Amirabbas Ataei
598 posts


@ImAyrix
Bug Hunter & Web Application Pentester



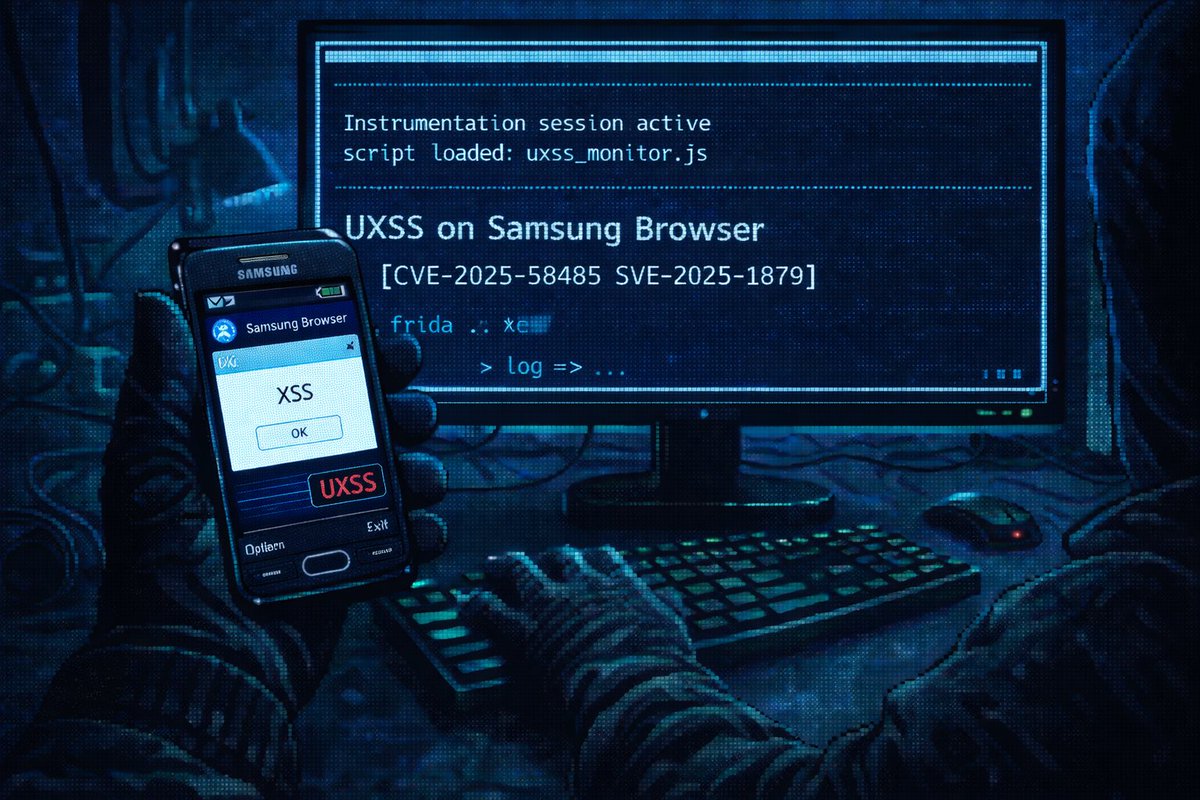
We got permission from the Samsung Security team to disclose this uXSS that we found in Samsung Browser, it was assigned a CVE (CVE-2025-58485) and patched. Here is the PoC, expect the write-up in the next upcoming days.

