Sabitlenmiş Tweet

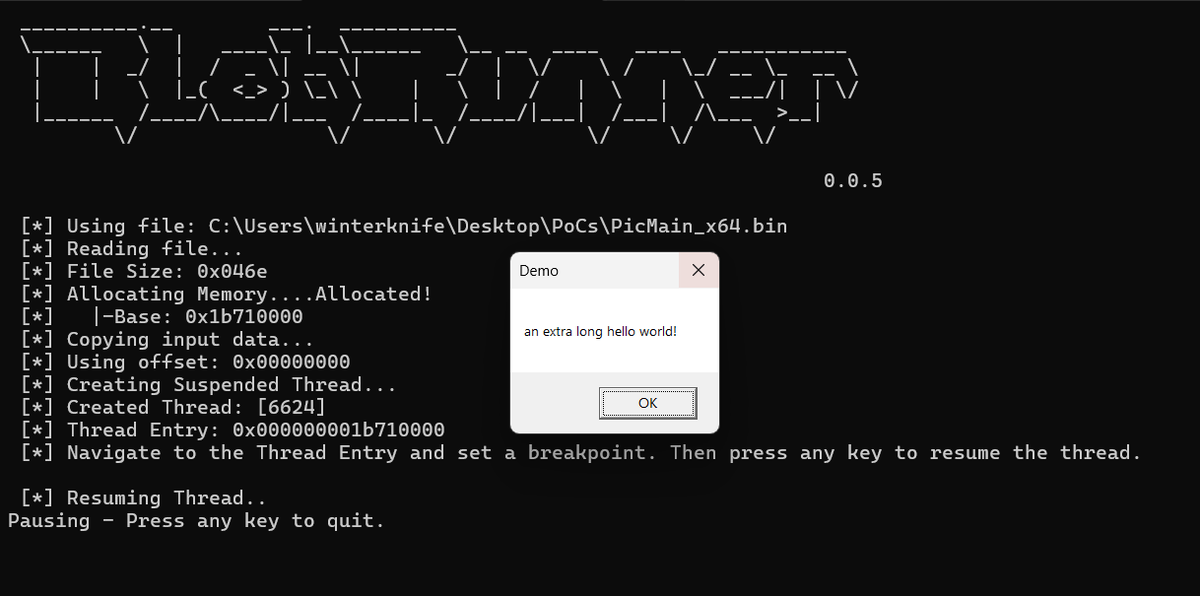
Releasing SILVERPICK, a Windows shellcode development framework using C/C++.
github.com/winterknife/SI…
English
winterknife 🌻
909 posts

@_winterknife_
low-level developer with a focus on 𝙸𝚗𝚝𝚎𝚕 𝚡𝟾𝟼 ISA devices running 𝚆𝚒𝚗𝚍𝚘𝚠𝚜 | R&D @BHinfoSecurity | https://t.co/lyJL0y7qRZ