Adedoyin retweetledi

Day 15/100 of ZK 🔐
Today we moved to lattice-based cryptography, the backbone of post-quantum security and the go to foundation for powerful Fully Homomorphic Encryption (FHE).
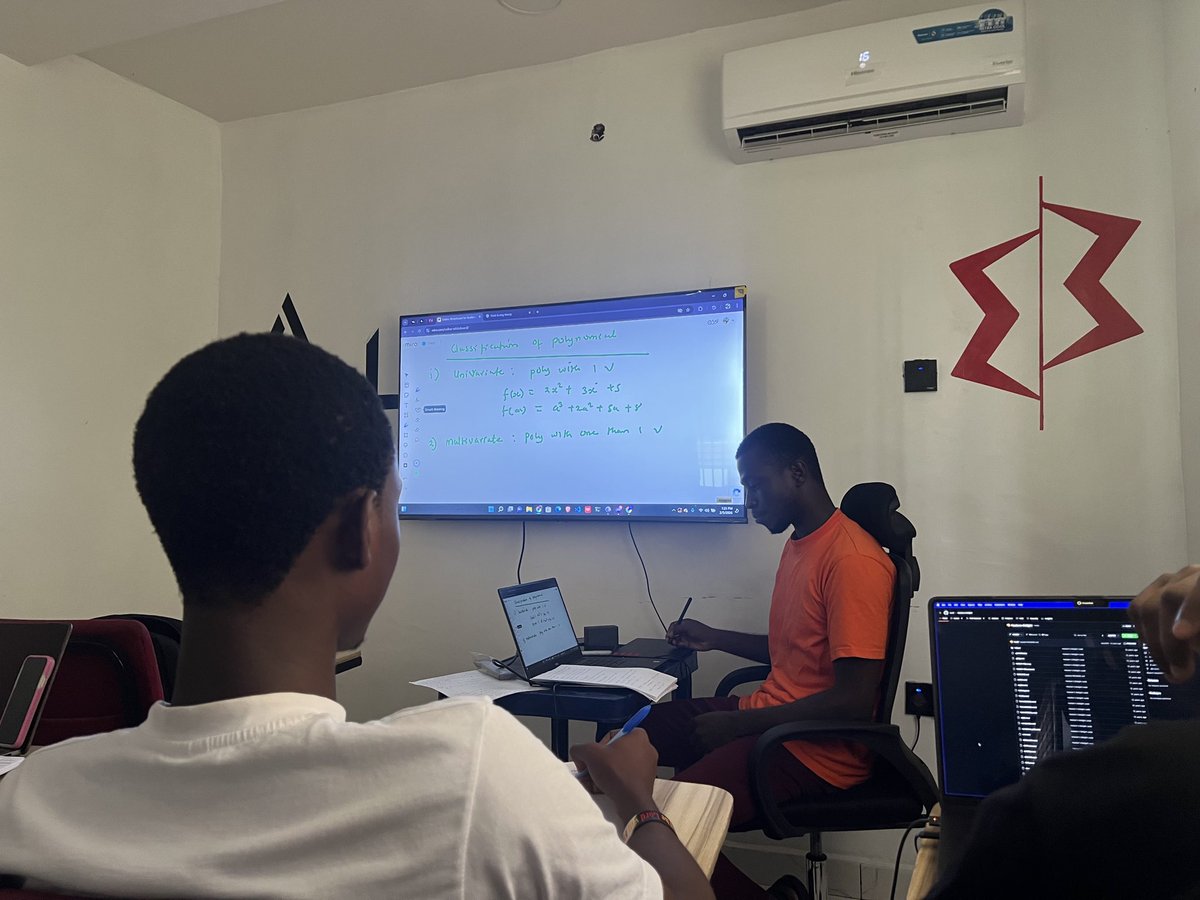
First, lattices in pure math: A lattice is a discrete subgroup of ℝⁿ generated by integer linear combinations of basis vectors. Think of it as an infinite grid of points in high-dimensional space, regular but sparse.
Key hard problems include:
* Shortest Vector Problem (SVP): Find the shortest non-zero vector in the lattice. Brutally hard in high dimensions.
* Closest Vector Problem (CVP): Given a target point (not necessarily on the lattice), find the closest lattice point.
These worst-case problems are believed to resist even quantum attacks, unlike factoring or discrete logs, which Shor's algorithm crushes.