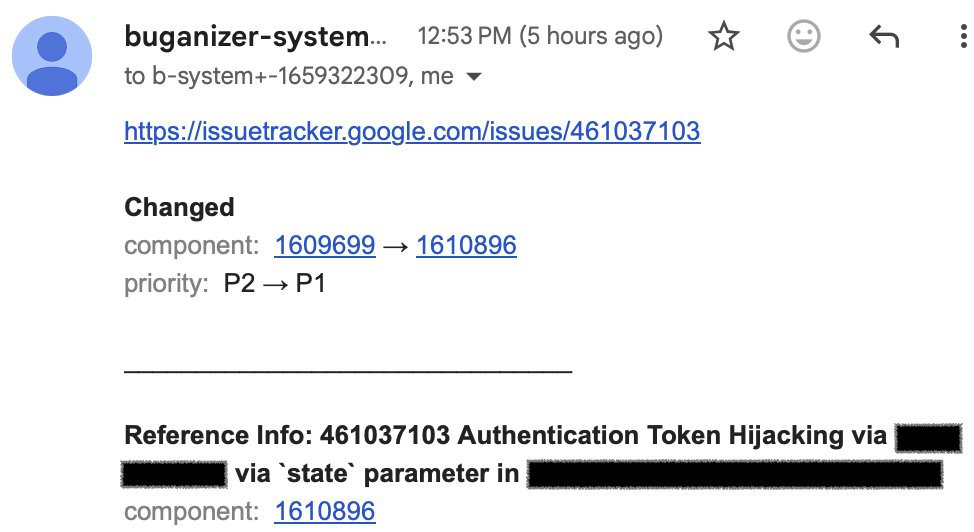
20 days ago I found a uXSS and reported, it got triaged now, I'll publish a blog post after fix and vendor permission, it's my first bug that I'm not happy with due to recent H1 situation 🖤


Yousef (@samm0uda) gave me a challenge few days ago, it's a redesign of Amir's recent challenge, the solution is quite interesting, I was able to solve it in 10 minutes as I'd previously debugged QS library it, I highly RECOMMEND it, the source code: gist.github.com/samm0uda/91efe…

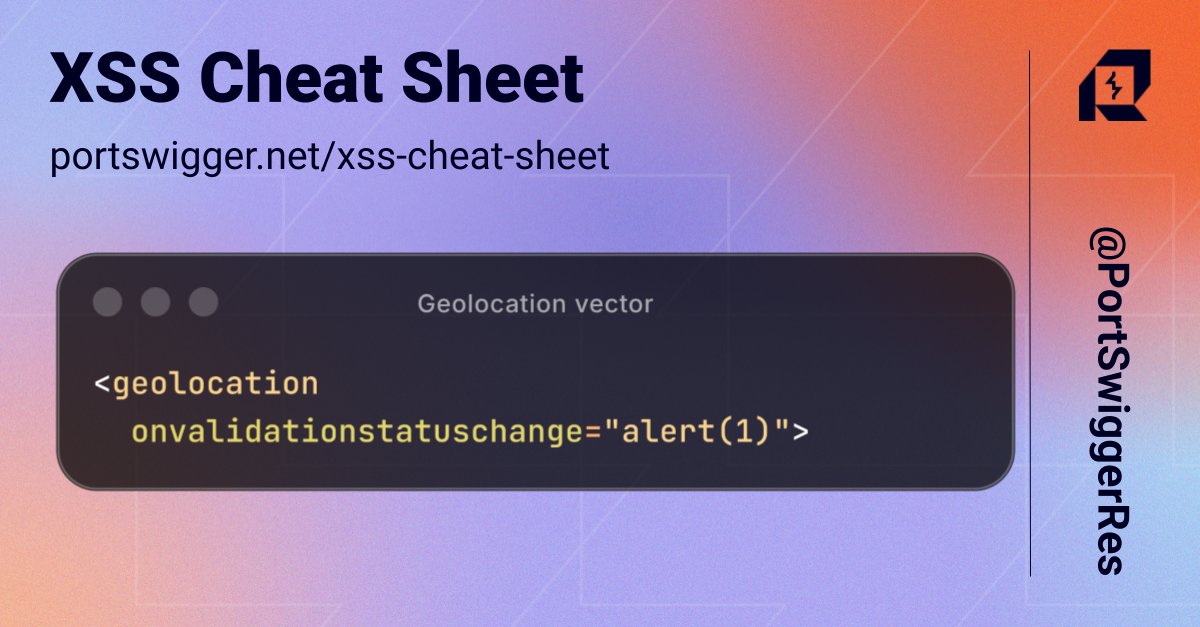
Can you spot the XSS vulnerability? 👀 Test it out live at: pwnbox.xyz