Rotimi Akinyele
905 posts

Rotimi Akinyele
@InfosecShinobi
The 1st Guy To Spawn A Backdoor Shell From Eggs. Infosec Guy. OSCE/OSCP/CRTE. Founder: PhynxLabs™, @NaijaSecCon, @NaijaSecForce. Likes == Bookmark
UAE Katılım Şubat 2012
461 Takip Edilen1K Takipçiler
Rotimi Akinyele retweetledi

Mon, 07 Oct 2024 17:27:00 EDT
A cybersecurity incident has been disclosed by ADT Inc. $ADT (CIK: 0001703056)
View SEC Filing: sec.gov/Archives/edgar…
English
Rotimi Akinyele retweetledi

Excited to announce the 🚀 launch of the 🔥 LOLESXi project. It provides valuable insights into adversarial techniques targeting VMWARE ESXi.
lolesxi-project.github.io/LOLESXi/ #threatresearch #lolesxi #dfir
English
Rotimi Akinyele retweetledi

Search engines for OSINT - Telegram Source
leak.sx
scylla.sh
intelx.io
4iq.com
leaked.site
hashes.org
leakcheck.io
vigilante.pw
leakcheck.net
weleakinfo.to
leakcorp.com
leakpeek.com
rslookup.com
snusbase.com
ghostproject.fr
leakedsource.ru
leak-lookup.com
nuclearleaks.com
private-base.info
haveibeensold.app
breachchecker.com
dehashed.com
scatteredsecrets.com
haveibeenpwned.com
haveibeenpwned.com
services.normshield.com
joe.black/leakengine.html

English
Rotimi Akinyele retweetledi
Rotimi Akinyele retweetledi

* Unauthenticated RCE vs all GNU/Linux systems (plus others) disclosed 3 weeks ago.
* Full disclosure happening in less than 2 weeks (as agreed with devs).
* Still no CVE assigned (there should be at least 3, possibly 4, ideally 6).
* Still no working fix.
* Canonical, RedHat and others have confirmed the severity, a 9.9, check screenshot.
* Devs are still arguing about whether or not some of the issues have a security impact.
I've spent the last 3 weeks of my sabbatical working full time on this research, reporting, coordination and so on with the sole purpose of helping and pretty much only got patronized because the devs just can't accept that their code is crap - responsible disclosure: no more.

English
Rotimi Akinyele retweetledi

Today, TrustedSec is releasing #Specula (our previously internal framework) into the world, which will transform the Outlook email client into a beaconing C2 agent. @oddvarmoe and @freefirex2 walk through how to use Specula in our latest blog! hubs.la/Q02JfFFN0
English
Rotimi Akinyele retweetledi

😱 Anyone can access deleted & private repo data on GitHub. Forever.
🔓This is due to a new type of vulnerability - CFOR
👎Deleted Fork Data: Still accessible.
👎Deleted Repo Data: Commits remain.
👎Private Repo Data: Can become public.
👉trufflesecurity.com/blog/anyone-ca…
English
Rotimi Akinyele retweetledi

