
@Dimillian Man! That's a wild relic. We were such skids back then haha ! The TPB wallpaper... priceless 🤣
English
Jean-Pierre LESUEUR
56 posts


@DarkCoderSc
Malware Researcher / Microsoft MVP






Got an email from the FBI once asking if I knew who 'Iceman' was. Someone was using my alias 'Aphex' to deface websites. Pretty sure I know who was behind it...



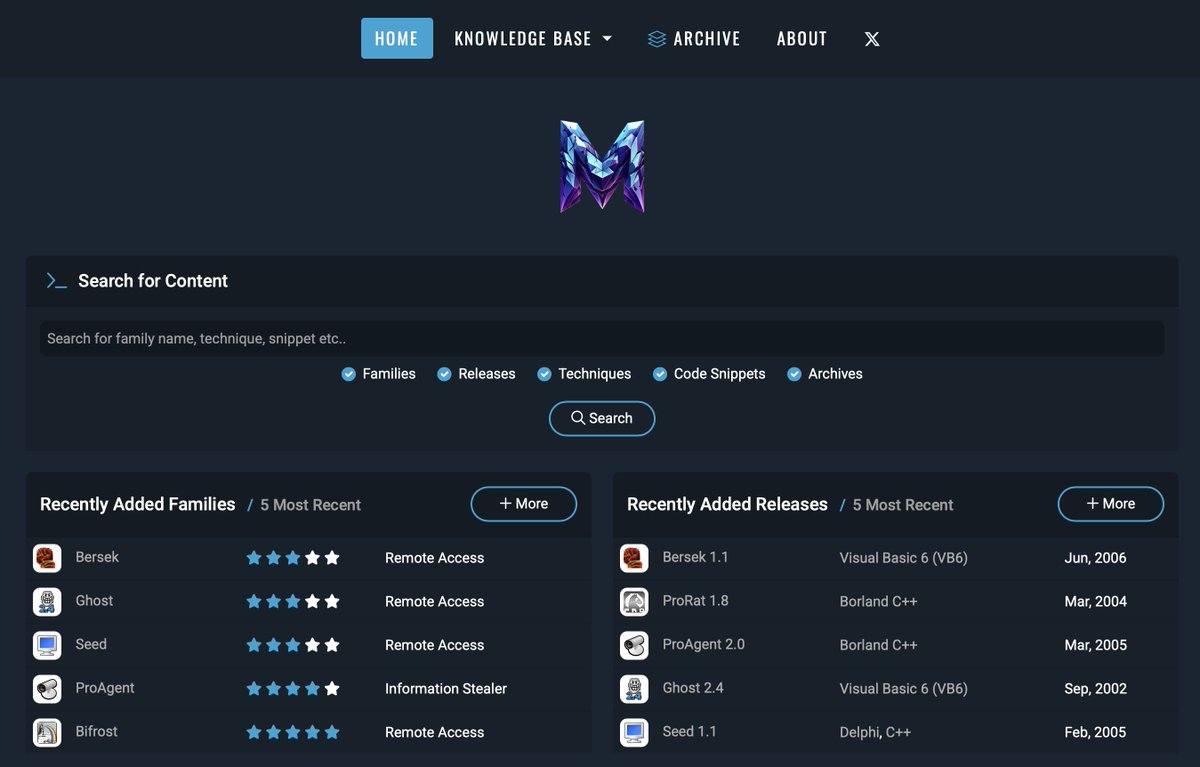
Has anyone ever seen or used this evasion technique? I have been using it for many years and still find it effective (particularly with macro's), so I was surprised to see it continue to work so I decided to document it on Unprotect : unprotect.it/technique/indi… Feedback appreciated!












