Sabitlenmiş Tweet
ForgeAudit
100 posts


ForgeAudit
@ForgeAudit
Deep security audits for Web3 protocols. Get secured : https://t.co/XQyx5uTFfP
Katılım Mart 2026
28 Takip Edilen74 Takipçiler

One audit doesn't mean your protocol is safe forever.
It means every vulnerability we could find at that point in time has been addressed.
But protocols evolve. New features get added. Integrations expand. Every change shifts the attack surface.
The teams that stay secure aren't the ones who audited once. They're the ones who treat security as an ongoing process.
Every new feature deserves a fresh set of eyes.
Every upgrade is a new risk surface that didn't exist before.
And even after your code is final, bug bounties exist for a reason.
A hundred security researchers looking at your protocol will always catch things a single audit couldn't. Different perspectives, different assumptions, different findings.
One audit is the foundation.
What you build on top of it determines how long it holds.
English

@Scallop_io Side contracts rarely get the same scrutiny as core contracts. But attackers don't make that distinction.
Appreciate the transparency and swift response, this is how it should be handled.
English

🚨 SECURITY INCIDENT NOTICE
We have identified an exploit affecting a side contract related to Scallop’s sSUI spool rewards pool, resulting in a loss of approximately 150K SUI.
The affected contract has been frozen. Our core contracts remain safe and only the sSUI rewards pool was impacted. All other pools are safe.
Scallop will fully cover 100% of the loss.
We are actively investigating and will share further updates soon. Thank you for your patience and continued support. 🐚
English

A few years ago, auditors read code line by line.
Then tools came. Static analyzers, fuzzers, automated scanners. Some auditors resisted it, saying real auditing is manual.
Meanwhile attackers never resisted anything. They adopted every tool that gave them an edge.
If hackers are using AI to find vulnerabilities, and they are, then auditors who aren't using it are already behind.
We can't reject progress. We have to move with it.
We use AI. It makes us faster, gives us more coverage, catches the surface level stuff quickly.
But we don't stop there. Because AI finds patterns. It doesn't find intent. It doesn't understand why a function was built a certain way or what happens when two systems collide under pressure.
That's where humans come in.
That's where the real bugs hide.
The future of smart contract security isn't AI or human.
It's both.
English

@asen_sec This. The ones grinding in silence right now are the ones who'll matter most later.
English

@gurwinder_sui We cover more than just Solidity. EVM is our core but we're not limited to it
English

@ForgeAudit do you guys specialize only in solidity or in other languages?
English

Some of the sharpest builders and auditors in Web3 are still unknown.
Not because they lack skill.
Because they never got the right support.
The builder with a great idea but no network.
No budget for an audit.
No connection that opens the first door.
The auditor with real skills and a growing track record, but never got a real opportunity.
They're out there. Still grinding. Still building in silence.
Web3 moves better when we lift each other up.
Support the builders around you.
Back the auditors still finding their footing.
Share their work. Give them a shot.
You might be looking at the next great name in this space.
That's exactly what we are building toward.
A place where serious builders and auditors belong.
It's one of our biggest visions.
Are you one of them?
English

@ighodarod95 That feeling is more common than people admit. What stage are you at right now, still learning or already doing contests?
English

@seeksahib Strong point.
Another pattern we see:
Teams focus on building fast,
but don’t think enough about trust.
Demand gets users in,
but reliability is what keeps them.
English

Vibecoding made everyone a builder.
But why are you building in Web3 at the first place?
If you can't answer this clearly... you aren't ready.
We're seeing more early-stage projects than ever.
The common reason of failure of all these projects is
a) not enough demand
b) no strong reason to pick them over others
Don't start a Web3 project, just because it sounds cool and fancy.
English

@volo_sui Incidents like this are a good reminder that security isn’t just about smart contracts.
Operational layers, especially key management, often become the real point of failure.
Appreciate the transparency here.
English

