J.A.
28 posts


J.A.
@Jalbrec4
Security Researcher at Lookout, staring into the middle distance. Opinions are my own.





🚨New Partnership Announcement!🚨 All students will receive enhanced access to @Validin providing improved hunting capabilities. Upcoming training on Validin and real-life use cases tracking threat actors are on the way! inc. dedicated Discord channel for Validin. 🔥🔥🔥








Beware, WeChat users! LightSpy APT is targeting you to steal payment data. Stay vigilant and secure your online transactions @The_Cyber_News Discover more: gbhackers.com/lightspy-apt-a… #cybersecurity #onlinesafety #WeChat #paymentfraud




Unterdrückung in China: Investoren fordern Untersuchung von Volkswagen-Geschäften in Uiguren-Region – Der Spiegel spiegel.de/wirtschaft/unt…

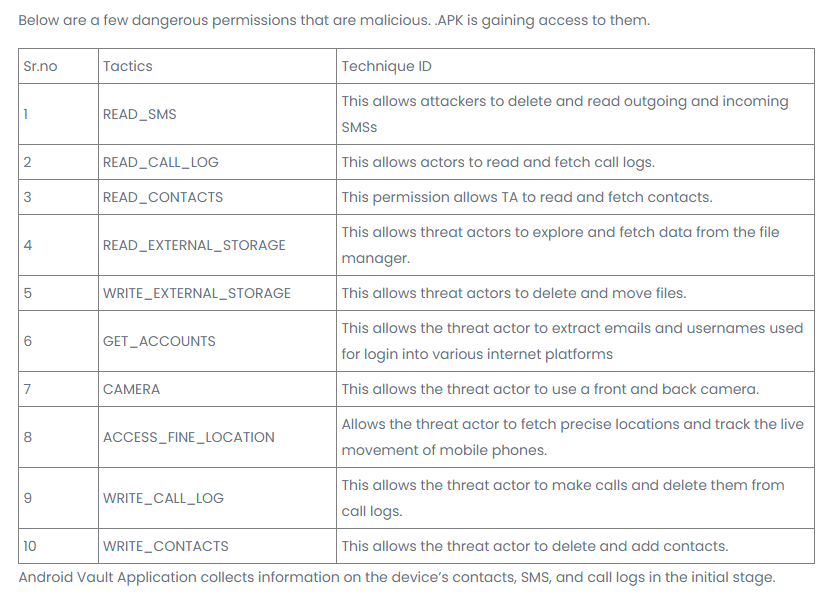
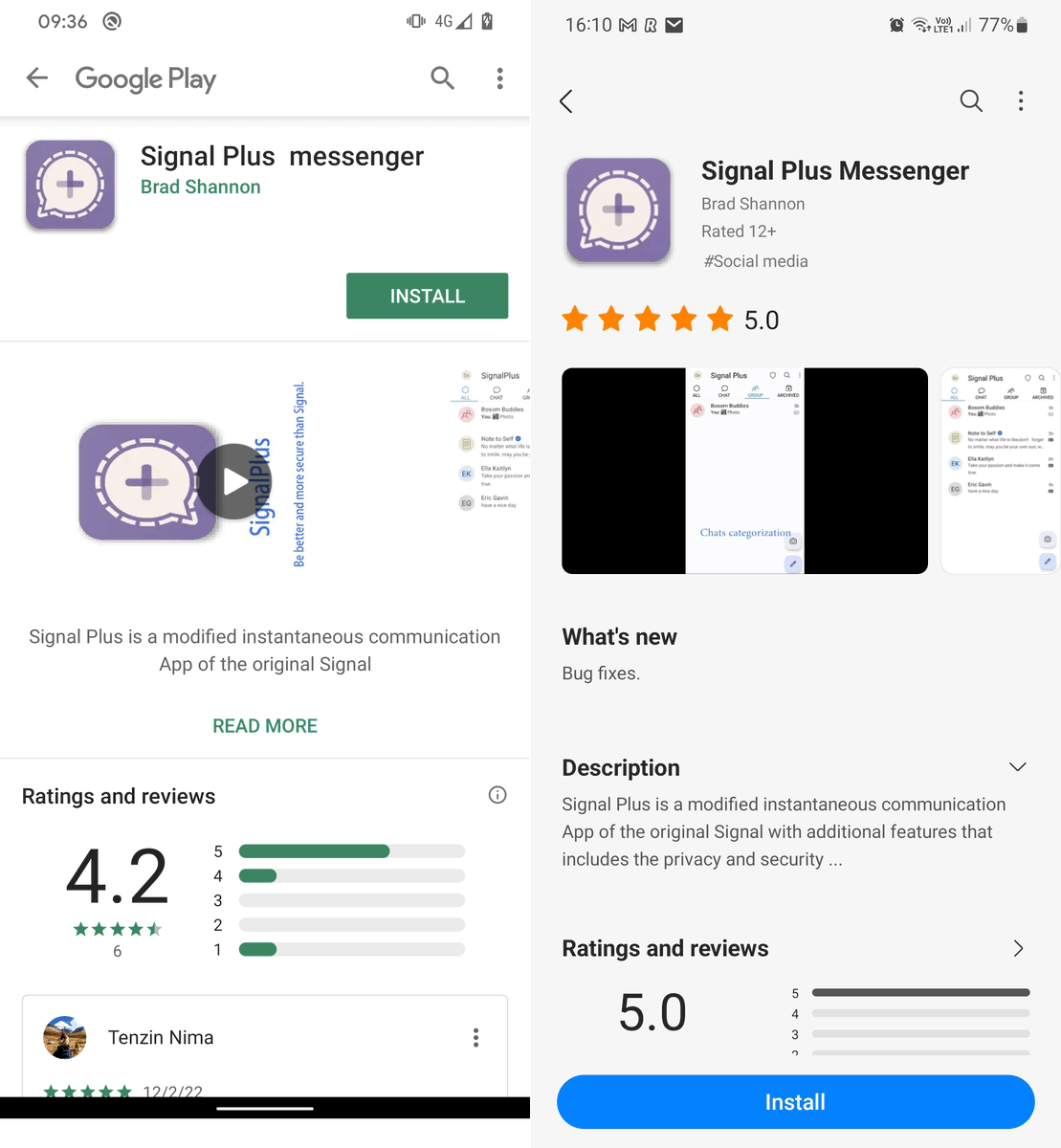
BouldSpy: A New Android Surveillance Tool zimperium.com/blog/bouldspy-…