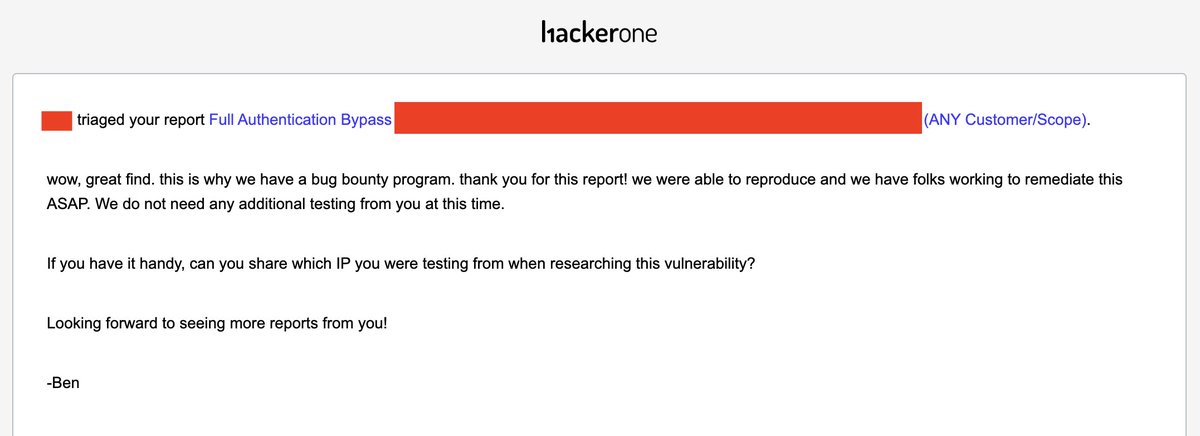
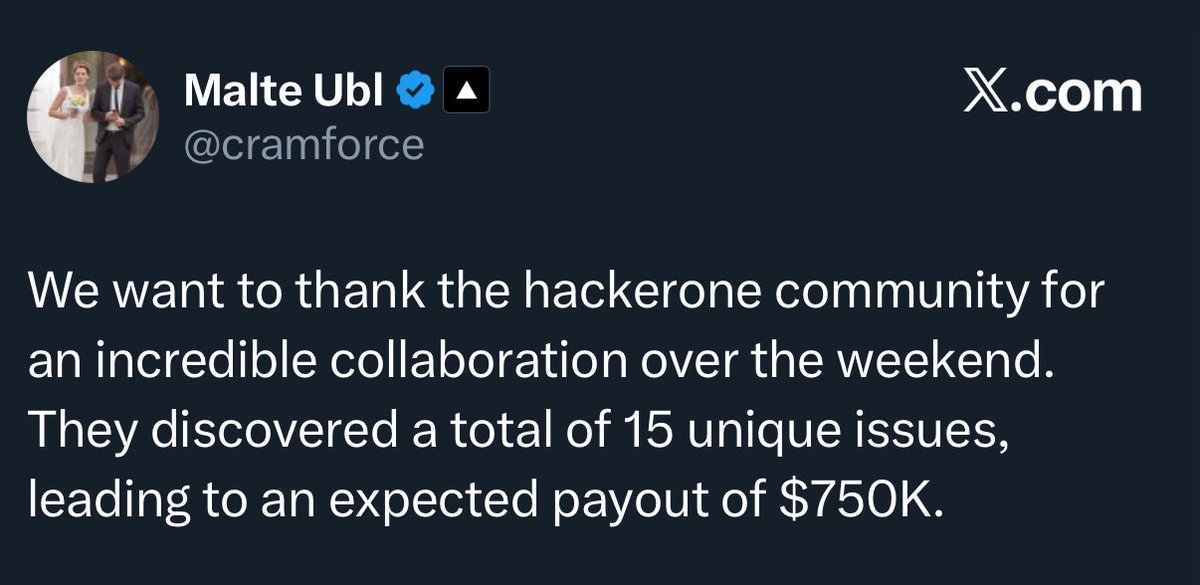
FRUSTRATING bug bounty experience this week (3 crits) 😀🔫 - Default credentials with API gateway access: "Asset was being decommissioned anyway" - Auth bypass exposing employee data: "Our dev team found it that morning, actually" - Hardcoded API key with live access: "Already reported in our legacy Synack program"






The US government just banned consumer routers made outside the US 🙃 theverge.com/news/899172/fc…



