Geiseric
203 posts
Geiseric
@Geiseric4
AD/Azure Enthusiast | eCPPTv2 | CRTP | CRTO | CRTE | CRTM | CARTP https://t.co/yYy84cNFPw
Katılım Şubat 2022
160 Takip Edilen911 Takipçiler

Giveaway.
Thank you @mrd0x for sponsoring this.
We've got FIVE @MalDevAcademy vouchers. These vouchers are bundles. This vouchers give you:
- Full access to malware source code database
- Full access to malware development course
Comment below for a chance to win.
English

Giveaway.
@Octoberfest73 has sponsored two Zero Point Security "BOF Development & Tradecraft" courses.
tl;dr Training course on Cobalt Strike and malware C2 stuff.
Leave a comment below for a chance to win.
Course information: zeropointsecurity.co.uk/course/bof-dev
English

Hello.
I have partnered with @cyberwarfarelab to give away FOUR HUNDRED (400) vouchers to their Infinity Learning Pro Plan. This is worth $119,600.
- 130+ hands-on labs, including advanced attack chains
- Unlimited challenge time
- Monthly new challenges & scenario updates
- Leaderboards for nerds
- ???
This is a massive giveaway. How to enter:
1. You NEED a Gmail account. IF YOU ARE SELECTED AS A WINNER authentication is performed via Gmail. It does NOT have to be your real Gmail. It can be a disposable email. However, if you DO NOT have a Gmail you WILL NOT be able to authenticate.
2. This is a pit of doom. You're all fighting. Leave a comment below with an IMAGE of your SILLIEST weapon of choice.
3. This giveaway will be active for the next 48 hours (unless I get bored). It is November 30th, 2025. If you comment AFTER December 2nd, 2025 then you're a big stinky nerd. You have missed the pit of doom.
4. Winners will notified by me commenting your comment. If you do not respond to the DM within 24 hours (if you're selected) you forfeit your win and someone else is chosen. PAY ATTENTION.
Good luck in the pit of doom. Have fun. I expect lots of laughs from the silliness.
Cheers,
English

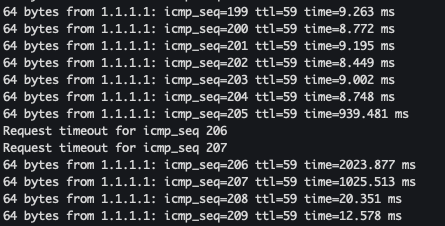
I just solved the strangest tech problem I've ever come across.
My wifi kept dropping packets, confirmed by ping. It would look something like the first image (packets dropping, then it comes back to life). After a while the connection would just stop working completely and drop all packets. If I turned my wifi off and on again, it would resume working normally.
I thought this was a problem with my router, cables or ISP, so I went through the usual troubleshooting processes: checking settings, swapping cables, powercycling, etc. nothing worked.
Eventually I started noticing that it would only happen when I sat in my office. I was taking a video meeting and it kept dropping segments of audio, making it hard to understand the other person.
I unplugged my laptop from my monitor + keyboard because I wanted to try walking into another room. Immediately, the video started working perfectly.
I thought it was because I was a few steps closer to my router - but that didn't really make sense because the router had always worked fine from that location.
I started thinking about what I'd changed in my desk setup recently, the only thing I could think of was when I changed from using a USB-C <-> DP cable for my monitor, to using a HDMI <-> HDMI cable.
I tried plugging my screen back in. Immediately, the packets started dropping. I unplugged it, the dropping stopped.
It turns out my HDMI cable doesn't have enough shielding, so it was jamming my own WiFi signal with radio frequency interference 🤯
I unrolled the HDMI cable that was sitting behind my laptop and draped the main length of the cord down behind my desk, and now my internet works perfectly.
Apparently this is a fairly common issue?!
English
Geiseric retweetledi

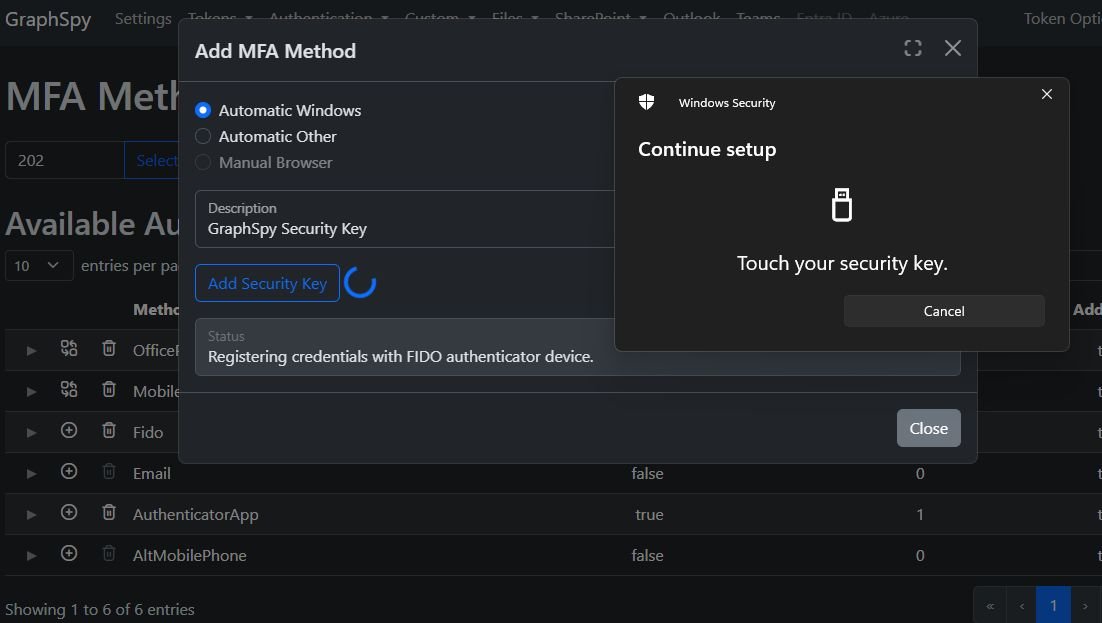
📧 GraphSpy 1.5.0 is out now and brings a brand new Outlook Graph module!
✅Read emails in any folder
✅Send HTML-formatted emails directly in GraphSpy
✅Access shared mailboxes
✅Search for sensitive information like passwords
🔗Check out GraphSpy here:
github.com/RedByte1337/Gr…


