Skadz
162 posts
@DeniCodes @zeroxjf Wanna know too , asked several times but no answer. Most people said ios 18.4-ios18.7, but i think should work on ios 18.1
English

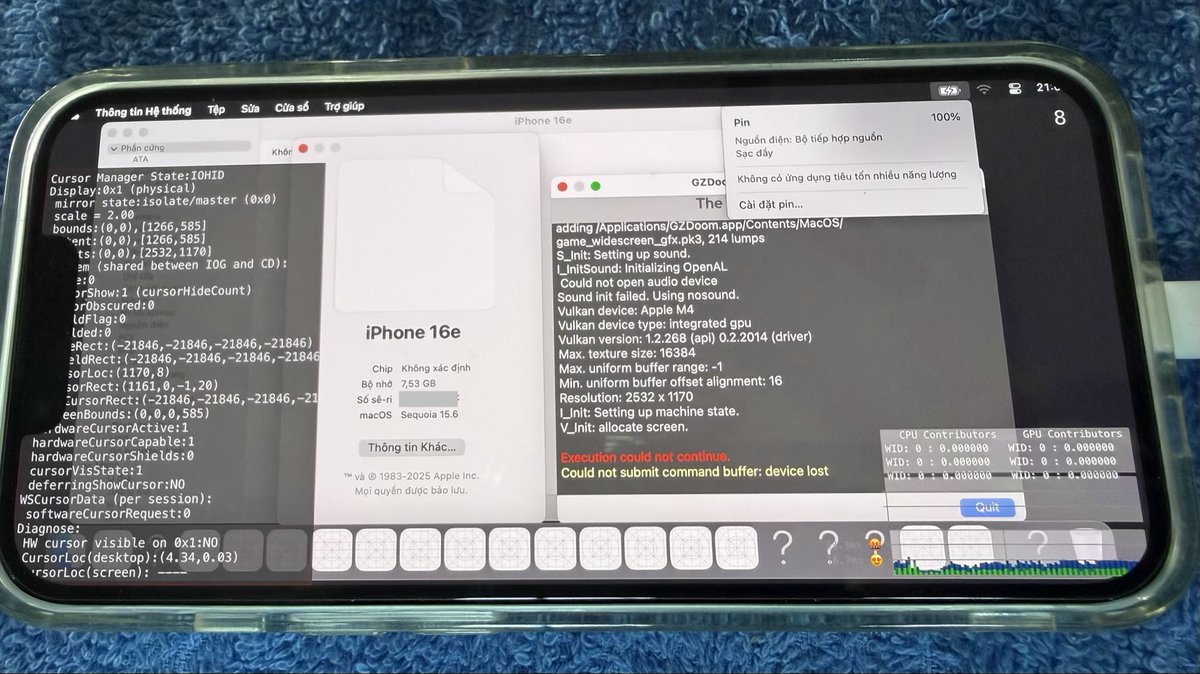
Thanks to a tip from @khanhduytran0, I now have the extracted DS files getting dumped to /private/var/mobile/Media/Downloads/ in lieu of the highly unreliable remote server communication.
I also now have the full chain repro up to 60-70%!
johnny@zeroxjf
Post-exploit data theft
English

@amfi_d this might sound dumb but is there any hope for people(me) on 18.0.1 (below 18.4)?
English

@mattiekool Yes, with remnants of 18.6 code. But it's the full chain and could likely be adapted to any susceptible version with some adjustments
English
@Little_34306 @zeroxjf If ios >=18.4, so means not work with ios 18.1 ?
English

How crazy Darksword and GHOSTBLADE are!
shout out to @zeroxjf for the finding
Unrelated: GHOSTBLADE also my fav comic from WLOP!


English

@Forkazmodan Well. There's no mention about that ios version.
English

iOS 18 jailbreak… might not be that far.
Coruna already proved:
• Tweak injection works
• .dylib loading works
• System UI can be hooked
Now DarkSword adds:
• Website-based exploitation
• Fileless execution (no install needed)
• “Smash-and-grab” data extraction in minutes
• Works just by visiting an infected page
• Targets real devices at scale
It can access things like:
• Messages (iMessage, WhatsApp, Telegram)
• Photos and files
• Browser data
• Even sensitive app data
And the scary part:
The exploit chain was left exposed.
Meaning it can be reused.
If these get combined…
we could see a Coruna-level jailbreak for iOS 18.
And this time?
No cables. No sideloading.
Just a webpage.
Exploit News Source : Wired

