🧐
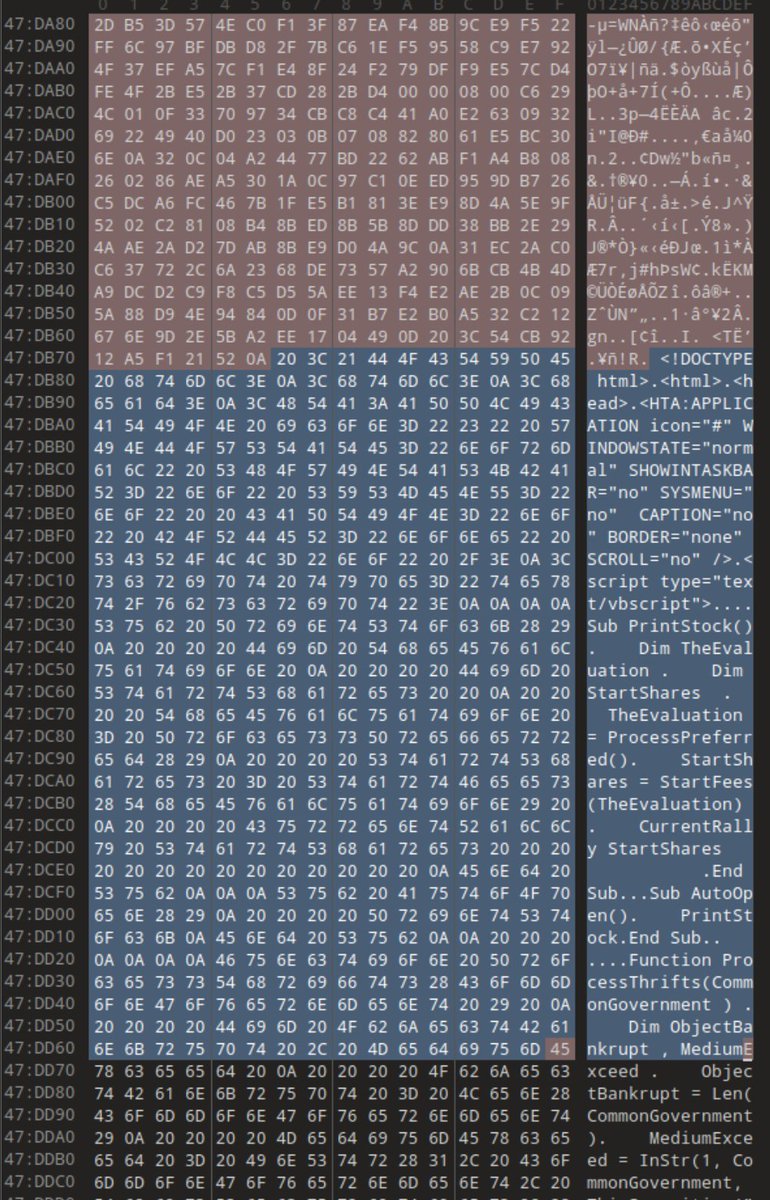
Gentlemen Ransomware group apparently liked our blog.
Reposting it so that others can check it out for themselves:
expel.com/blog/code-sign…

Check Point Research@_CPResearch_
"The Gentlemen" ran a tight RaaS operation. Then they got breached. CPR analyzed the full leak: org structure, access brokers, active CVEs, victim comms, and financials. Real operators, real tradecraft, fully exposed. research.checkpoint.com/2026/thus-spok…
English