How Axios was compromised 🤯
Joe Stocker
7.6K posts


@ITguySoCal
Christian Family Man, CEO of Patriot Consulting (Microsoft Security Partner) Author of "Securing Microsoft 365" Microsoft MVP (Security) (2020-2026)

How Axios was compromised 🤯

How Axios was compromised 🤯

Software horror: litellm PyPI supply chain attack. Simple `pip install litellm` was enough to exfiltrate SSH keys, AWS/GCP/Azure creds, Kubernetes configs, git credentials, env vars (all your API keys), shell history, crypto wallets, SSL private keys, CI/CD secrets, database passwords. LiteLLM itself has 97 million downloads per month which is already terrible, but much worse, the contagion spreads to any project that depends on litellm. For example, if you did `pip install dspy` (which depended on litellm>=1.64.0), you'd also be pwnd. Same for any other large project that depended on litellm. Afaict the poisoned version was up for only less than ~1 hour. The attack had a bug which led to its discovery - Callum McMahon was using an MCP plugin inside Cursor that pulled in litellm as a transitive dependency. When litellm 1.82.8 installed, their machine ran out of RAM and crashed. So if the attacker didn't vibe code this attack it could have been undetected for many days or weeks. Supply chain attacks like this are basically the scariest thing imaginable in modern software. Every time you install any depedency you could be pulling in a poisoned package anywhere deep inside its entire depedency tree. This is especially risky with large projects that might have lots and lots of dependencies. The credentials that do get stolen in each attack can then be used to take over more accounts and compromise more packages. Classical software engineering would have you believe that dependencies are good (we're building pyramids from bricks), but imo this has to be re-evaluated, and it's why I've been so growingly averse to them, preferring to use LLMs to "yoink" functionality when it's simple enough and possible.


🚨 Secure Boot 2026 is coming—and it’s not just another patch. Microsoft’s June certificate update impacts platform trust. Are your Windows endpoints ready? Join this technical session to learn how to assess & prepare with Intune. Register: lnkd.in/g8XBe2qT #secureboot




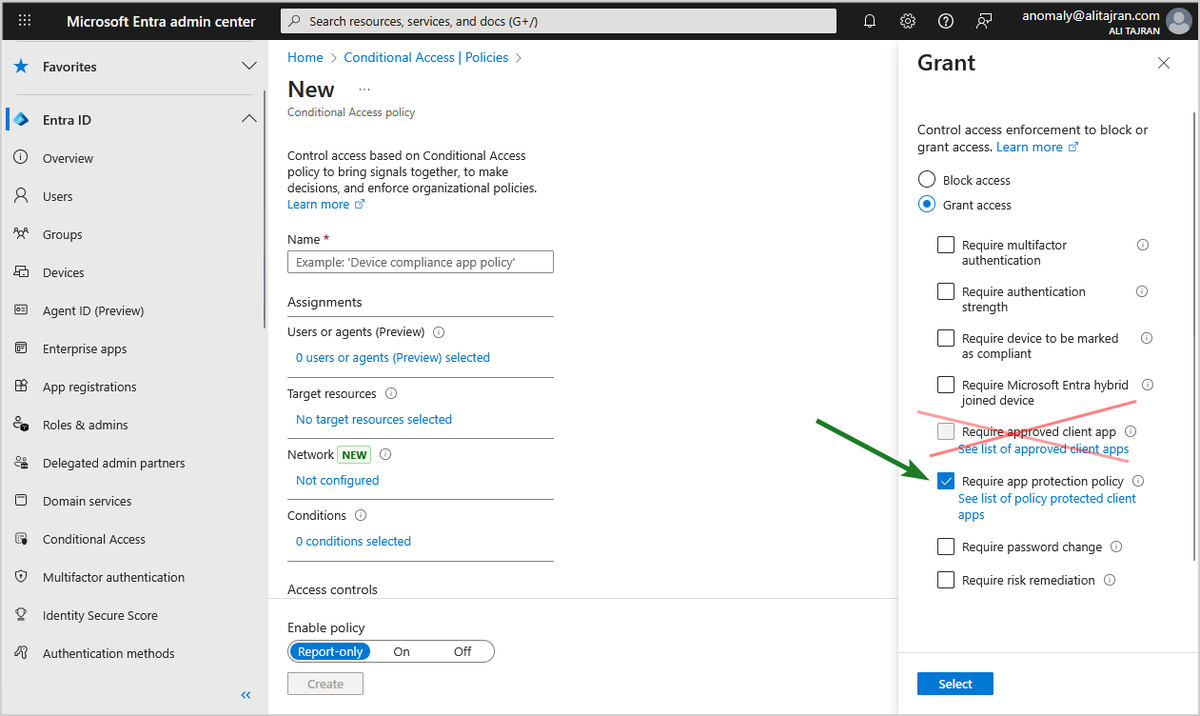

The "Require approved client app" control in Microsoft Entra Conditional Access will be retired in June 2026! Microsoft Entra ID and Microsoft Intune will retire the Conditional Access "Require approved client app" grant control in June 2026! Additionally, for any new Conditional Access policy, only apply the "Require app protection policy" grant. We recommend utilizing the "Require application protection policy" grant control, which provides the same data loss and protection with additional benefits. 𝐇𝐨𝐰 𝐭𝐡𝐢𝐬 𝐰𝐢𝐥𝐥 𝐚𝐟𝐟𝐞𝐜𝐭 𝐲𝐨𝐮𝐫 𝐨𝐫𝐠𝐚𝐧𝐢𝐳𝐚𝐭𝐢𝐨𝐧: If you have a Conditional Access policy with "Require approved client app" grant control configured, after this change, you will no longer be able to enforce this control, it will be as if this grant is not selected. 𝐖𝐡𝐚𝐭 𝐲𝐨𝐮 𝐧𝐞𝐞𝐝 𝐭𝐨 𝐝𝐨 𝐭𝐨 𝐩𝐫𝐞𝐩𝐚𝐫𝐞: We recommend updating your Conditional Access policy to use the "Require application protection policy" grant control. 1. Sign in to the Microsoft Entra admin center 2. Browse to Entra ID > Conditional Access > Policies. 3. Select a policy that uses the approved client app grant. 4. Under Access controls > Grant, select Grant access. 4a. Select Require approved client app and Require app protection policy 4b. For multiple controls select Require one of the selected controls 5. Confirm your settings and set Enable policy to Report-only. 6. Select Create to create to enable your policy. After confirming your settings using policy impact or report-only mode, move the Enable policy toggle from Report-only to On. #Microsoft365 #MicrosoftEntra