FeDEX
1.4K posts

FeDEX
@FetchDEX
{ Christian Hacker } { ceo @aisafe_io } { @WreckTheLine }
Timişoara, România Katılım Ocak 2015
1.6K Takip Edilen1.3K Takipçiler

No timelapse. Just a short gif, but we’re making good progress. Tomorrow, we pour 16 concrete pylons 🙌
GIF
Raul@RaulOnRails
In short. Indie hacking is taking a break, while cabin hacking is in the spotlight.
English
FeDEX retweetledi

Dialed in! Nikolaos Mourousias (@deltaclock), Caue Obici (@caueobici) & Bruno Halltari (@BrunoModificato) of OtterSec used a Code Injection bug to exploit LM Studio in the second round, earning $20,000 and 4 Master of Pwn points. Full win! #Pwn2Own #P2OBerlin
English
FeDEX retweetledi

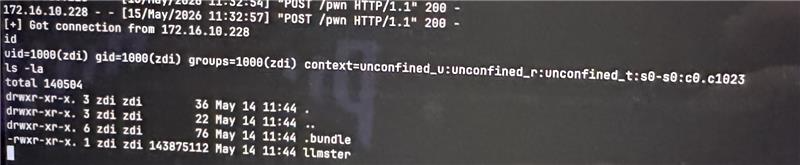
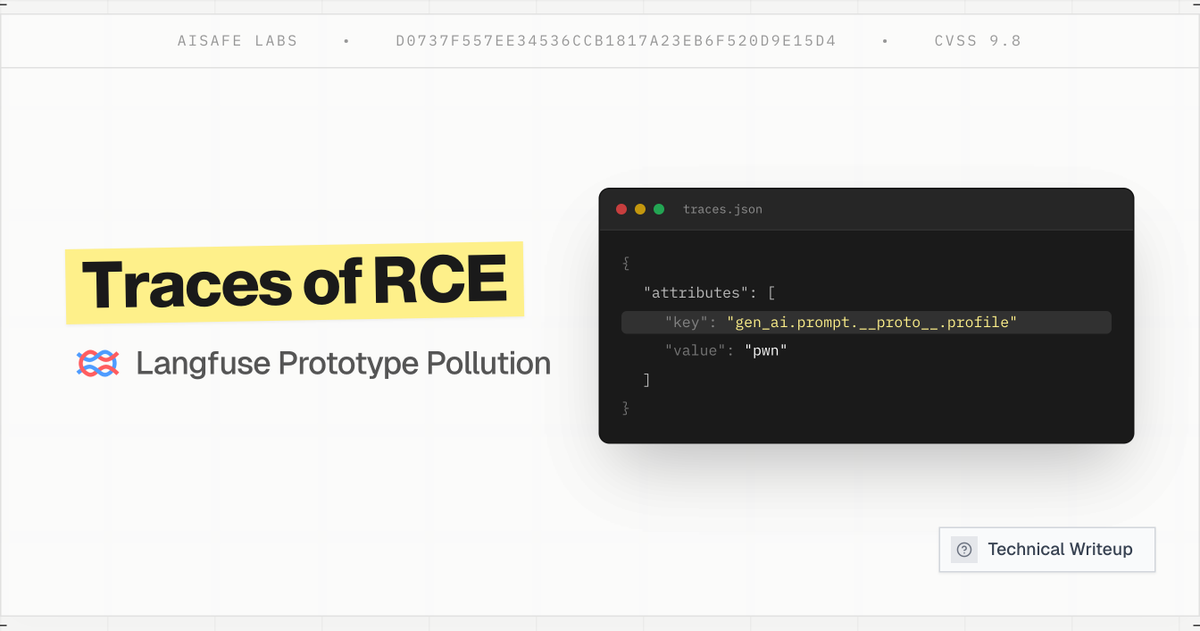
🚨BREAKING: AISafe Labs discovered Remote Code Execution on @langfuse with a single OTel trace request.
The flaw in the OpenTelemetry dotted-attribute expansion allowed unauthorized access to LLM traces belonging to other projects and system compromise via prototype pollution💣
English

I've been doing bug bounty full-time for 4 years.
I just published everything I know. Methodology, AI workflow, templates, prompts, report structure, and the mental side nobody talks about.
It's mostly to prove to you that there is no magic tricks or payload
aituglo.com/guide/bug-boun…
English
FeDEX retweetledi