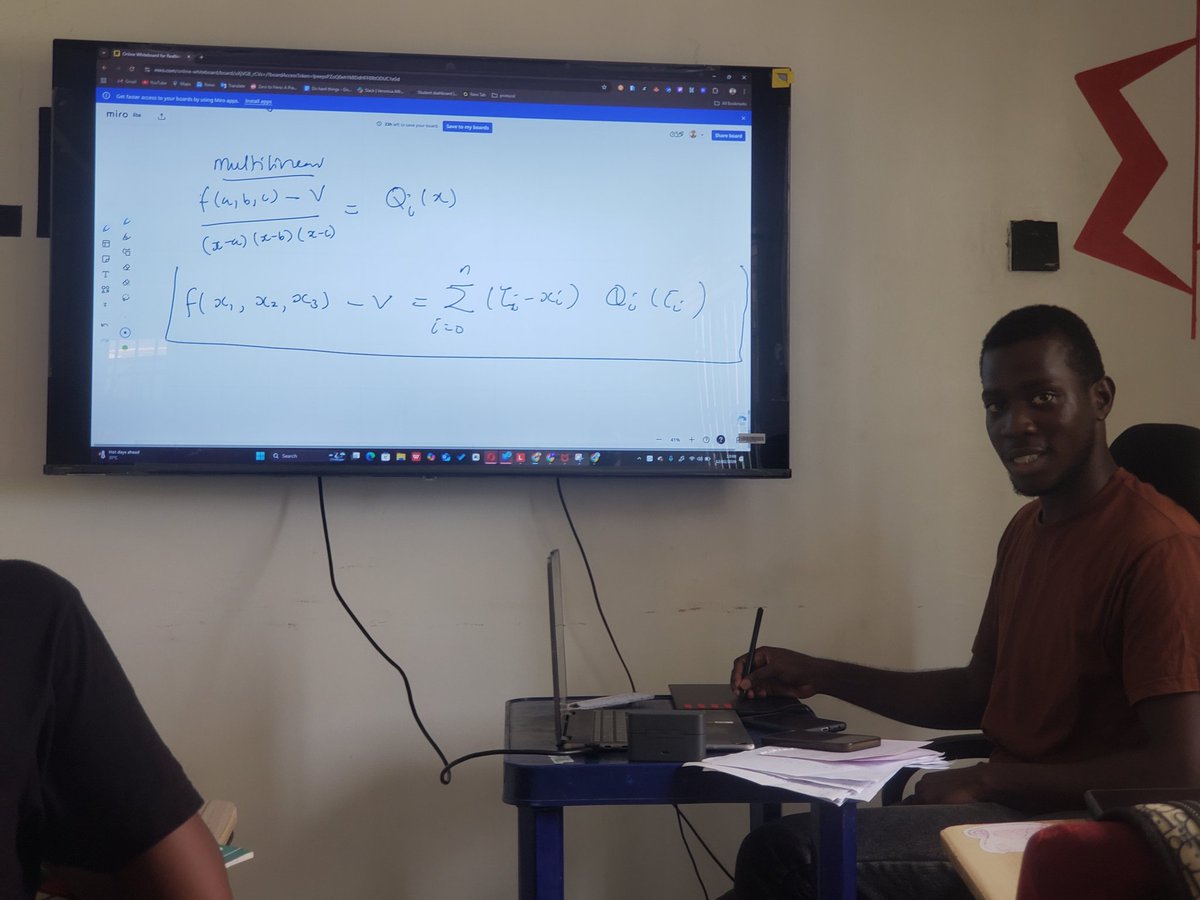
Learning With Errors (LWE): Introduced by Regev, LWE turns these into average case hardness perfect for crypto. Given matrix A ∈ ℤ_q^{m×n}, secret s ∈ ℤ_q^n, and small error e (from a discrete Gaussian or similar), samples are (a_i, b_i = + e_i mod q). Recovering s from many samples is as hard as solving approximate SVP/CVP in the worst case.
Why lattices for FHE? FHE lets you compute on encrypted data without decrypting — add/multiply ciphertexts to get encrypted results. Classic encryption (RSA, ECC) breaks under quantum threats, and even classically, it can't support unlimited homomorphic ops without noise explosion.
Power of FHE: True privacy preserving cloud computing, secure ML on encrypted data, confidential smart contracts — compute anything (arbitrary circuits) while data stays encrypted end-to-end.
Lattice-based schemes dominate practical FHE because LWE/Ring-LWE supports noisy but homomorphic operations, with bootstrapping to refresh noise and enable unlimited depth.
TFHE (Torus FHE): A fast, practical FHE variant working over the torus ℝ/ℤ (real numbers mod 1). It uses TLWE/TRLWE samples (noisy linear equations on the torus) and GSW-style ciphertexts for fast bootstrapped binary gates. TFHE excels at Boolean circuits, with very efficient gate bootstrapping.
Lattice crypto, via LWE and variants, delivers quantum resistant primitives and enables FHE's holy grail: arbitrary computation on encrypted data. The "noise" in LWE hides secrets while allowing meaningful ops, and lattices' hardness survives quantum scrutiny.
Thanks a lot @Dev_esayayo for your taking me through the math behind ZK, and for being patient throughout the process.

English