📋 Community Status Report - Volo Protocol
We want to provide our community with a full and honest account of where things stand following yesterday's security incident.
We owe you clarity, and we are committed to providing it every step of the way.
1. Cause of the Hack
Our investigation is ongoing, and we do not want to speculate on details before we have a complete picture.
What we can share at this stage: we believe the attack was the result of a private key compromise.
Despite our best efforts and security practices in place, the attacker was able to exploit this vector to access the affected Vaults.
This was not a smart contract vulnerability or a protocol-level exploit; the Sui blockchain and its infrastructure performed as intended throughout.
A full technical post-mortem will be published once the investigation is concluded. We are working with security partners to ensure this cannot happen again.
2. Fund Recovery - $2M Successfully Frozen
Of the ~$3.5M in assets taken, we have successfully frozen approximately $2M in close coordination with the Sui Foundation and ecosystem partners. This was the result of a rapid, round-the-clock effort from our team and the broader ecosystem.
We are continuing to work through the details of the recovery and return process with our partners during EST business hours on Wednesday. A further update will follow as soon as those discussions are concluded.
3. Making Users Whole - We Are Fully Prepared
For the remaining ~$1.5M, we are fully prepared to make every affected user whole. No user will be left out of pocket.
We know that a promise alone is not enough - we will be communicating every step of the process transparently before funds are returned, so you know exactly what is happening and when.
Details on the reimbursement process will be shared shortly.
We are deeply sorry this happened. The Volo Team is working without pause to resolve it and to rebuild the trust you have placed in us.
Thank you for your patience and continued support.
English

@ClayTrop Appreciate that. That’s exactly what we’re trying to build, step by step.
Still early, but we’re getting there.
English

@ForgeAudit This hits.
As a builder, I’ve seen how many great ideas stay hidden just because the right doors never opened. We need more spaces like this.
English

@Abdulrahee84158 Exactly. By the time it's 'after launch', the window is already open.
English

Shipping pressure is real. Deadlines are real. Investor expectations are real.
So is the exploit that comes after.
Most protocols that got drained weren't built by careless teams.
They were built by talented people under pressure at launch, at upgrade, at every new integration.
Security isn't a one time checkpoint.
It's the work that never stops.
The window between deployment and exploit doesn't wait for your roadmap.
If you're still building, one piece of advice :
make security part of the process now.
Not after the audit request. Not after the incident report. Now.
English

@Param_eth Single point of failure at the verifier level. The exploit didn't break the system, it used it exactly as designed. That's the harder lesson.
English

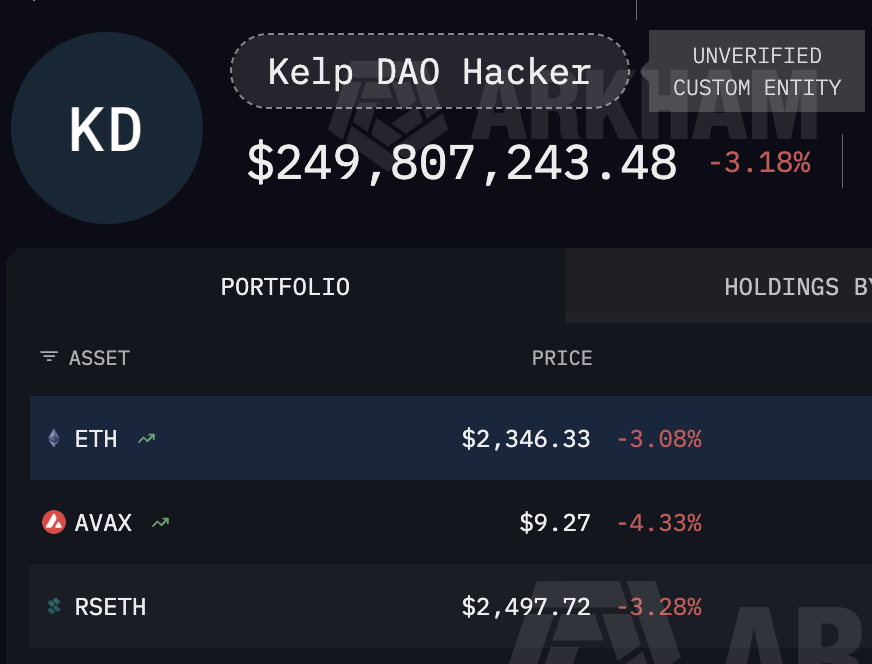
Everything you need to know about the rsETH exploit ($292 million):
attacker targets insecure bridge configuration
Verifier setup:
Only one approval is required, and this is the single point of failure.
Attacker forges cross-chain message.
Tricks Bridge into Release:
116,500 fake $rsETH worth ~$292 million
About 36% of total supply
Unbacked ETH tokens created from thin air by the attacker (minted)
Attacker receives fake rsETH on
Ethereum
Immediately deposits it into Aave as collateral
then borrows:
106,467 ETH (~$250M)
Started selling and swapping rsETH.
bad debt created of more than $177 million.
WETH pool utilisation hits 100%
Aave freezes rsETH market
exploit was not in core rsETH backing
exploit hit bridged rsETH version
attacker wallet publicly tracked
funded via Tornado Cash
one of the biggest bridge failures of 2026
English

