Sabitlenmiş Tweet

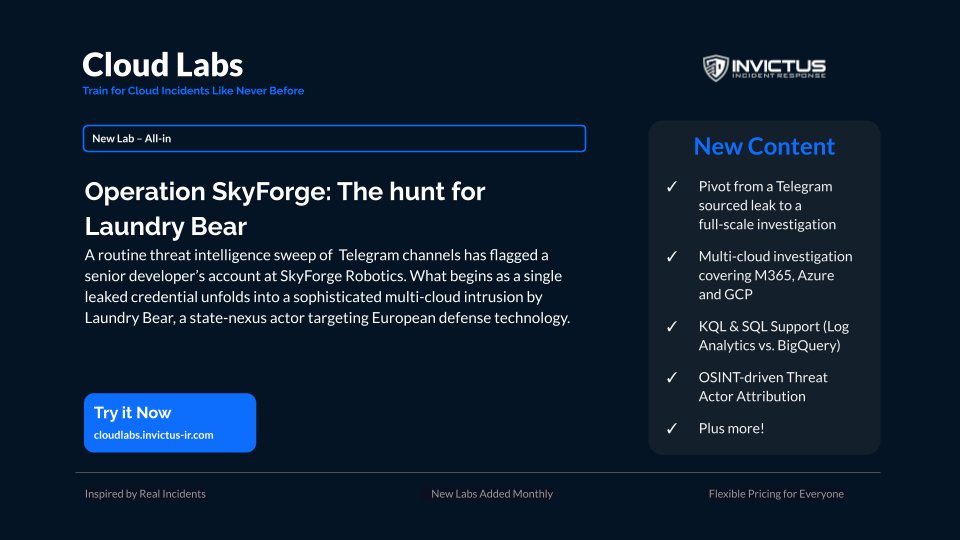
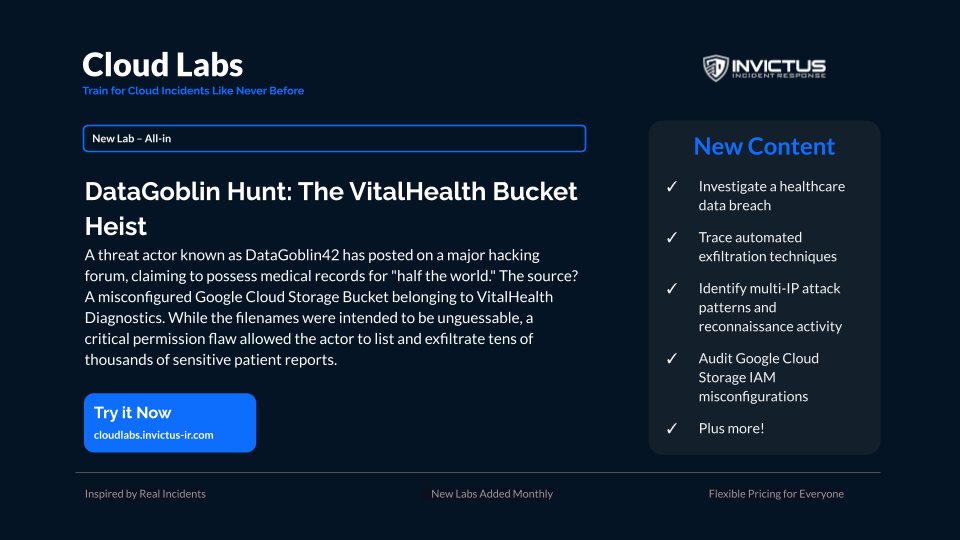
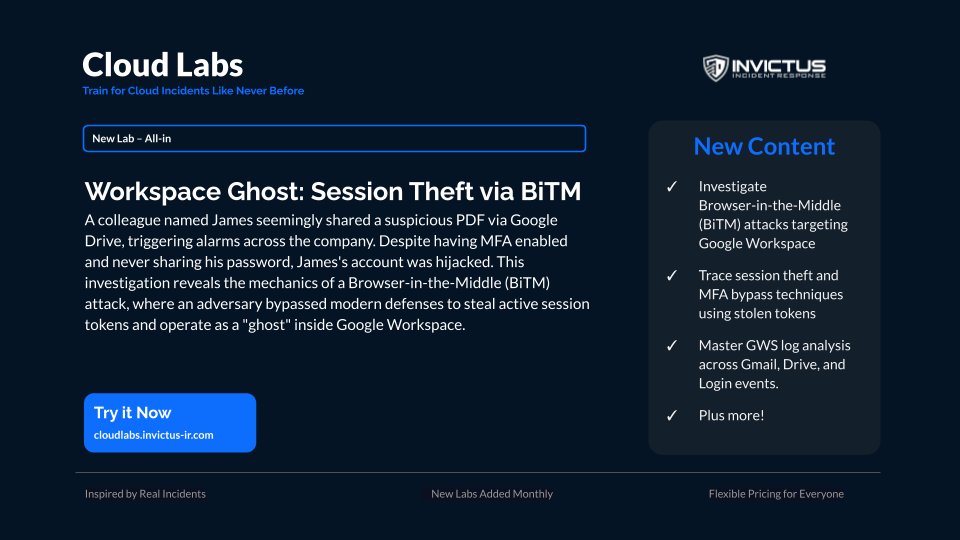
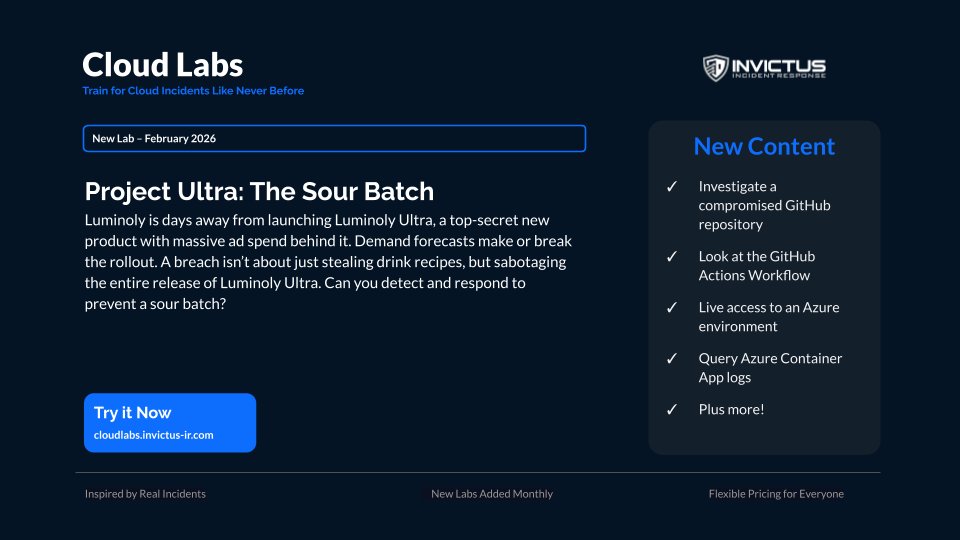
💥 𝐂𝐥𝐨𝐮𝐝 𝐋𝐚𝐛𝐬 𝐢𝐬 𝐥𝐢𝐯𝐞!
🏗️ A hands-on lab environment to practice your cloud incident response skills.
cloudlabs.invictus-ir.com
We're also doing a giveaway here, to enter:
1. Like this post
2. Comment why you want to have access
(Winners announced Monday September 1)
#stayInvictus #CloudLabs #CloudIncidentResponse

English