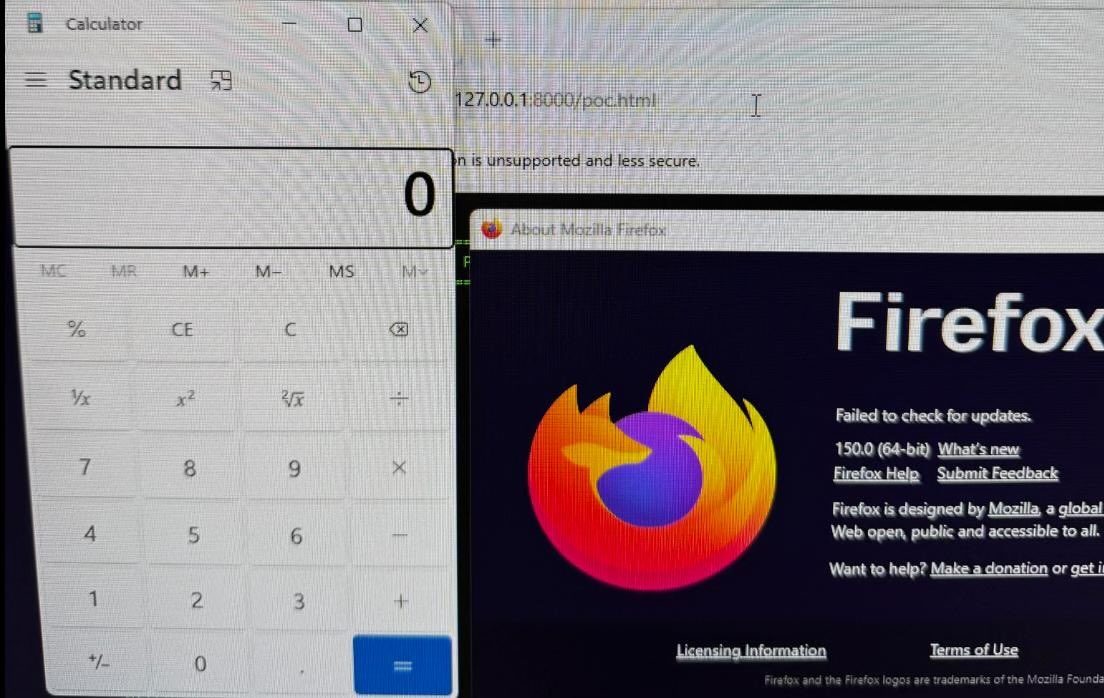
Despite 271 bugs massacred by Anthropic, our renderer rce and sbx escape alive and well ready unless there is sudden patch before p2o ( mean we dont have enough time for prepare new one ) - wish us luck!
blog.mozilla.org/en/privacy-sec…
English
FeDEX retweetledi

Read the full story of how AISafe found a Stored XSS in Immich, a self-hosted photo app with over 98k GitHub Stars ⭐️
aisafe.io/blog/cve-2026-…
English

I would take other side that vibecoding will be responsible for a flood of security vulnerabilities.
no matter how good the models get at finding security vulnerabilities, you can't cover all the grounds.
your security token budget is limited, while the exploitation paths are many. more LoC is never something to be proud of, it means you're expanding your attack surface by orders of magnitude and getting pwned like context ai.
English
I miss the old internet
Anthony Sistilli@sistilli
startup fraud is just... legal now FaaS /fas/ • noun Fraud, sold as a service.
Timişoara, România 🇷🇴 English

@LakersDailyCom @HoustonRockets Why you scared? You said a couple minutes ago that Luke does a better job than Luka so KD coming back shouldn’t scare you no?
English

We won’t bring back Luka if you don’t bring back KD @HoustonRockets
English
FeDEX retweetledi
FeDEX retweetledi
FeDEX retweetledi
FeDEX retweetledi
FeDEX retweetledi

@hyperbridge Delete your account, dissolve the protocol, fire everyone and go make puzzles or something

English

The issue is the framing of a model that's great at finding bugs, many of which cause crashes that are unlikely to ever amount to anything besides a DoS, while covering the model like it's unleashing an unlimited amount of weaponized 0day.
The paper they released about the Firefox exploit included a disabled sandbox/other defense in depth features.
English

I think it is generally a good idea to take AI company claims about unreleased models with a grain of salt, but at this point the deniers are implying there is an industry-wide conspiracy to let Anthropic claim they are finding zero-day exploits in critical software with, I guess, a basement full of world-class white hat hackers pretending to be Claude?
Dean W. Ball@deanwball
It’s crazy that some are just straight up in denial about mythos having the capabilities anthropic says it does. Usually the in-denial-about-AI community is able to cloak their views in at least *some* intellectual garb, but this time it’s just, “it’s not real.” Wild. Also sad.
English









