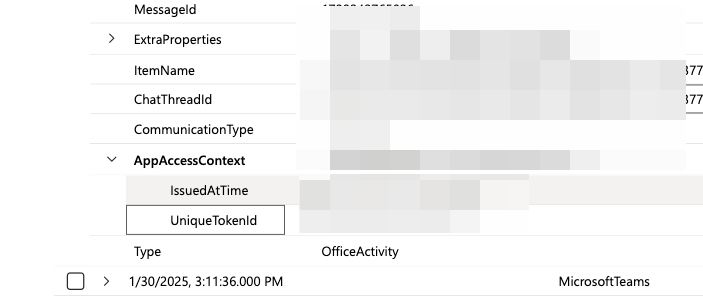
Sentinel analytics rules have _SentinelHealth() for failure monitoring. Defender XDR custom detections have... nothing. No table, no native alerting. Just the GUI. How is everyone catching these silent detection failures? @msftsecurity #MicrosoftDefender
English