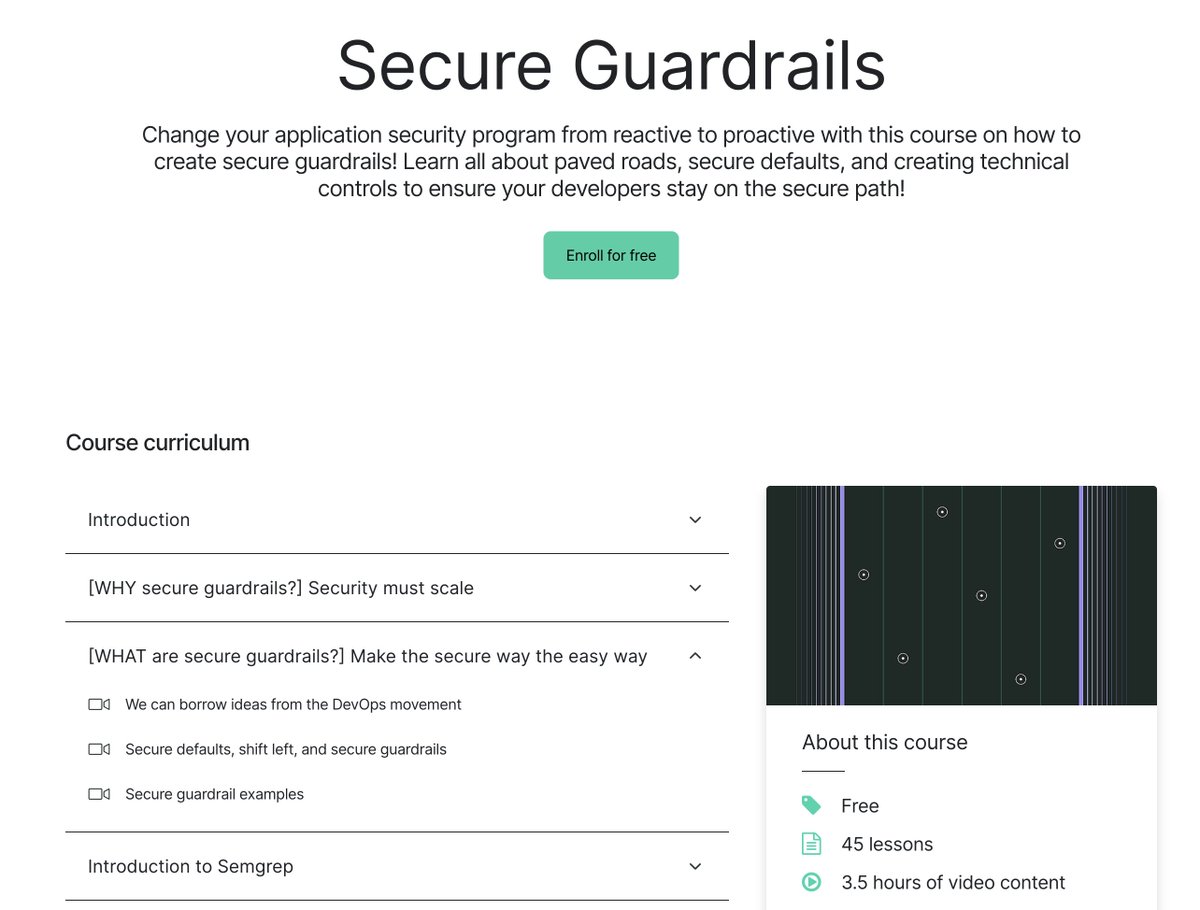
📖 New FREE Secure Guardrails Course
How to change your AppSec program from reactive to proactive using secure guardrails (making the secure way the easy way)
Lots of hands-on examples
45 lessons, 3.5 hours of video content
By @semgrep's @0xDC0DE
academy.semgrep.dev/courses/secure…
English
Rotimi Akinyele retweetledi

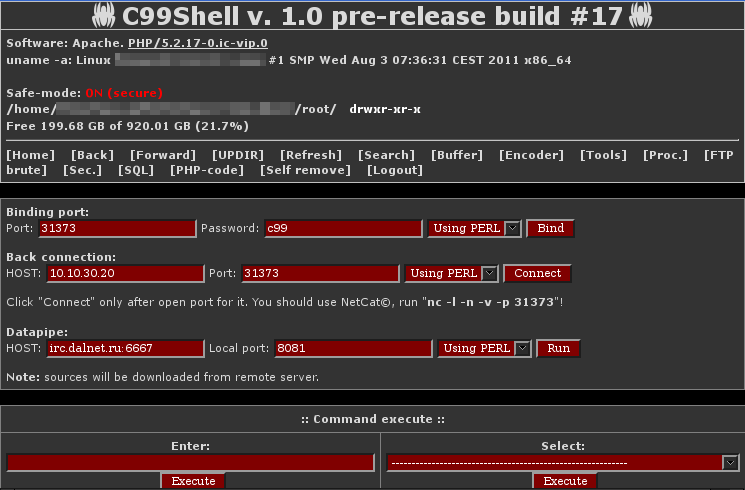
@Andrew___Morris Nolstalgic. Phplens, phploader, C99, r57, wso, br34k 😁 First steps to getting listed on Zone H 😁
English
Rotimi Akinyele retweetledi

Lol, best solution is to wake up from the nightmare 😅
eyitemi@eeyitemi
Happy holidays folks. Saw this note from an Incident response tabletop exercise I organized in 2018. My infosec people how do you handle this scenario? What do you do? Where do you start from? Which of these would be your priority?
English
Rotimi Akinyele retweetledi

Interesting usecase
eyitemi@eeyitemi
I told OpenAI to do find vulnerabilities in a C++ snippet.
English
Rotimi Akinyele retweetledi