English
Geiseric retweetledi
Geiseric retweetledi

GraphSpy just hit 600 stars on GitHub after releasing version 1.4!✨
This version introduces the new Entra ID module, better loading animations, and JSON syntax highlighting.
Check it out here:
github.com/RedByte1337/Gr…



English

I just pwned Vintage in @hackthebox_eu! This is indeed a hard box. I had repeated issues, hitting brick walls etc. The creator, @Geiseric4, did a good job restricting and guiding the player when designing it. #HackTheBox #htb #CyberSecurity #EthicalHacking #InfoSec #PenTesting
English
Geiseric retweetledi

Old but gold 🏅
Vintage created by Geiseric will go live on 30 November 2024 at 19:00 UTC. Lantern will be retired!
✔️ Hard
✔️ Windows
→ Choose your Machine and start #hacking: okt.to/BkgKWo
#HackTheBox #HTB #CyberSecurity #NewRelease

English
Geiseric retweetledi

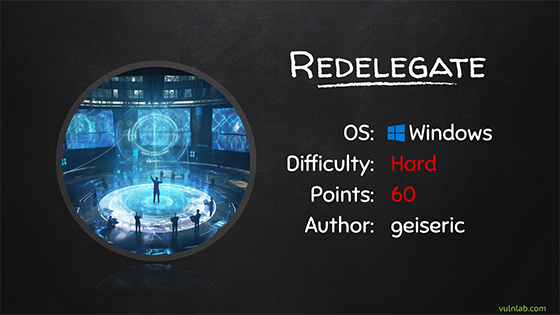
Time to dive into Active Directory again - Redelegate by @Geiseric4 will be released on Thursday!
English
As many others did, I also created a BlueSky account, hopefully leaving this platform.
If you want to keep in touch bsky.app/profile/geiser…, see you there!
English
@jason_sarnoff Not really, I just wanted a place to regroup all the recent PRs.
English

@Geiseric4 Are you doing the same thing with certipy here github.com/GeisericII/Cer…?
English
Hello! This fork aims to be the most bleeding-edge, but of course it's not possible without your contributions. If you are making a PR to Fortra's Impacket, please mirror it here github.com/ThePorgs/impac…
Fortra=steady and stable, Porgs=BleedingEdge (less conflicts = quicker merge)
English

powerview.py now supports LDAP search filter, base dn and properties obfuscation. Supply --obfuscate flag and youre good to go.
(servicePrincipalName=*) is now ( seRviCePRincIpaLnAmE>===)

English
@filip_dragovic @BlWasp_ @rayanlecat Do you know if current tooling support relaying to HTTPS for ADCS? Like certipy/ntlmrelayx?
For SCCM I'm assuming it has to do with the newest version, I'm trying to download an older one
English

@Geiseric4 @BlWasp_ @rayanlecat yeah https without epa works , at least on adcs do not know about sccm but should work
English

@rayanlecat @Geiseric4 I haven't tested this version so far. But HTTPS without EPA should be good for a relay ?
English

Added new module to powerview.py to enumerate logon user via registry, Get-RegLoggedOn. Credits to @Geiseric4 and the original PowerSploit's script.
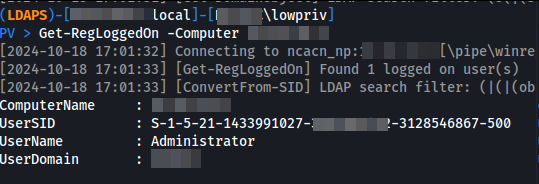
Geiseric@Geiseric4
Following @splinter_code idea, you can also start RemoteRegistry remotely. This way you can check on which server DAs are connected, in case you want dump their creds. This script could help: gist.github.com/GeisericII/684… It works from low privileged user 😉
English
Geiseric retweetledi

Congratulations to @Geiseric4 for clearing our Certified Azure Red Team Professional exam!
#AzADLab #CARTP #AlteredSecurity cc @nikhil_mitt
alteredsecurity.com/azureadlab

English
@theluemmel I've never used it but I can recommend @L3o4j tooling, he really knows his stuff
English

Did anyone of you folks already use github.com/Leo4j/Invoke-A…
It quite a lot of code I just now don't want to go through.
English