The best trophy I received in my bug bounty career, by far! Thanks @swisscom_csirt - it always has been pleasure to work with you all - and happy to see my work appreciated and respected! 9 years of hunting it - 10th one coming soon! 🎂 #bugbounty














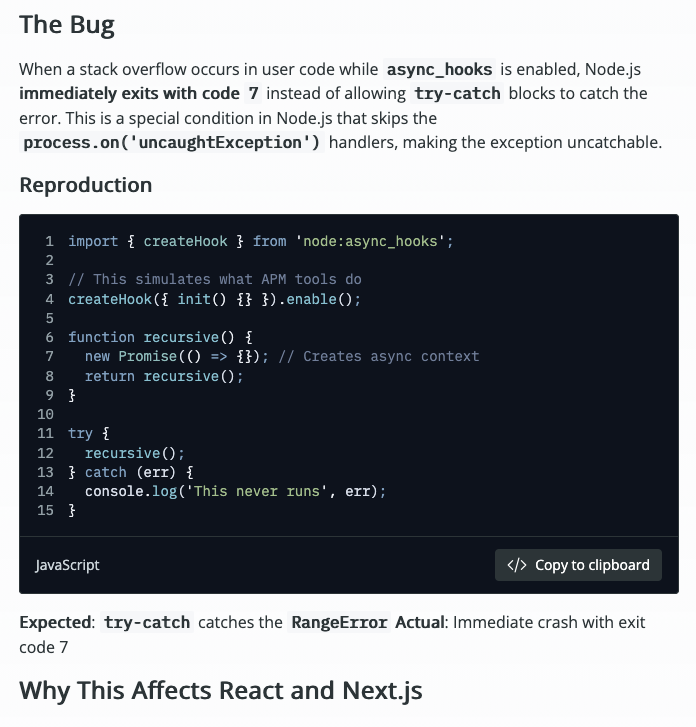
Today, @nodejs published a security release for Node.js that fixes a critical bug affecting virtually every production Node.js app. If you use React Server Components, Next.js, or ANY APM tool (Datadog, New Relic, OpenTelemetry), your app could be vulnerable to DoS attacks. 👇


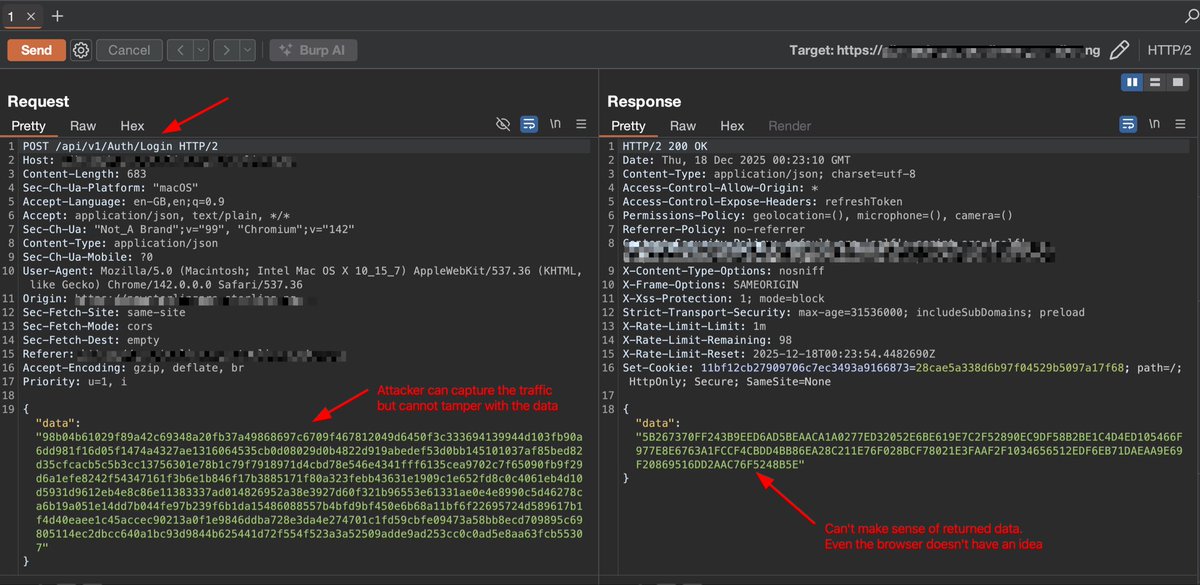
Never thought encrypting your password before sending to your backend was a thing until 2 days ago