English

Wild couple weeks for the iOS jailbreak community.
2 exploit chains in 2 weeks. ICYMI, there’s a new iOS 18 chain (details below). Payloads don’t appear to be in the wild, (good given how many are still on iOS 18), but likely means no imminent ability to adapt for a jailbreak.
Mateusz Krzywicki@krzywix
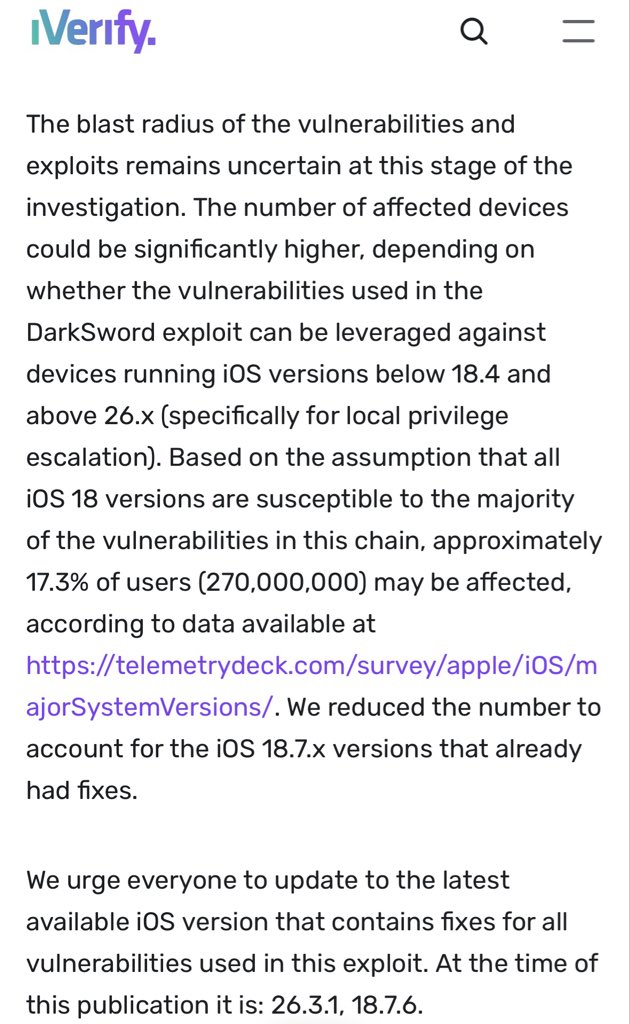
In collaboration with Lookout and Google (thank you 🙏) we have been working on tearing down and building detections for DarkSword - iOS exploit chain for iOS 18.4 - 18.7. Super excited for this research 🎉. Please update your iPhones. iverify.io/blog/darksword…
English

In collaboration with Lookout and Google (thank you 🙏) we have been working on tearing down and building detections for DarkSword - iOS exploit chain for iOS 18.4 - 18.7. Super excited for this research 🎉. Please update your iPhones.
iverify.io/blog/darksword…
English

New ITW kernel exploits for more recent iOS versions. RIP I already updated to 26.1 for obviously stupid reason :/
Mateusz Krzywicki@krzywix
In collaboration with Lookout and Google (thank you 🙏) we have been working on tearing down and building detections for DarkSword - iOS exploit chain for iOS 18.4 - 18.7. Super excited for this research 🎉. Please update your iPhones. iverify.io/blog/darksword…
English