The oracle wasn't broken, it read what was there.
The attacker deployed fake token contracts, wired them into a cluster of freshly created pools, and built a synthetic liquidity graph around attacker controlled assets.
Any validation logic that trusted those pools without questioning asset legitimacy got misled.
The gap wasn't oracle sophistication.
It was asset admission.
English

@ForgeAudit @CertiKAlert @rhea_finance this part baffles me, wouldn't it need to be pretty sophisticated to fool oracles?
English

#CertiKInsight 🚨
We have seen an incident affecting @rhea_finance
The attacker created fake token contracts and added liquidity in fresh pools, likely misleading the oracle and validation layer.
In total, at least ~$7.6M was extracted
nearblocks.io/address/31ac7a…
English

$7.6M left Rhea Finance.
No cryptography was broken.
No zero day exploit.
The attacker created fake tokens,
spun up fresh liquidity,
and fed the system inputs that looked valid.
And the system accepted all of it.
Real assets.
Fake inputs.
No resistance.
This didn’t start in the contract.
It started at asset admission.
And that’s where the next one will start too.
English

@DriftProtocol @tether Respect to the Drift team for putting together this recovery package for the users.
Wishing you all the best on the relaunch and rebuilding stronger
English
Today, Drift is announcing a collaboration with @tether and other partners totaling up to nearly $150 million to support our commitment to a relaunch with USDT at the center, and a path to user recovery.
These funds encompass a $100M revenue-linked credit facility, an ecosystem grant, and loans to market makers, designed to fund a dedicated user recovery pool.
Learn more 👇
English

For a long time, most security effort in DeFi focused on smart contracts, and for good reason, because that’s where critical bugs lived. That hasn’t changed.
We still see the same edge cases, the same assumptions, the same overlooked paths. But lately, something else keeps showing up, not inside the contract, but around it. Frontends get spoofed, APIs return manipulated data, users sign things they don’t fully verify.
The contract can be correct, and the system can still fail. Because security doesn’t stop at the code, it extends to everything that interacts with it.
The attack surface didn’t shift, it just turned out to be bigger than we thought.
English

@trench_boe Exactly. And that dismissal is the real vulnerability. Not in the code, in the decision to ignore the warning. No exploit ever waited for the protocol to take security seriously.
English

@ForgeAudit When you give them an alert, they think you are too small for this until they lose everything
English

@ForgeAudit Completely agree. The industry still relies on one-time assurance for systems that change daily.
That’s why we focus on continuous, adversarial testing at TestMachine.
English


