Aaron D retweetledi

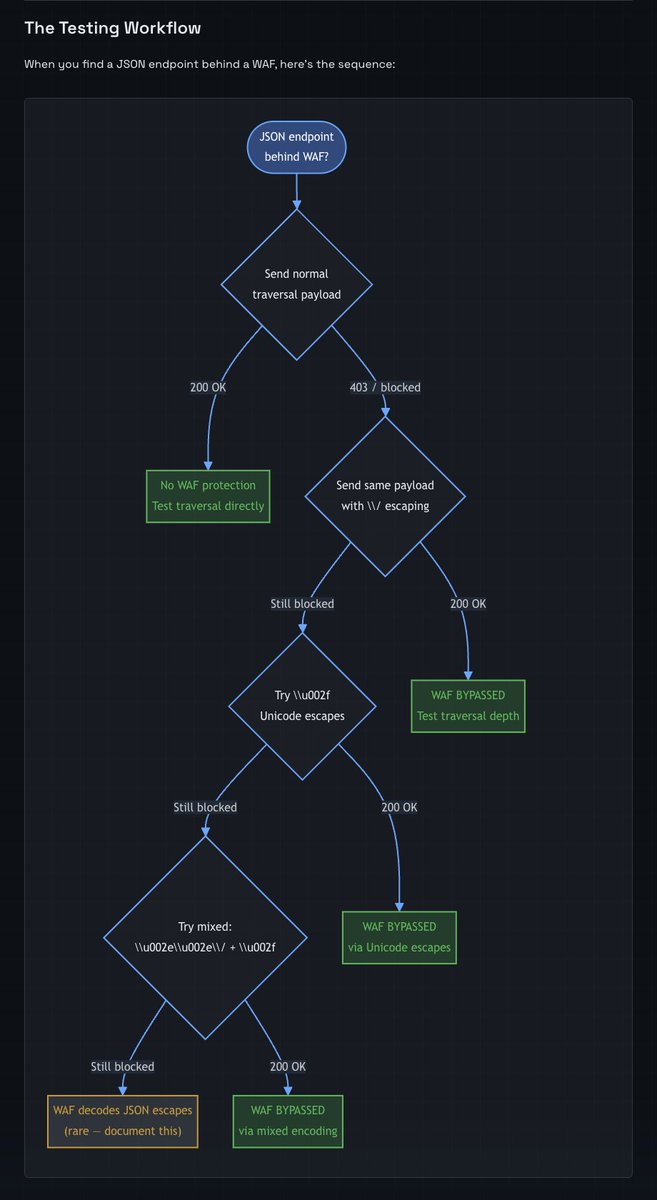
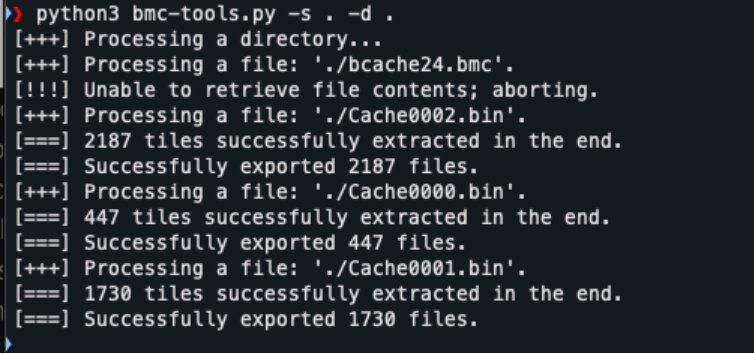
Remote Desktop, Windows quietly saves fragments of what was on screen. Attackers can grab those fragments and reassemble them into readable screenshots using two free tools and about ten minutes. No special privileges required.
scythe.io/scythe-labs/wh…

English