ErrorToCompile
316 posts


ErrorToCompile
@ErrToCompile
busy automating @sigintzero_



We’ve agreed to a partnership with @SpaceX that will substantially increase our compute capacity. This, along with our other recent compute deals, means that we’ve been able to increase our usage limits for Claude Code and the Claude API.


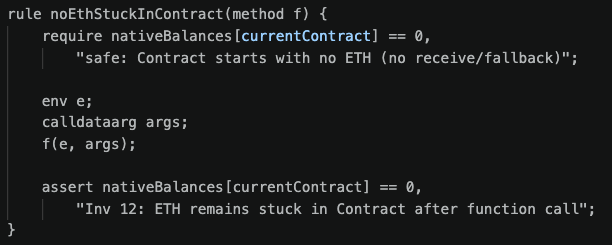
Super stoked to share that we at @sigintzero_ have been awarded a $10k USDG grant from @SuperteamAU as we build toward Tripwire, our 24/7 on-chain monitoring and threat response system for Solana, focused on post-deployment security and real-time protection. Awesome to see support going toward Australian builders pushing the ecosystem forward. We’re now heads down for the final stretch of the @colosseum Frontier Hackathon, focused on delivering it in full and getting it into the hands of teams.



NEW: Claude-powered AI coding agent deletes entire company database in 9 seconds — backups zapped, after Cursor tool powered by Anthropic's Claude goes rogue — Tom's Hardware