


Kagame Opana
453 posts


@KagameO01
Tech Enthusiast😃 || Spray and Pray






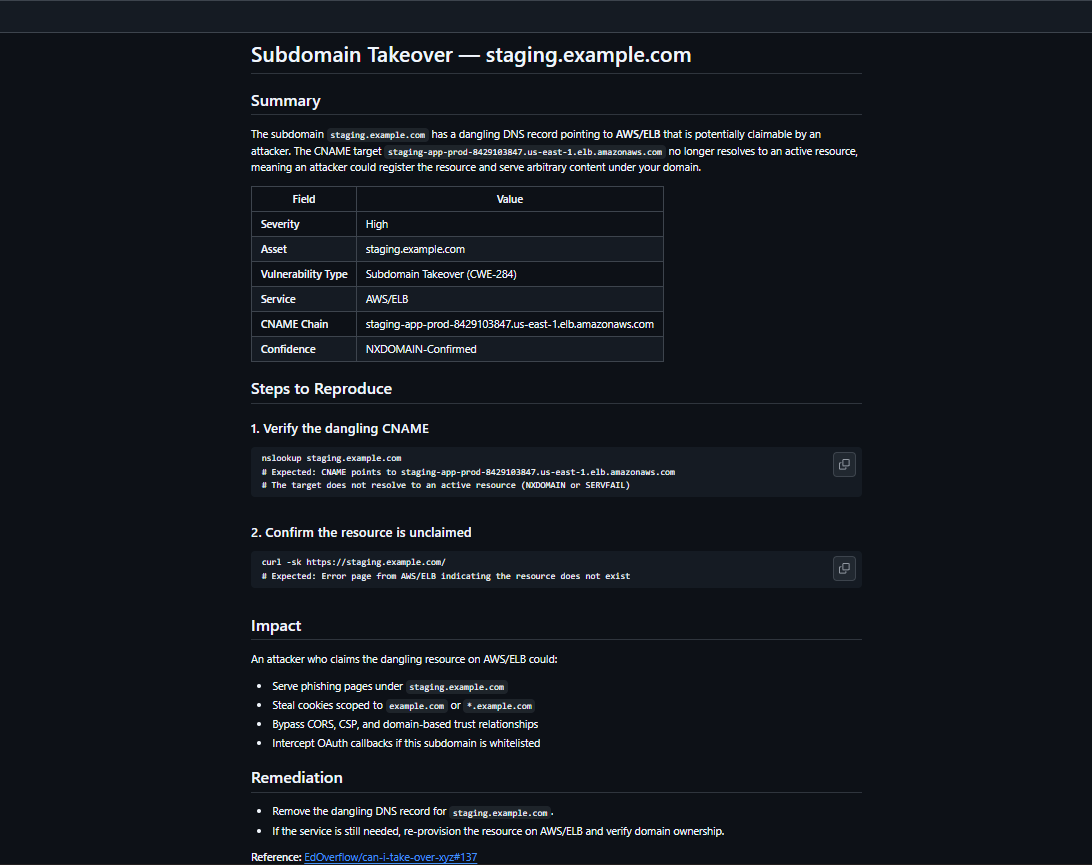
if my tool wasnt real this wouldnt be possible lol here is the proof output too github.com/Unit-259/subEn… 🎵 thats right. I am your god now bow to me 🎵

Remember this? Thanks to @Jhaddix we now have FIVE courses to give away for @the_IDORminator course on @arcanuminfosec So this Valentines day, to win 1 of 5 codes, I want you to write why this course would mean so much to you. Rules below in post 2/2




I hate this kind of attitude that @the_IDORminator is getting! Ive been a professional hacker for 30 years, old enough that I don’t need to buy courses, but smart enough to know I don’t know everything. There is always something to learn! So im going to buy 2 and give one away!







ELON WANTS TO REPLACE PLANES WITH ROCKETS SpaceX’s Starship could take you from New York to Sydney in under an hour. It skips jetlag by literally launching you into space and back down somewhere else. It’s like teleportation but with fire and Elon energy. Would you ditch planes for rocket rides? Source: Technology

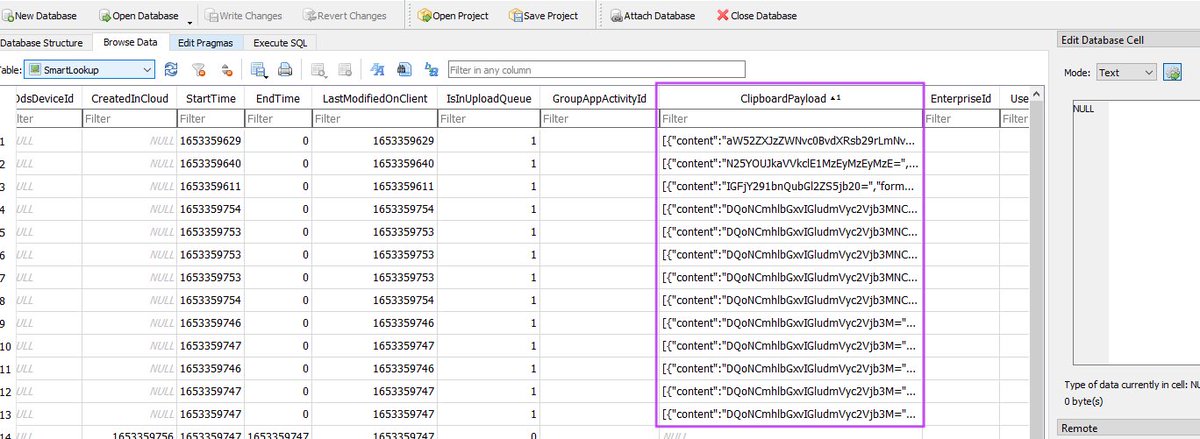
Most red teamers ignore the clipboard. You can pull: – VPN creds – MFA tokens – AWS keys – Password manager dumps All from CTRL+C. Nobody checks it. Nobody clears it. But it’s always there. Use it. 👊🏾