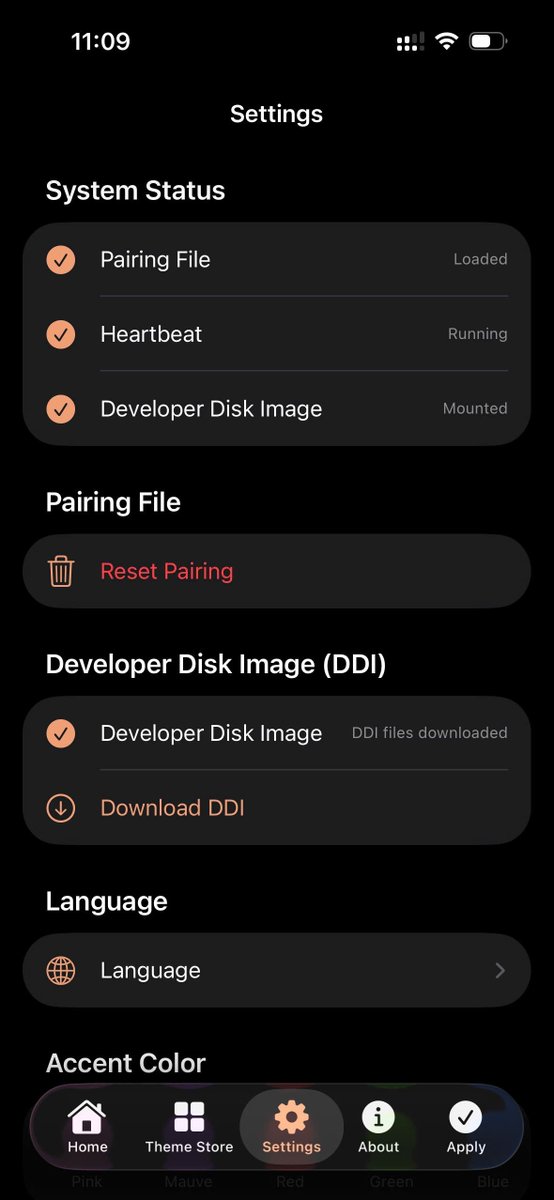
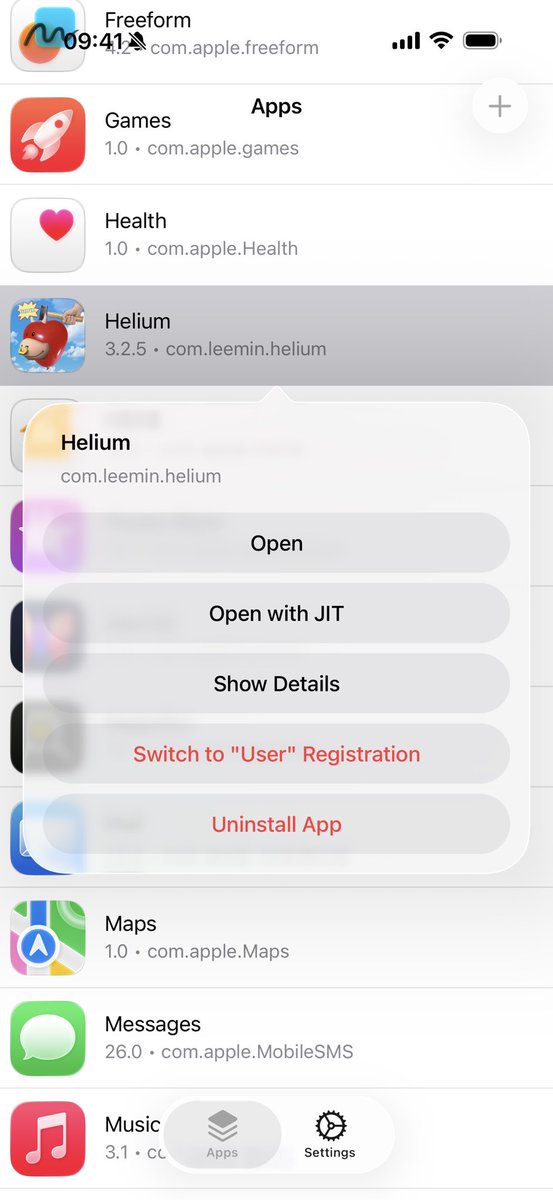
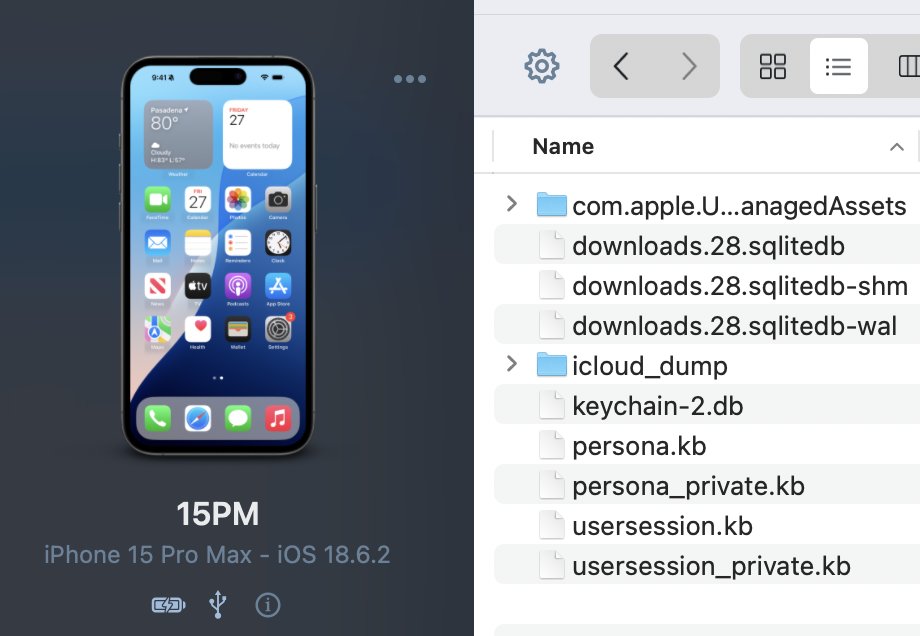
@Little_34306 @khanhduytran0 fyi people: this is an internal device. trollstore will never ever come to ios 26 on regular devices.
in my personal opinion, this whole saga is incredibly misleading and is just a bunch of clout-chasing engagement bait, but last time i said that i got flamed so.. good job
English


@khanhduytran0 how? i thought it required a jailbreak but there aren’t any jailbreaks for the iphone 16e
English
@skadz108 @Little_34306 @khanhduytran0 Is there any chance of change our phone into AI device with book exploit?
English

@Little_34306 @khanhduytran0 genuinely what is the point of hyping this up if not to mislead people for clout
what's even the point of releasing this? the only people that'd be able to use this are people you could likely just hand this to if needed, there's zero need for this to be public.
English

With @khanhduytran0's "AI" device release, here's a TrollFools fixed for iOS 17.5.1-
I'm planning to make it support on higher iOS "AI" device since start from iOS 17.6 Apple did a thing
place ldid into /var/jb/usr/bin/ldid to make sure it works fine
github.com/34306/TrollFoo…
English